
Botnets & Info-Stealers (Part Ⅲ)
In this last part of a three part series, our teams summarize the major takeaways from our joint research and provide you with some actionable recommendations…
Home » Cyrus

In this last part of a three part series, our teams summarize the major takeaways from our joint research and provide you with some actionable recommendations…

In this second of a three blog post series, Cyrus and Hudson Rock reveal how the info-stealer threat looks from the hacker’s point of view…

An information stealer is a type of malware that gathers sensitive information stored on a device. Once a computer has been infected, the info-stealer uses various techniques to acquire data…
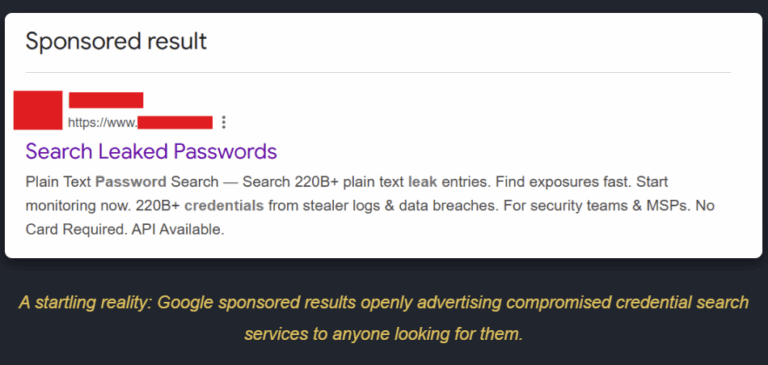
The New Era of Initial Access: How Infostealer Lookup Services are Changing Cybercrime We are currently witnessing a massive shift in how cyberattacks begin. Infostealer
How One Infostealer Infection Solved a Global Supply Chain Mystery and Unmasked DPRK Spies in U.S. Crypto. Researcher & Law Enforcement Notice: Hudson Rock welcomes
Infected by GTA 5 Cheats: How an Infostealer Infection Unmasked a North Korean Agent State-sponsored cybercrime is evolving. Foundational research by Kudelski Security, utilizing Hudson
