Breaking through the Infostealer Exploit and the Enigma of Cookie Restoration.
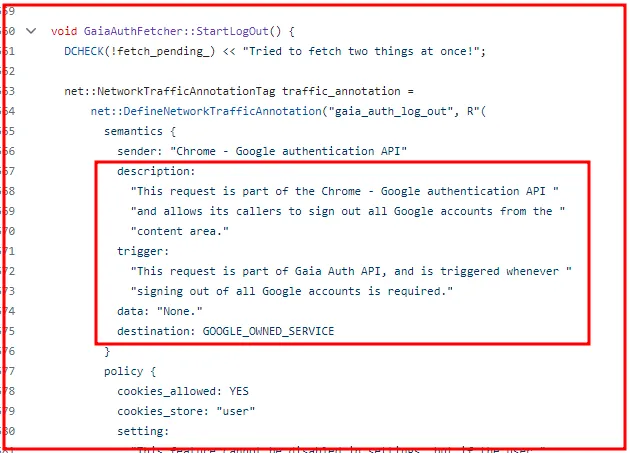
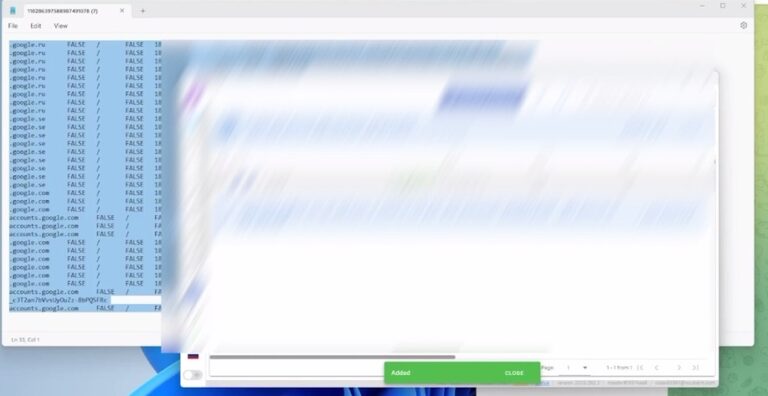
The Lumma Infostealer’s cookie restoration method operates by leveraging a key from restore files, allowing the revival of expired Google cookies…
Home » 0-Day
The Lumma Infostealer’s cookie restoration method operates by leveraging a key from restore files, allowing the revival of expired Google cookies…
Today, even despite attempts to alert Google over a month ago that there is an ongoing 0-day being exploited by Infostealer groups…
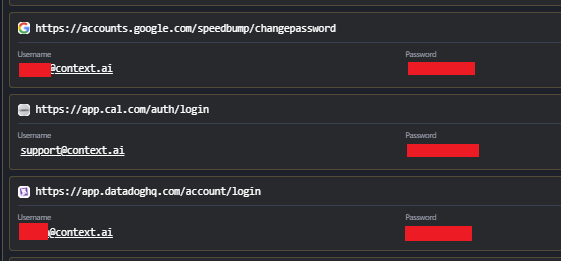
Breaking: Vercel Breach Linked to Infostealer Infection at Context.ai Breaking: Vercel Breach Linked to Infostealer Infection at Context.ai Following the recent confirmation of the Vercel
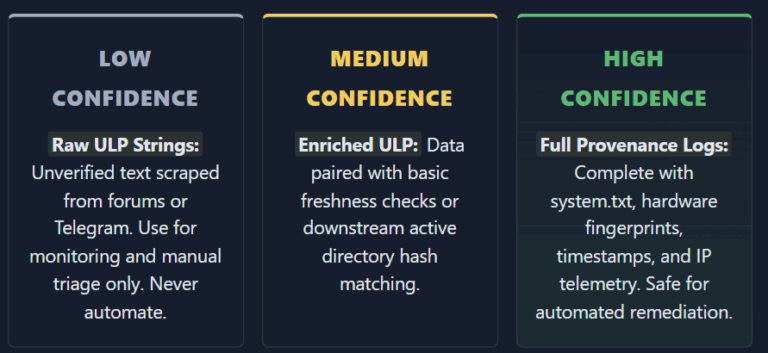
Infostealers ULP Data Is Burning Out SOC Teams and Killing Automation Infostealers ULP Data Is Burning Out SOC Teams and Killing Automation The cybersecurity industry
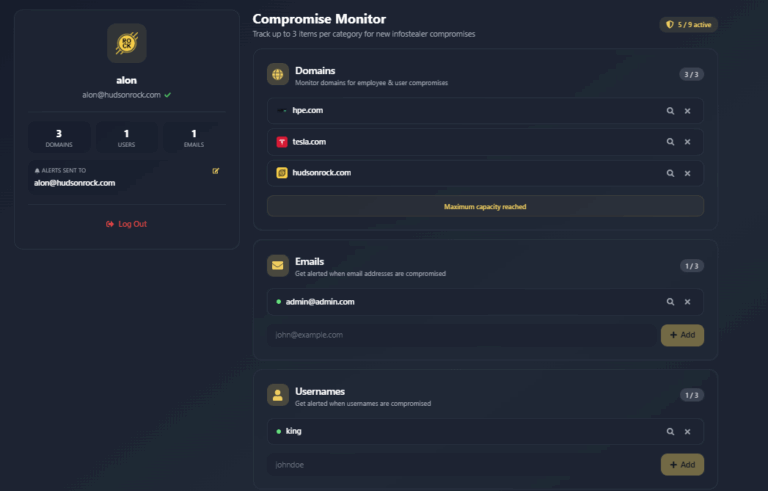
Free Infostealer Monitoring: Track Up to 3 Emails, 3 Domains, and 3 Usernames Free Infostealer Monitoring: Track Up to 3 Emails, 3 Domains, and 3
