Key Learnings from Files Present on the C2 Server of an Infamous Infostealer Malware
This method can be applied to multiple other C2 servers that we come across on a daily basis to check for any security misconfigurations…
Home » VirusTotal
This method can be applied to multiple other C2 servers that we come across on a daily basis to check for any security misconfigurations…
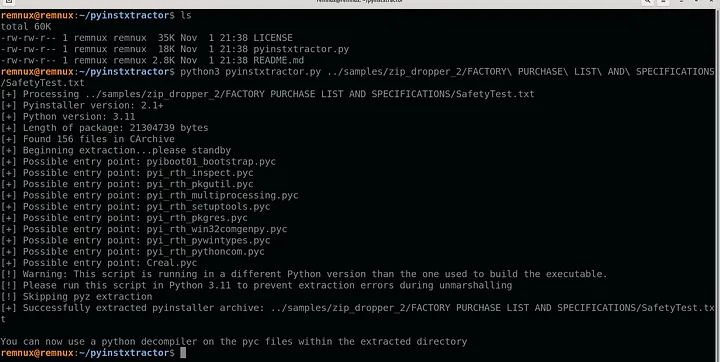
A ZIP/LNK payload and, with some luck, we will end up identifying the infostealer that is being dropped and its source code…

Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100+ Company Ransomware Spree Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100+ Company Ransomware

Original report – https://www.teiss.co.uk/news/news-scroller/korean-matchmaking-service-duo-fined-over-600000-over-sensitive-member-data-breach-17402 Korean matchmaking company Duo has been fined over £600,000 by the country’s data protection watchdog for failing to secure the data
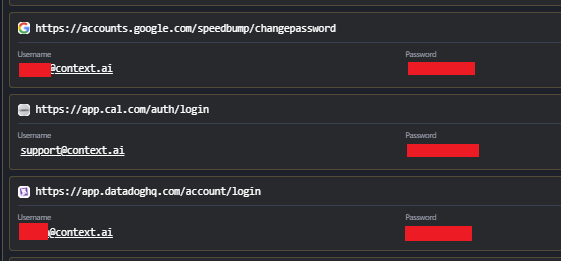
Breaking: Vercel Breach Linked to Infostealer Infection at Context.ai Breaking: Vercel Breach Linked to Infostealer Infection at Context.ai Following the recent confirmation of the Vercel
