The adversaries use the open-source SapphireStealer to create their own Infostealer malware for collecting employee authentication data from Russian companies.
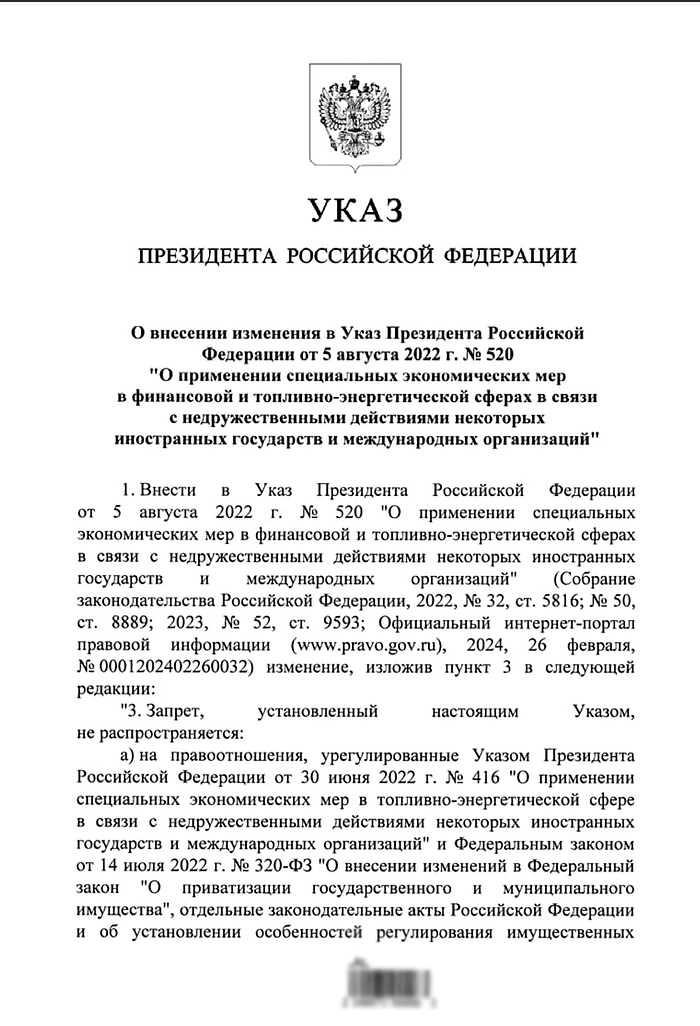
Since March 2024, the BI.ZONE Threat Intelligence team has been tracking the cluster of activity dubbed Sapphire Werewolf. The threat actor targets Russia’s industries, such as education, manufacturing, IT, defense, and aerospace engineering. Over 300 attacks were carried out using Amethyst, an offshoot of the popular open-source SapphireStealer. The attackers disguise the malware as an enforcement order, a Central Election Committee leaflet, and even as a decree from the President of Russia. We can conclude, with medium confidence, that the cluster used phishing emails with T.LY links to deliver Amethyst to the target systems.
Key findings
- Espionage-driven adversaries increasingly often employ stealers for obtaining various authentication data.
- Attackers do not necessarily have to create malware from scratch. They can modify already existing commercial or open-source solutions.
- Catchy subject lines plus decoys with content matching the names of the malicious files increase the chances for a successful delivery of malware to target systems.
