
The Industrialization of “ClickFix”: Inside ErrTraffic
The Industrialization of “ClickFix”: Inside ErrTraffic – Hudson Rock The Industrialization of “ClickFix”: Inside ErrTraffic Author: Hudson Rock Threat Intelligence Team | Date: December 28,

The Industrialization of “ClickFix”: Inside ErrTraffic – Hudson Rock The Industrialization of “ClickFix”: Inside ErrTraffic Author: Hudson Rock Threat Intelligence Team | Date: December 28,
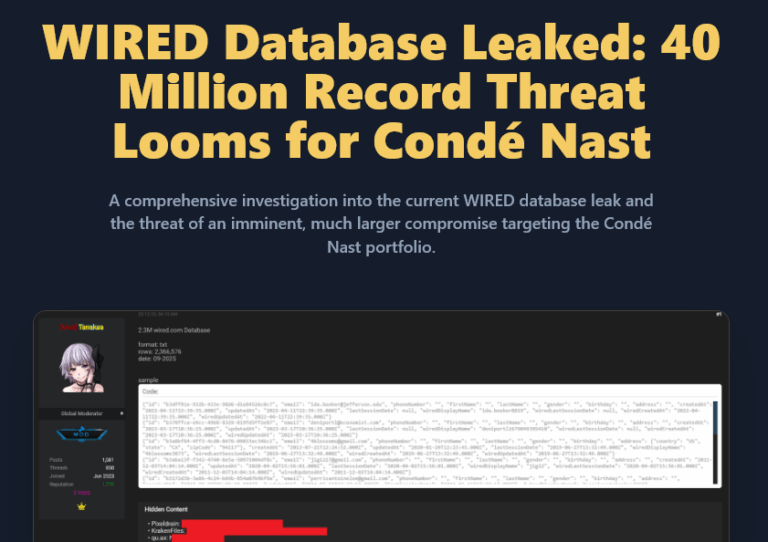
WIRED Database Leaked – Condé Nast Breach Analysis Incident Analysis Report WIRED Database Leaked: 40 Million Record Threat Looms for Condé Nast A comprehensive investigation
🚀 Big News for Recon & OSINT Professionals! 🚀 🤝 We are thrilled to announce that Hudson Rock is now officially integrated with theHarvester, one
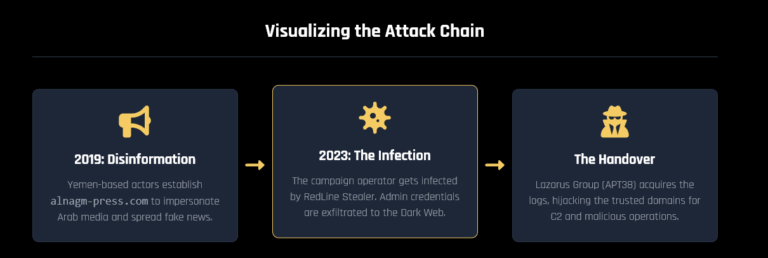
Hudson Rock Report: The Infostealer to APT Pipeline HUDSON ROCK Cybercrime Intelligence Back to Home APT Threat Intel Disinformation The Infostealer to APT Pipeline: How
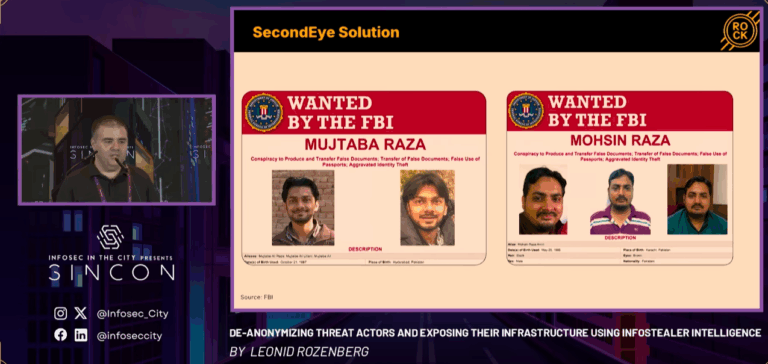
Speaker: Leonid Rozenberg, Cybercrime Researcher, Hudson Rock. Infostealing malware has become a near-perfect tool for cybercriminals, enabling the theft of sensitive data with remarkable efficiency.
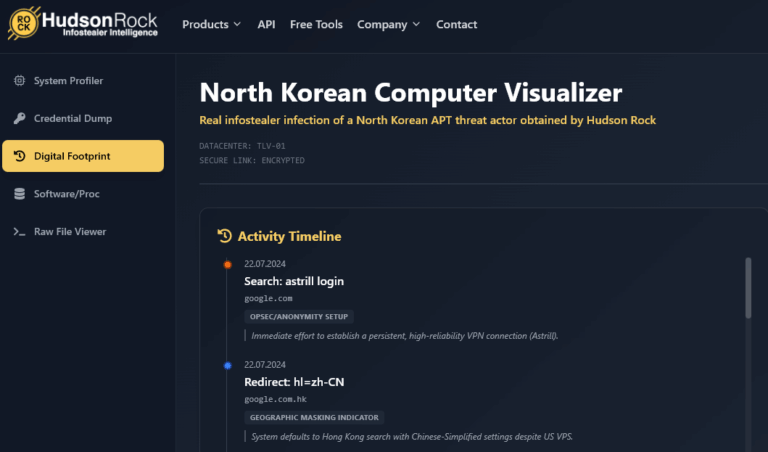
*Interactive simulator can be accessed via desktop – www.hudsonrock.com/northkorean In the world of Threat Intelligence, we are usually looking at the aftermath of an attack:

