
Botnets & Info-Stealers (Part Ⅲ)
In this last part of a three part series, our teams summarize the major takeaways from our joint research and provide you with some actionable recommendations…
Home » Cyrus

In this last part of a three part series, our teams summarize the major takeaways from our joint research and provide you with some actionable recommendations…

In this second of a three blog post series, Cyrus and Hudson Rock reveal how the info-stealer threat looks from the hacker’s point of view…

An information stealer is a type of malware that gathers sensitive information stored on a device. Once a computer has been infected, the info-stealer uses various techniques to acquire data…
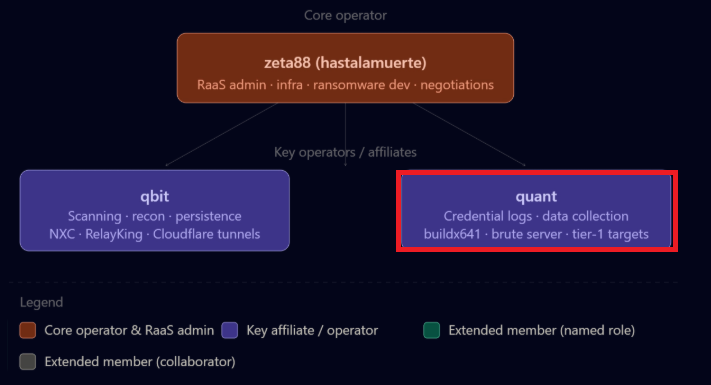
The Gentlemen Ransomware Group’s Infostealer Playbook How The Gentlemen Ransomware Group Operates: A Blueprint Built on Infostealer Credentials A recent internal data leak from “The

The Infostealer-Ransomware Pipeline: A New Partnership with Ransomware.live The Missing Link: How Infostealers Fuel Ransomware Attacks (and Our New Partnership with Ransomware.live) In the ever-evolving

Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100+ Company Ransomware Spree Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100+ Company Ransomware