Campaign
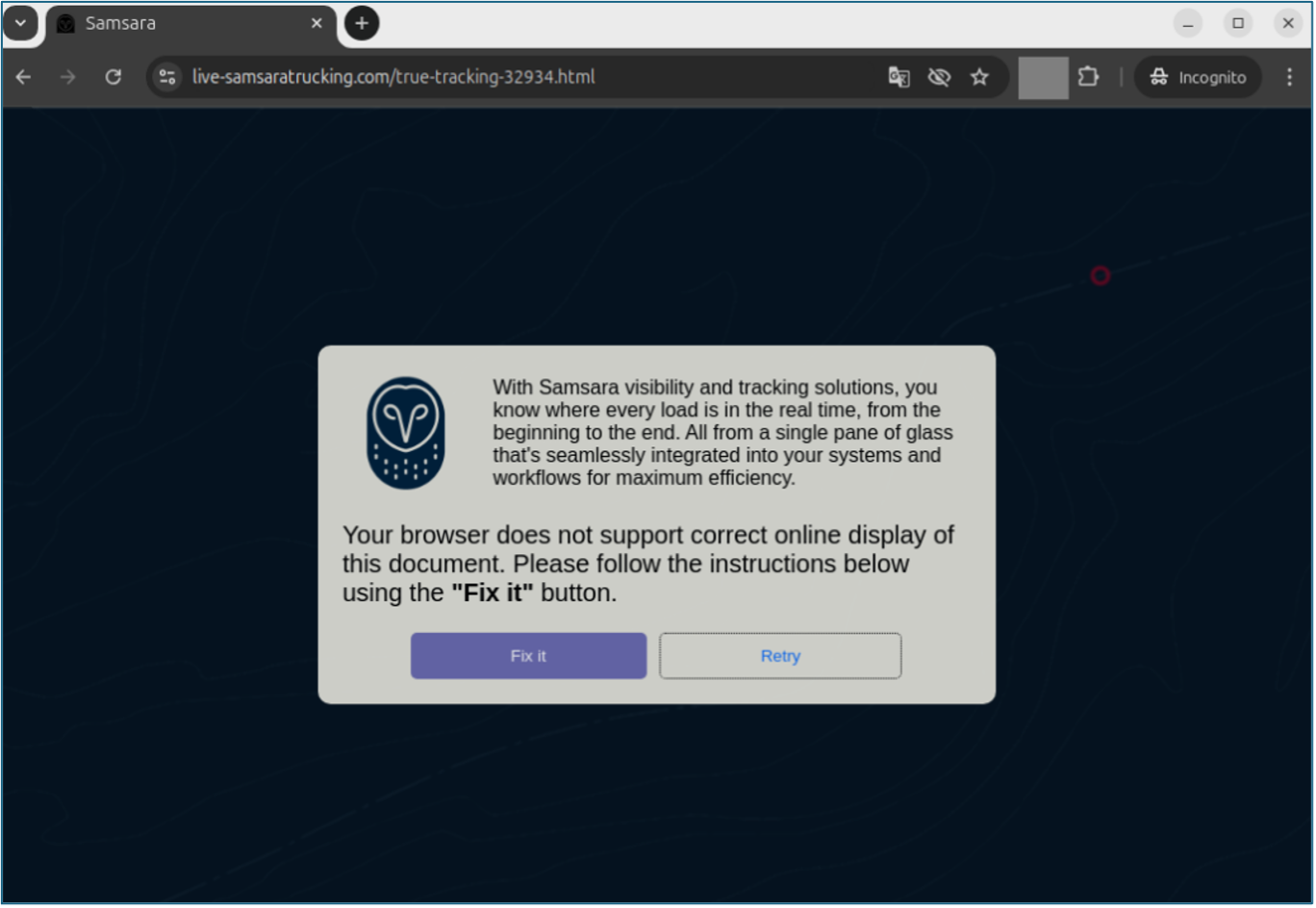
All the malicious files used by the adversaries in the campaign have certain functional similarities.
By opening such a file a victim unknowingly creates the folder %AppData%\Microsoft\EdgeUpdate and copies to it MicrosoftEdgeUpdate.exe from Resources.MicrosoftEdgeUpdate.
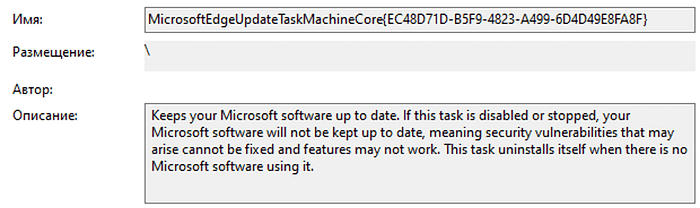
To get a foothold in the compromised system, the adversaries create a task in Windows Task Scheduler. For this purpose, they use the library embedded in the executable file, FunnyCat.Microsoft.Win32.TaskScheduler.dll. This legitimate library makes it possible to create a scheduled task without actually running schtasks. The name, description, and path to the executable file in the task are disguised as a legitimate task MicrosoftEdgeUpdateTaskMachineCore. The newly created task is executed every 60 minutes after the initial launch.
At the same time, a decoy document is written into the current folder and then opened.
