ID Verification Service for X & TikTok Breached due to an Infostealer Infection
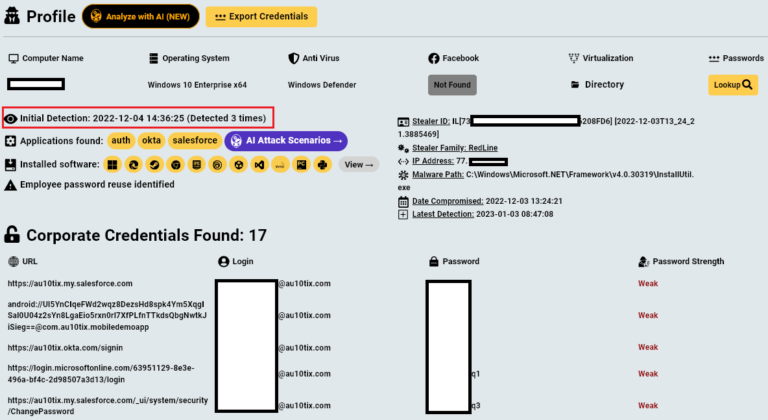
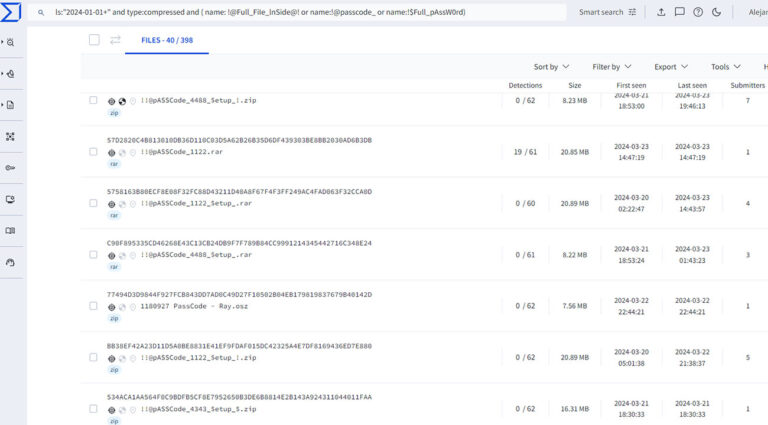
AU10TIX, a company that verifies the identities of TikTok, Uber, and X users, sometimes by processing photographs of their faces and pictures of their drivers’
AU10TIX, a company that verifies the identities of TikTok, Uber, and X users, sometimes by processing photographs of their faces and pictures of their drivers’
Affected Platforms: Microsoft WindowsImpacted Users: Microsoft WindowsImpact: The stolen information can be used for future attackSeverity Level: High The past few years have seen a significant increase in the
Case Summary It was a quiet Monday morning in March 2024 when the EDR researchers with our Trellix Advanced Research Center identified an interesting sequence

Learn about Infostealers with actual real life breaches caused by Infostealer infections with Leonid Rozenberg, Hudson Rock’s Head of Partnerships & Integrations. To discover how

