Analysis of APT attack cases targeting domestic companies using Dora RAT (Andariel Group)
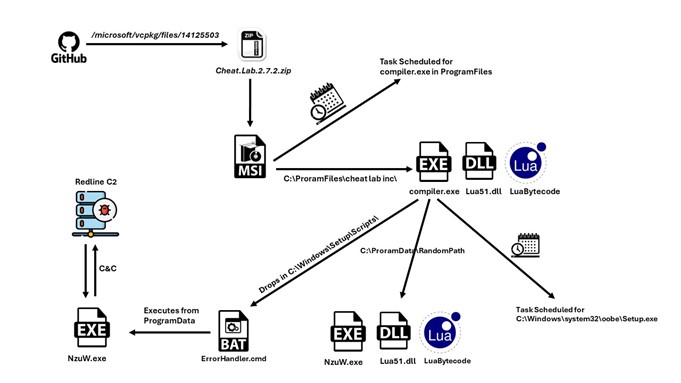
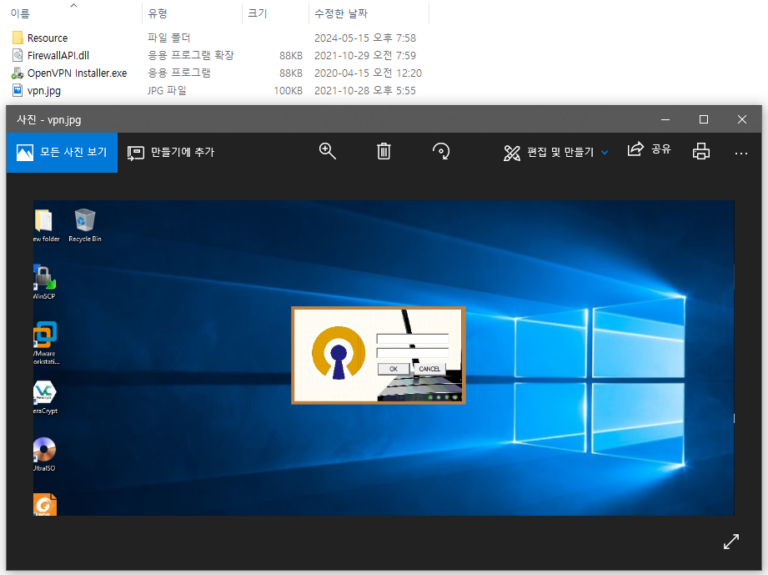
AhnLab SEcurity intelligence Center (ASEC) recently confirmed cases of APT attacks by the Andariel group targeting domestic companies and institutions. The organizations identified as targets