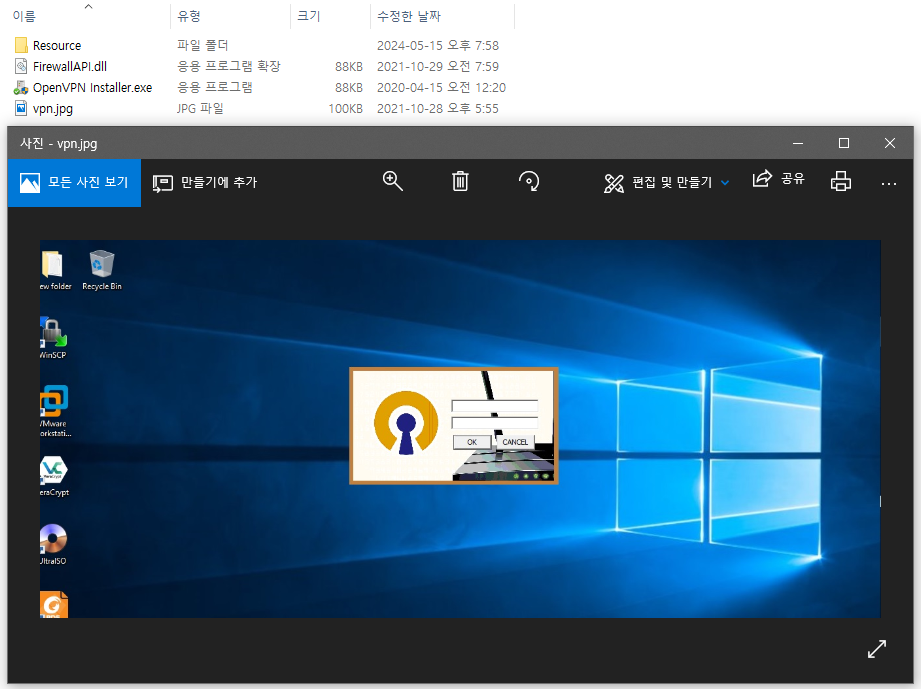
After that, the Amethyst stealer is written to the VPN.exe file in a temporary data folder and run.
Once the program has been executed, the file is deleted via the following command: cmd.exe /C choice /C Y /N /D Y /T 3 & Del “[path to the current executable file]”.
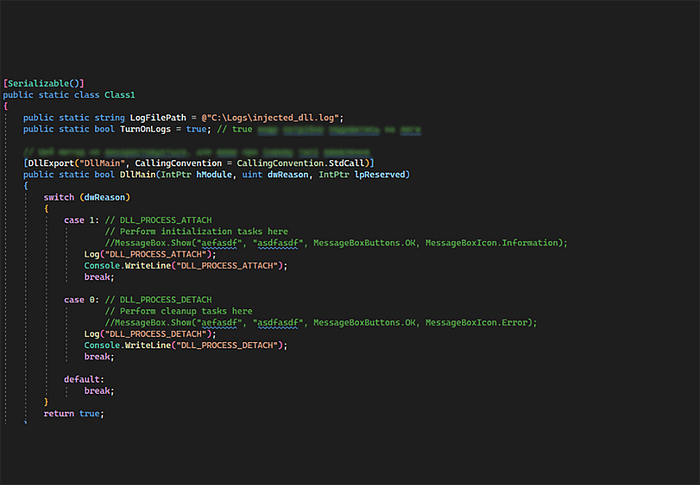
As noted earlier, Amethyst is based on the source code of SapphireStealer, an open-source information stealer.
Running the malicious file changes the execution thread’s security zone on MyComputer and creates an asynchronous task that will later send the collected files to the C2 server.
The collected files are saved in a folder whose name is a UUID-generated string. The folder is located in a directory with temporary files.
The stealer gathers the following files:
- Telegram configuration files from
%AppData%\Telegram Desktop\tdata - password and cookie databases, browser and popular website histories, saved pages and configurations from the browsers Chrome, Opera, Yandex, Brave, Orbitum, Atom, Kometa, Edge Chromium, Torch, Amigo, CocCoc, Comodo Dragon, Epic Privacy Browser, Elements, CentBrowser, 360 Chrome, and 360 Browser
- PowerShell logs stored in
%AppData%\Microsoft\Windows\PowerShell\PSReadLine FileZillaandSSHconfiguration files
The above mentioned files get archived and sent to the C2 server, after which the folder is cleared.
Once this is done, the stealer collects the following:
- files from
%UserProfile%/Downloads/Telegram Desktopwith the extensions.txt,.pdf,.doc,.docx,.xls,.xlsx,.crt,.cer,.ca-bundle,.p7b,.p7c,.p7s,.pem,.key,.keystore,.jks,.p12,.pfx,.ppk,.pub,.sig,.sgn,.rsa,.rdp,.vnc,.tvc,.tvf,.amy,.ica,.plist,.lmi,.nxs,.remmina,.rvc,.json,.tf,.yml,.yaml,.dockerfile,.vncloc,.ini,.ovpn,.rtsx,.config,.jump,.x2go, and.xml - files from removable media, also with the said extensions
All these files get compressed into an archive and transmitted to the C2 server.
