Part 2 of a 3 Part Series in Collaboration with Cyrus: Botnets & Info-Stealers
The following post, a first of a three part series, is presented in collaboration with Cyrus.
Intro
In this second of a three blog post series, Cyrus and Hudson Rock reveal how the info-stealer threat looks from the hacker’s point of view — the spread of malware across different countries, the most affected online services in day-to-day sectors, and the effect the Work-From-Home era has on the use and spread of info-stealers.
Which regions do cybercriminals target?
To better understand which geographical regions are on cybercriminals’ radar, our teams poured over the data and found some interesting facts. According to Hudson Rock’s data, 15% percent of one million randomly selected, compromised devices belong to Americans.
In parallel, the Cyrus research team analyzed chatter in closed cybercrime communities and discovered that threat actors strongly prefer attacking wealthier countries over poorer ones. In the heat-map below we can clearly see that the info-stealer campaigns are coming from different parts of the world. However, the hackers always prefer to first monetize Western regions like the U.S. and Europe.

Heat-map generated from the geolocations of 1,000,000 compromised computers worldwide
The Numbers
After a device was successfully infected and the data was sent to a cybercriminal, it is then time to start checking the data for any hot commodities.
The higher the number of compromised accounts, the easier it is for cybercriminals to monetize them or use them for illicit activity. Down below you’ll see some examples of how malicious actors use this gathered information.
Now let’s dive into the data and see which companies and services were most affected in each sector. This will help us understand how your everyday accounts and services are in fact a treasure trove for an opportunistic hacker.
Financial Sector
Once a financial account has been taken over, the race for a money or cryptocurrency cash-out is on. As we can see, PayPal clearly leads the list: this reflects the underground methodology of researching and developing tools/tutorials for the most commonly used services. These compromised accounts can also be used to transfer funds in order to cover one’s tracks.

Social Media
Mainstream social accounts are typically sold in bulk (for several U.S. dollars each) on the black market. An account with a detailed history looks much more genuine for spamming or influence campaigns than a new one. The accounts that belong to influencers or high-net individuals are subject to takeover attacks and ransom requests (usually starting at 500 USD).

Email Providers
Compromised email addresses are used to send spam and phishing emails via somebody else’s digital identity. This exploits the email recipient’s trust as they believe that the message comes from a legitimate contact.
As the info-stealer data below demonstrates, Gmail still dominates the email market, and therefore remains the provider with the most compromised devices. Basically, nobody is safe.
We strongly advises activating 2FA (two-factor authentication) to minimize as much as possible the risks of an email account takeover.

Online Marketplaces
Online marketplaces often suffer from account takeovers stemming from info-stealers. As a result, hackers use compromised, reputable eBay accounts in order to advertise fraudulent listings or even abuse Amazon accounts to reroute packages that victims ordered.

Streaming Services
Stolen streaming account credentials are in high demand; they are put up for sale on dedicated underground forums and black markets for only a few U.S. dollars.

