Initial Access Brokers, Infostealers, and Everything Between Them
Introduction Hudson Rock recently shed light on how a compromised Citrix account without MFA was potentially used to deploy a devastating ransomware attack on Change Healthcare. This
Home » Citrix
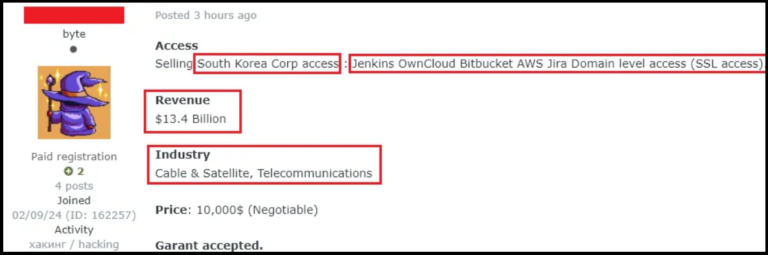
Introduction Hudson Rock recently shed light on how a compromised Citrix account without MFA was potentially used to deploy a devastating ransomware attack on Change Healthcare. This
In late February 2024 Change Healthcare suffered a devastating ransomware attack which led to major disruptions to the company’s platform, estimated at a staggering $872,000,000

Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100+ Company Ransomware Spree Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100+ Company Ransomware

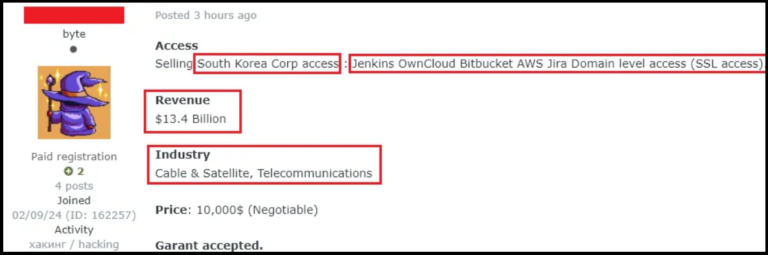
Original report – https://www.teiss.co.uk/news/news-scroller/korean-matchmaking-service-duo-fined-over-600000-over-sensitive-member-data-breach-17402 Korean matchmaking company Duo has been fined over £600,000 by the country’s data protection watchdog for failing to secure the data
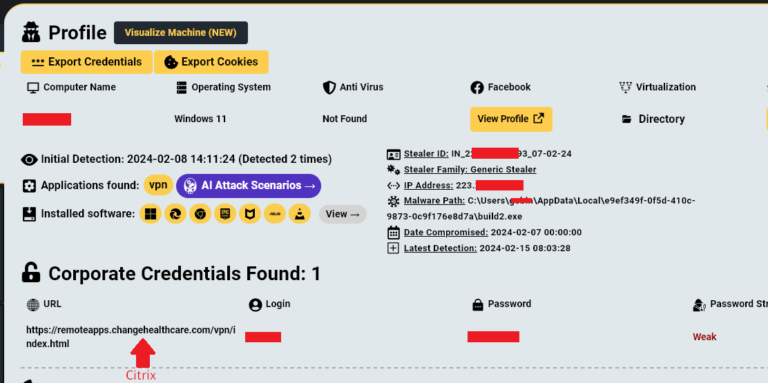
Breaking: Vercel Breach Linked to Infostealer Infection at Context.ai Breaking: Vercel Breach Linked to Infostealer Infection at Context.ai Following the recent confirmation of the Vercel