In the latest versions of Amethyst, the archive is protected by a password stored in the program memory. The archive also contains a note with the following data:
- the compromised device’s public IP address obtained through a query to
http://checkip.dyndns.org - the compromised device’s private IP address obtained by using
C#of theDnsclass - the compromised device’s name obtained by using the
GetHostNamefunction of theDnsclass - the user ID obtained with the query
SELECT SerialNumber FROM Win32_BaseBoard WMIand the objectwin32_processor=>processorID - the unpacked archive size
The C2 server that sends the archive is a Telegram bot whose token, as well as the user ID, is in the program. It should be noted that more than one token and more than one user ID can be specified in the program to substitute the main bot or the main client if those are unavailable.
The program can also retrieve the address of an additional control server by searching through posts in the preview of a specified Telegram channel. The stealer obtains the channel preview page by querying the resource https://t.me/s/[channel ID]. The post with the С2 server address looks as follows: %N[C2 server address]?H.
The tags for the archive to be sent are as follows:
filename: the name of the archiveusertag: 1stepname: Ragdoll
The MicrosoftEdgeUpdate.exe file enables the download and execution of additional files in the compromised system. Same as Amethyst, the file gets the C2 server address for downloading extra files through a post in the Telegram channel. The following parameters are also added to the query:
- the compromised device’s public IP address obtained through a query to the network resource
http://checkip.dyndns.org - the user ID obtained by using the query
SELECT SerialNumber FROM Win32_BaseBoard WMIand the objectwin32_processor=>processorID
The query looks as follows: [server address + protocol]/download?ip=[public IP address of the device]&uId=[device ID].
You can also see how the malware evolves over time. For example, in the files discovered about three months ago, the folder used for saving the collected data was named sapphire, which makes it evident that Amethyst originated from this stealer. Besides, at that time, the stealer did not contain any additional stages, nor did it have any mechanisms for achieving persistence in the compromised system.
A limited set of data was gathered: nothing but password and cookie databases were extracted from browsers while files from Telegram downloads and removable media were ignored. PowerShell logs were also disregarded.
In the course of our investigation, we also discovered additional information about this cluster of activity. For example, we found a list of email addresses lined up for a phishing campaign, as well as files representing a Visual Studio project of the stealer.
We also discovered several Microsoft Word and PDF files:
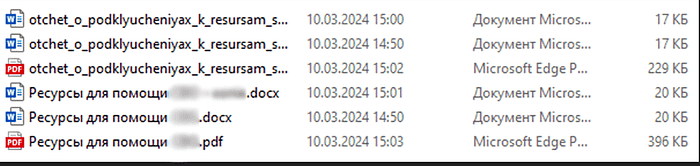
We assess with medium confidence that the adversaries planned to use the files as decoys.
Indicators of compromise
301d00aeae52011530370dcf32d0b68ebdcec291d94501b90a44dcc9a714e595204bcbb030856bfbd7f4b5edad94e17e61a3d44cde88dbcf4f6a30adb786d1a65c01531a6b7f25b92e9a2d0d67fe7057813140d2c60dc0bb356b190aa91a5857
MITRE ATT&CK

More indicators of compromise and a detailed description of threat actor tactics, techniques, and procedures are available on the BI.ZONE Threat Intelligence portal.
Detection
The BI.ZONE EDR rules below can help organizations detect the described malicious activity:
win_creation_task_that_run_file_from_suspicious_folderwin_possible_browser_stealer_activitywin_suspicious_access_to_software_sensitive_files
We would also recommend that you monitor suspicious activity related to:
- running suspicious executable files from the
%Temp%folder - running executables resembling system files from unusual folders
- creating scheduled tasks not typical for the organization
- opening sensitive files through unusual processes
- accessing external finders of IP addresses
How to protect your company from such threats
Sapphire Werewolf’s methods of gaining persistence are hard to detect with preventive security solutions. Therefore, we recommend that companies enhance their cybersecurity with endpoint detection and response practices, for instance, with the help of BI.ZONE EDR.
To stay ahead of threat actors, you need to be aware of the methods used in attacks against different infrastructures and to understand the threat landscape. For this purpose, we would recommend that you leverage the data from the BI.ZONE Threat Intelligence portal. The solution provides information about current attacks, threat actors, their methods and tools. This data helps to ensure the effective operation of security solutions, accelerate incident response, and protect from the most critical threats to the company.