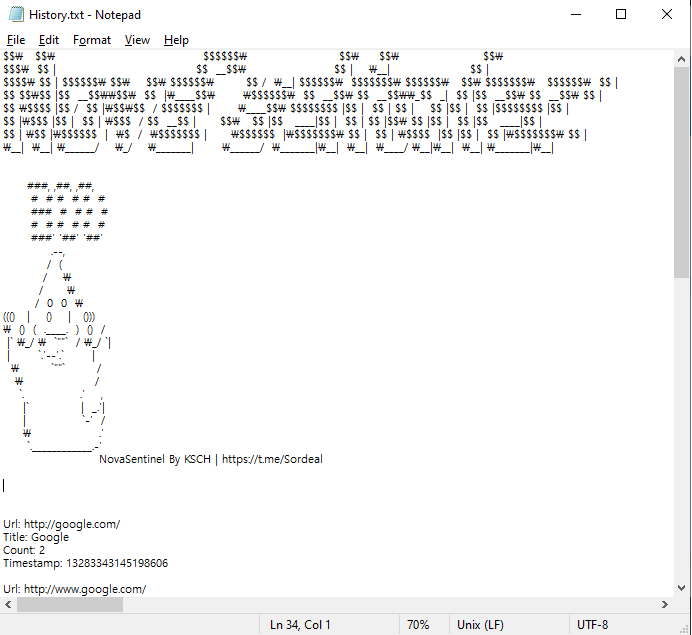
Infostealers commit close to the perfect crime. They sneak into your computer, grab your logins, passwords, and anything of value, and then delete themselves on
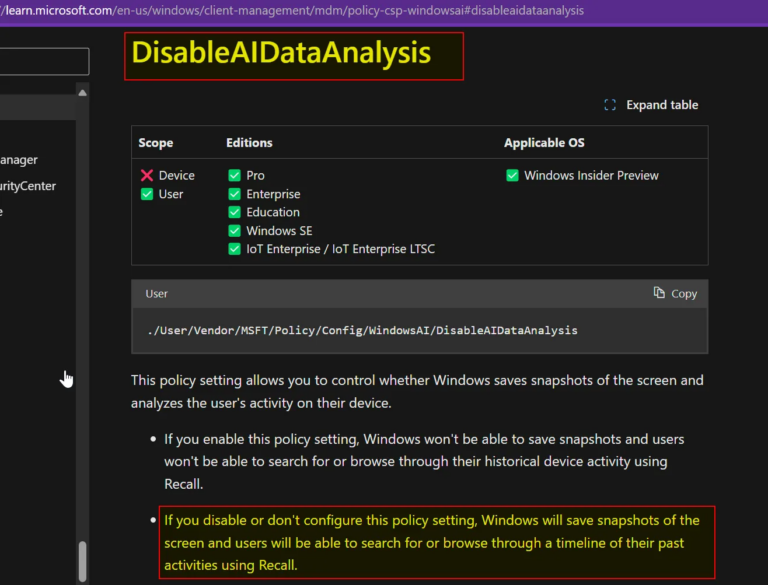
I wrote a piece recently about Copilot+ Recall, a new Microsoft Windows 11 feature which — in the words of Microsoft CEO Satya Nadella- takes “screenshots”
EXECUTIVE SUMMARY At CYFIRMA, we are committed to offering up-to-date insights into prevalent threats and tactics employed by malicious actors who target organizations and individuals.

The adversaries use the open-source SapphireStealer to create their own Infostealer malware for collecting employee authentication data from Russian companies. Since March 2024, the BI.ZONE Threat

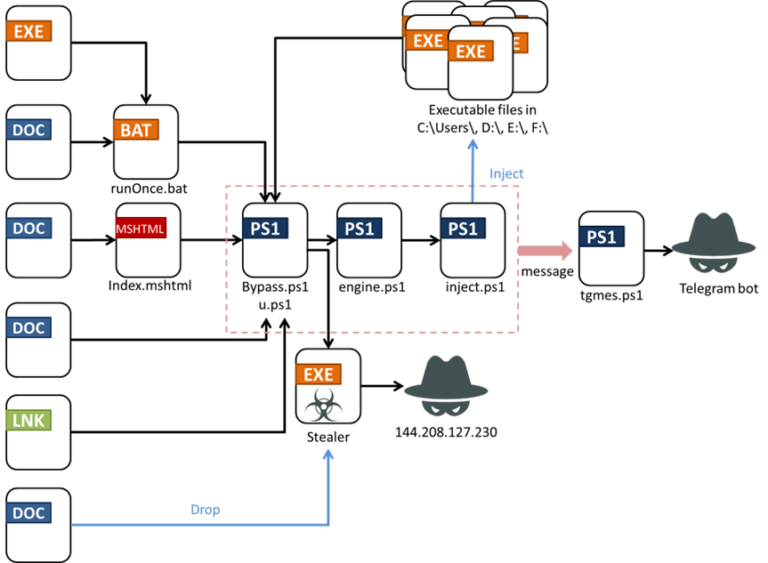
