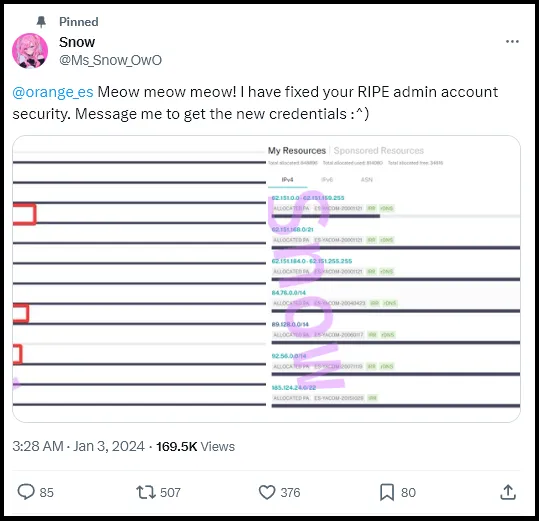
Infostealer infection of an Orange employee results in BGP disruptions
Using the stolen account, the threat actor modified the AS number belonging to Orange’s IP address, resulting in major disruptions…
Home » Orange
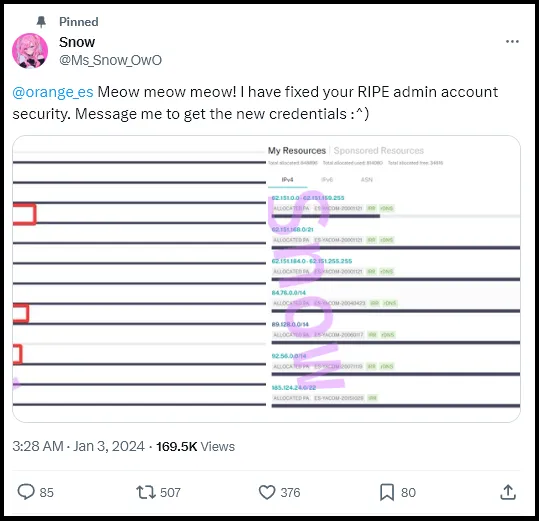
Using the stolen account, the threat actor modified the AS number belonging to Orange’s IP address, resulting in major disruptions…

Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100+ Company Ransomware Spree Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100+ Company Ransomware

Original report – https://www.teiss.co.uk/news/news-scroller/korean-matchmaking-service-duo-fined-over-600000-over-sensitive-member-data-breach-17402 Korean matchmaking company Duo has been fined over £600,000 by the country’s data protection watchdog for failing to secure the data
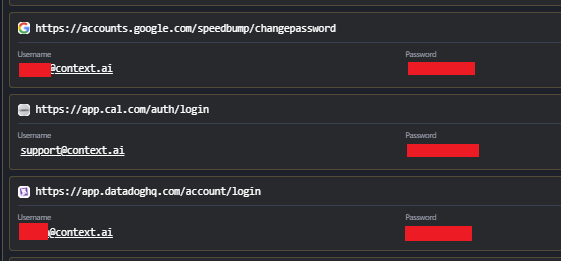
Breaking: Vercel Breach Linked to Infostealer Infection at Context.ai Breaking: Vercel Breach Linked to Infostealer Infection at Context.ai Following the recent confirmation of the Vercel
