Killings, Torturing, and Smuggling: How an Infostealer Exposed an ISIS Cell’s XMPP Network
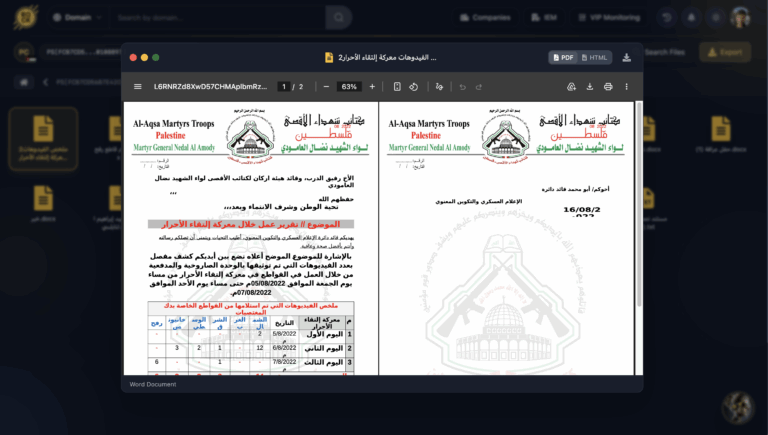
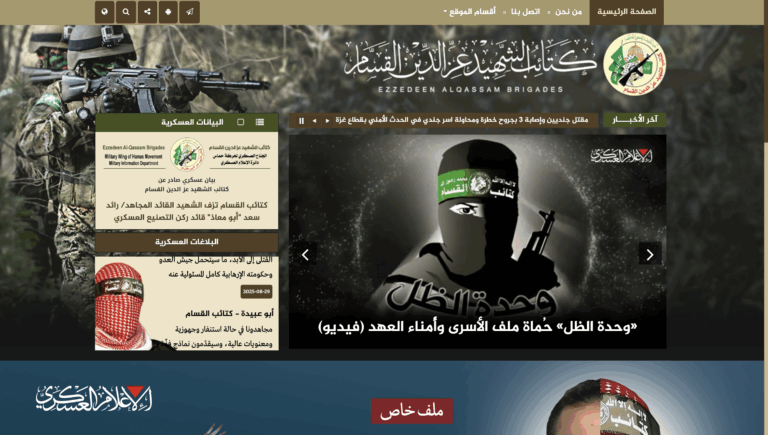
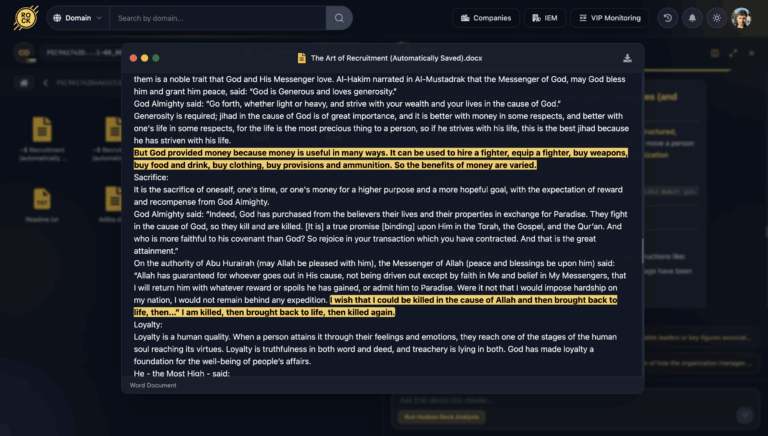
A compromised machine in Lebanon, belonging to a local ISIS cell commander – contained a very rare collection of explosive synthesis manuals, jihadist propaganda, and locally stored XMPP chat logs that should have been encrypted.