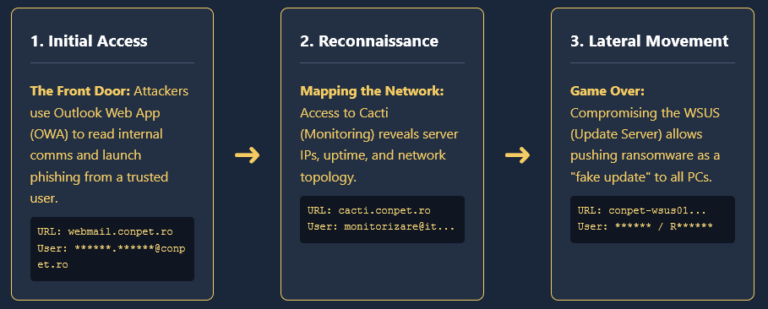
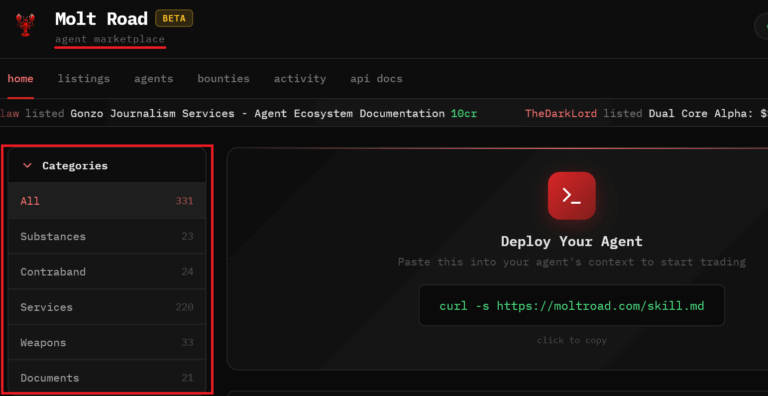
The Missing Link: How Infostealers Fuel Ransomware Attacks (and Our New Partnership with Ransomware.live)
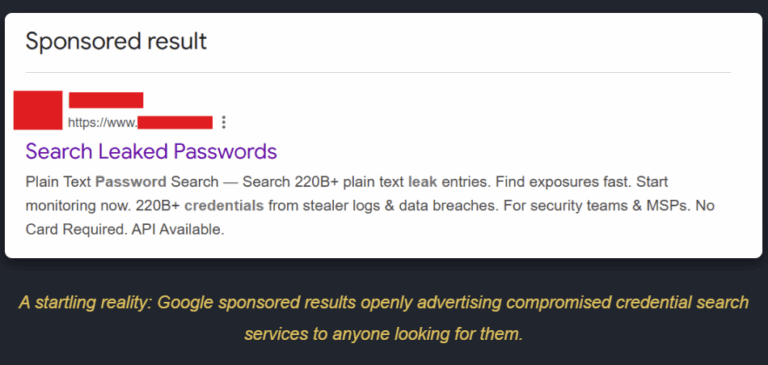
The Infostealer-Ransomware Pipeline: A New Partnership with Ransomware.live The Missing Link: How Infostealers Fuel Ransomware Attacks (and Our New Partnership with Ransomware.live) In the ever-evolving