How Compromised Work Accounts Skyrocketed in the WFH Era
As “Work-From-Home” models gained popularity across the world due to COVID-19, the incidence of employees accessing sensitive corporate domains via their personal computers increased in tandem. For instance, some employees tend to use their work-related devices for personal needs, which can increase the odds of an info-stealer attack.
However, other employees are simply not familiar with cybersecurity protocols (or ignore them) and therefore utilize their personal computers to access their work environment or corporate network.
As we learned from the first blog post, all the login credentials are always captured as clear-text passwords. This means that if you mix your work and your personal life on the same device and then fall prey to an info-stealer attack, the keys to your company’s network are gently dropped on the hacker’s table.
More advanced cybercriminals prefer not to focus on selling an additional 10,000 compromised Netflix accounts, and instead patiently wait until they find some juicy corporate access points that can then be sold in underground hacking communities. This is the inception of the next data breach or another more severe cybersecurity incident that will occur in the future.
Take Your Personal Cybersecurity to the Next Level
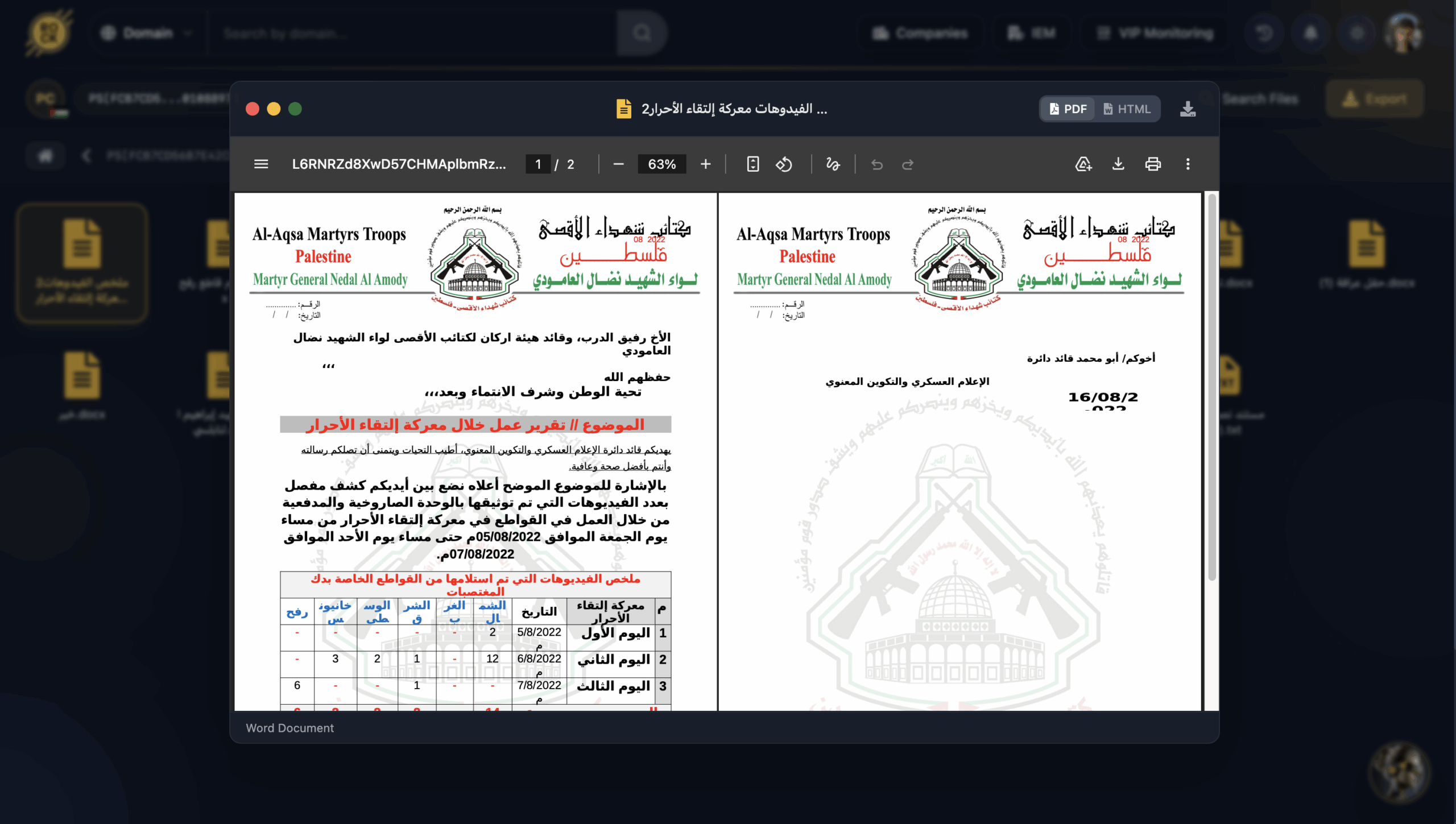
Using the Hudson Rock cybercrime intelligence feed, Cyrus is able to determine which compromised links are affiliated with corporate accounts and can serve as sensitive corporate access points.
In the event you have been alerted to an info-stealer attack which involves your work-related accounts, we strongly advise you to immediately change your passwords and report this incident to your IT department.
In the screenshot below, our joint analysis shows the number of sensitive work-related login links belonging to Hewlett Packard. These were discovered in Hudson Rock’s cybercrime database.
For example, the first link leads to the corporate “File Transfer Service.” Do you really want your personal and work information to be easily available to malicious actors?

Corporate URLs accessed by compromised employees are used by threat actors for network takeovers.
What Can We Learn?
- Hackers know how to extract financial, retail and social media account credentials from infected devices. They will first try to monetize those from the most developed countries.
- If you work from home or from any remote location, make sure you’re familiar with your employer’s cybersecurity policies and protocols. The best practice is to separate work and personal computers.
- The key to mitigating any potential cybersecurity incident is to continuously monitor your devices and to take action as soon as possible.
In the final part of this three-part blog series, our teams will cover the time that it takes to discover an infection (this will surprise you!), as well as provide you with a comprehensive summary. We will even share insights from an ex-cyber criminal who is an expert in info-stealer attacks.