Executive summary In mid-April 2024, Trellix Advanced Research Center team members observed multiple fake AV sites hosting highly sophisticated malicious files such as APK, EXE
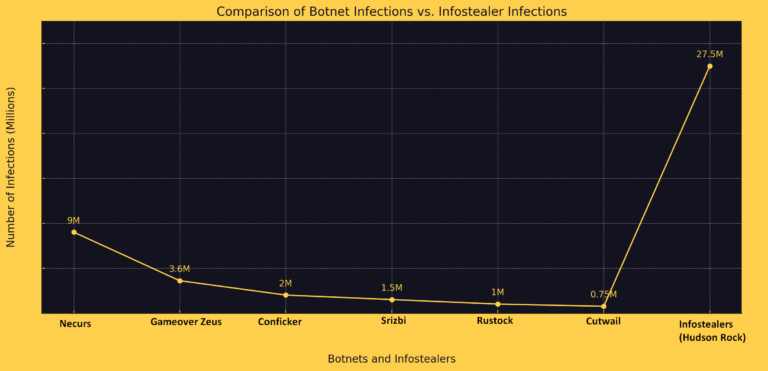
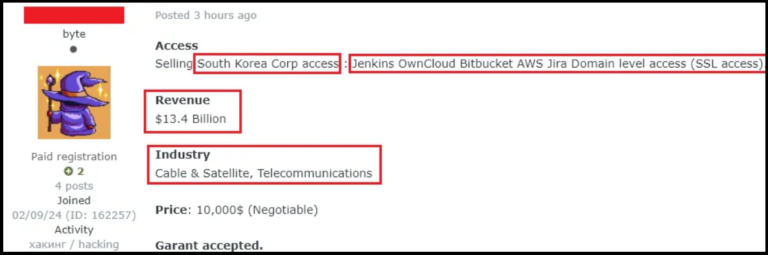
The landscape of cyber threats has been shifting dramatically in recent years, with a notable transition from traditional botnets to a more insidious form of
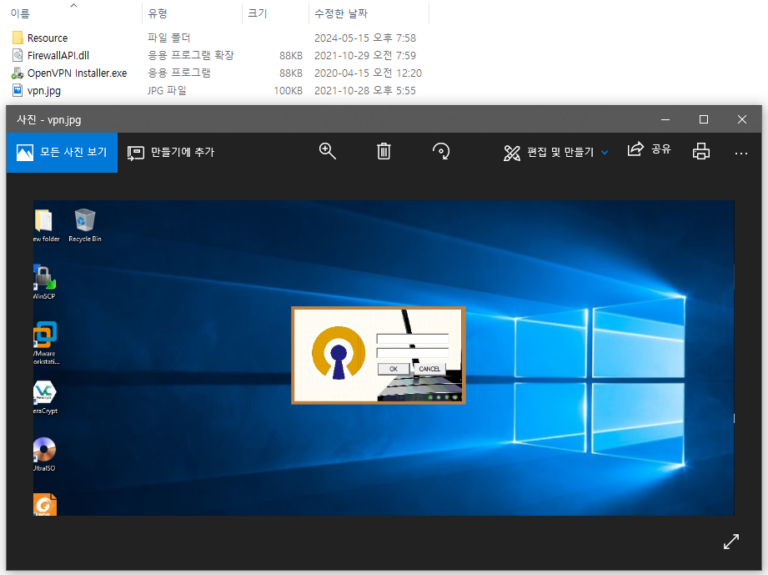
AhnLab SEcurity intelligence Center (ASEC) recently confirmed cases of APT attacks by the Andariel group targeting domestic companies and institutions. The organizations identified as targets

Summary So far, 2024 really has been the year of the infostealer when it comes to macOS malware. Families like AtomicStealer, Cuckoo, and CloudJump are
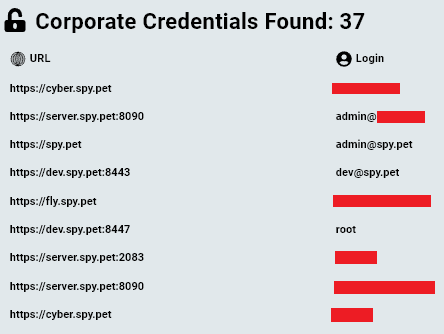
Introduction Hudson Rock recently shed light on how a compromised Citrix account without MFA was potentially used to deploy a devastating ransomware attack on Change Healthcare. This
