In this Help Net Security interview, Alon Gal, CTO at Hudson Rock, discusses integrating cybercrime intelligence into existing security infrastructures.
Our discussion will cover a range of essential aspects, from the importance of continuous adaptation in cybersecurity strategies to practical advice for CISOs on enhancing threat detection and response capabilities. We’ll also explore the challenges of balancing intelligence gathering with privacy and legal considerations and look at strategies for prioritizing intelligence inputs in decision-making.

What advice would you give to a CISO that wants to integrate cybercrime intelligence into an existing security infrastructure to enhance threat detection and response capabilities?
Cybercrime threats come in all shapes and forms, and cybercriminals are often highly motivated. They dedicate substantial time and effort to infiltrate organizations for potential financial gains.
For a hacker, it only takes a single success to establish an initial attack vector against a company. Unfortunately, for us cybersecurity professionals, it takes succeeding at all times to fend off attacks.
For holistic protection, CISOs should integrate various cybercrime intelligence solutions into their security infrastructure.
These solutions should include:
- Providing ongoing cybersecurity training for all employees to increase awareness of common social engineering attacks used by cybercriminals.
- Monitoring for compromised credentials that result from database leaks; these credentials are often used as an initial attack vector.
It is important to ensure proper access controls are set within the organization to limit who can access sensitive information.
- Staying alert & implementing solutions against emerging trends such as AI and machine learning, which are becoming widely used among hackers.
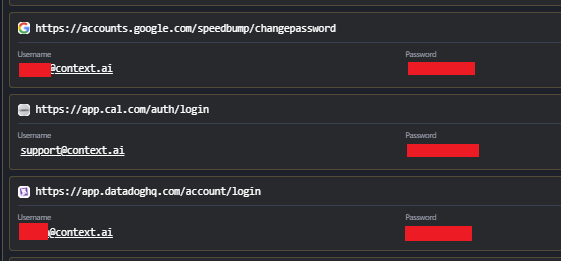
- Recently, there has been a significant increase in the use of Infostealer infections data by cybercriminals. Hackers can take advantage of the credentials and cookies found on compromised computers to perform various cyberattacks against organizations (e.g Airbus breach, Orange breach).
This poses a significant risk to organizations, and it is crucial to monitor whether the organization has infected the computers of employees, customers, and partners.
As cybercrime evolves, it is important to continuously integrate appropriate solutions to counter cybercrime trends.
With the vast amount of cybercrime data available, what strategies can security teams use to prioritize intelligence inputs for decision-making?
Given the vast amount of cybercrime intelligence data generated daily, it is crucial for security teams to effectively prioritize the information they use for decision-making.
To do this, I recommend security teams conduct regular risk assessments that should consider the organization’s risk profile, considering historical data and similar companies in their industry.
Once the risk profile is created, security teams can leverage the most suitable threat intelligence feeds and sources.
Evaluation of these risks should not be static but rather a continuous process that allows teams to regularly review and update their priorities based on the evolving threat landscape.
How can organizations balance the need to gather cybercrime intelligence with privacy and legal considerations?
To have a balance between gathering cybercrime intelligence and respecting privacy and adhering to legal considerations, organizations need to follow strict legal compliance, including data protection laws.
Organizations should also minimise the collection of sensitive information and focus only on essential data, and establish clear ethical guidelines for their intelligence gathering activities.
What metrics or KPIs can CISOs use to measure the effectiveness of cybercrime intelligence in their cybersecurity strategy?
Two of the key metrics and KPIs that can be used by CISOs to evaluate the effectiveness of cybercrime intelligence in their cybersecurity strategy are:
- Mean time to detect (average amount of time needed to detect a security threat or incident).
- Mean time to respond (average time it takes for incident responders to control, remediate, and eradicate a threat after it has been identified).
Additionally, CISOs should also monitor false positive rates, phishing click rates, and assess their ability to detect and respond to emerging threats quickly.
What are your thoughts on enhancing international cooperation to overcome common obstacles in cybercrime investigations?
Enhancing international cooperation in cybercrime investigations is important due to the borderless nature of the internet and the sophistication of cyber criminals.
Recently, we’ve seen multiple successful operations such as the takedown of ransomware groups’ infrastructure (RagnarLocker) and illicit online marketplaces & forums (Operation Cookie Monster, Raidforums takedown).
The role of public-private partnerships are important as well, allowing for the integration of law enforcement with the advanced technological and intelligence resources of cybersecurity companies, as seen in operations like Operation Nervone and Night Fury.
I hope that in 2024 we will see the trend of international cooperation becoming even more prevalent.
Considering the current trends and challenges in cybercrime intelligence, what are your predictions for this field?
Considering the current trends and challenges in cybercrime intelligence, several predictions can be made for the field in the coming years:
- AI and machine learning are likely to play a significant role in cybercrime intelligence, we’re already seeing some worrying trends such as sophisticated spear-phishing powered by AI and clever impersonation attacks.
- Given the ease of monetization of ransomware attacks, I expect to see a continued rise in the number and the sophistication of attacks. Governments and organizations will need to work hard in order to enhance their response strategies.
- Threat intelligence sharing will likely increase as more countries and organizations share intelligence in real-time to have quicker responses to emerging cyber threats.
- Automated infiltrations using Infostealers data is a concerning development that represents a significant escalation in both the efficiency and scale of cyber attacks. I expect to see more breaches, ransomware attacks and account takeovers which originate from Infostealer infections to happen in 2024.
Thanks for reading ~Alon Gal.