This article aims to shed light on the identity behind a massive Discord spying tool and raise concerns about the possibility of private Discord data
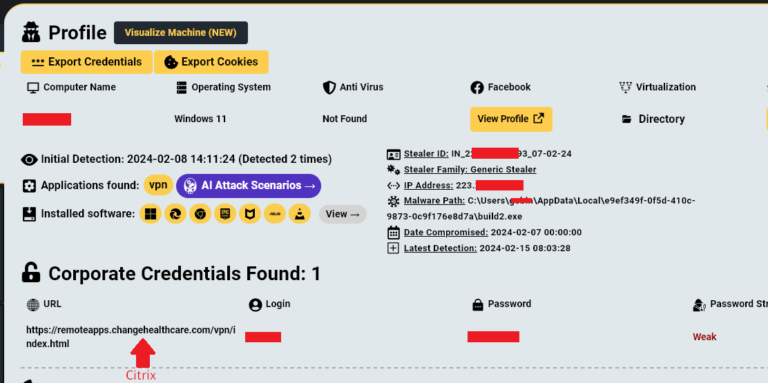
In late February 2024 Change Healthcare suffered a devastating ransomware attack which led to major disruptions to the company’s platform, estimated at a staggering $872,000,000
AhnLab SEcurity intelligence Center (ASEC) has discovered an Infostealer strain made with Electron. Electron is a framework that allows one to develop apps using JavaScript,
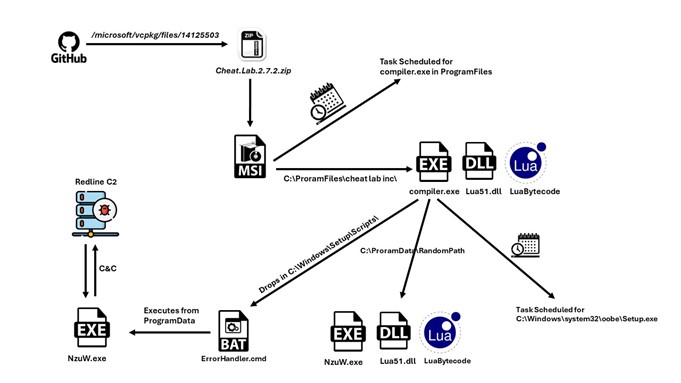
A new packed variant of the Redline Stealer trojan was observed in the wild, leveraging Lua bytecode to perform malicious behavior.McAfee telemetry data shows this

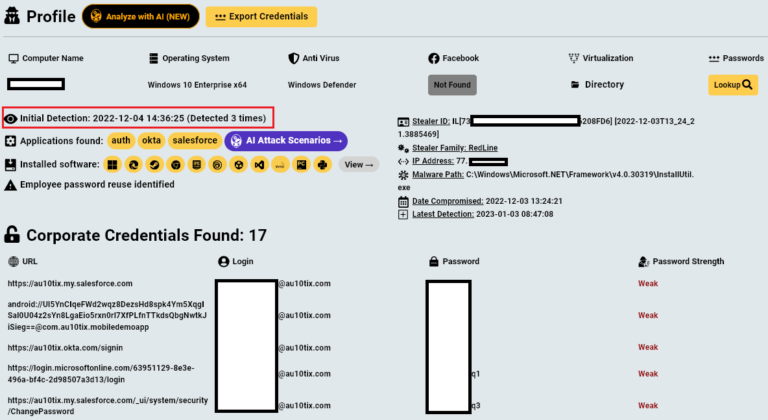
CoralRaider operators likely based in Vietnam Talos assesses with high confidence that the CoralRaider operators are based in Vietnam, based on the actor messages in