The Infostealer-to-APT Pipeline – Hudson Rock Infographic HUDSON ROCK THE INFOSTEALER TO APT PIPELINE How stolen diplomatic credentials fuel cyber-political power plays. The Dangerous Escalation
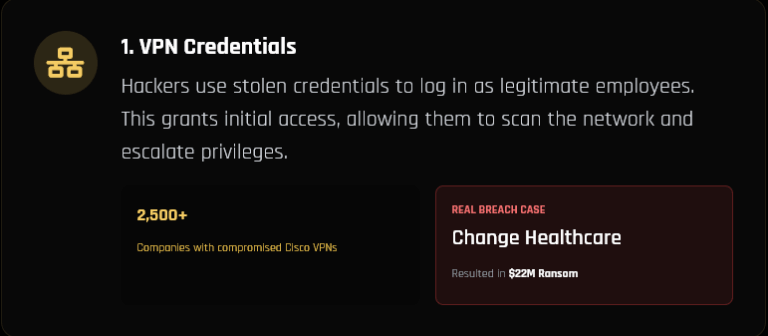
How Hackers Really Use Infostealers – Hudson Rock Infographic HUDSON ROCK HOW HACKERS REALLY USE INFOSTEALERS An analysis of the specific tactics used in the
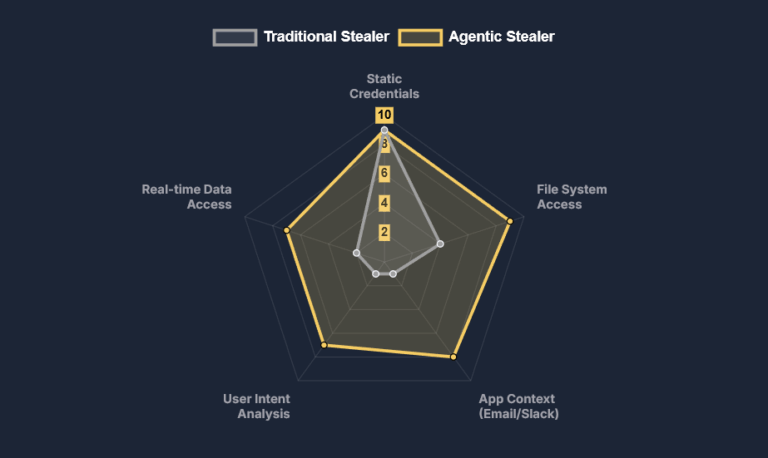
Infographic: The Agentic OS & Hudson Rock Defense HUDSON ROCK Threat Intelligence Report The Agentic OS Attack Vector Microsoft’s new Windows 11 update centralizes data
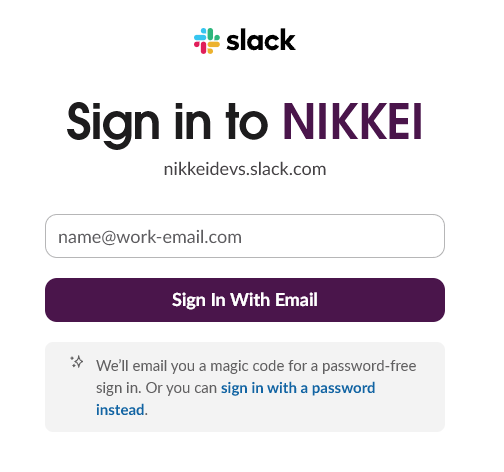
Over 17,000 employees and partners now face the fallout from a breach that started with a single infostealer infection on a Japanese computer in August

To completely understand what’s going on in a market that has been growing in the last years I found mandatory to know which players are

In a swift operation that underscores Russia’s growing crackdown on domestic cyber threats, the Ministry of Internal Affairs (MВД) has arrested a group of young
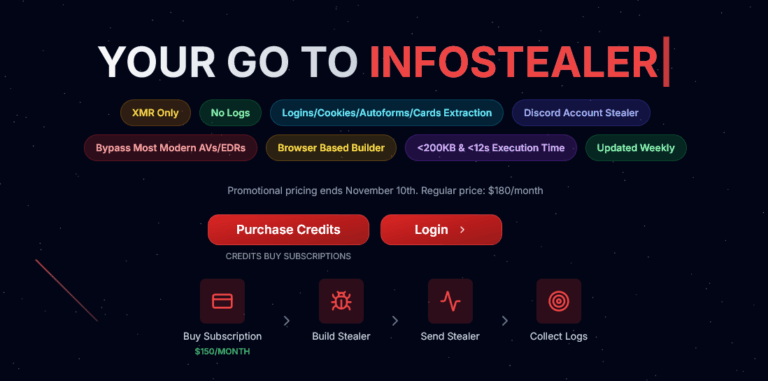
In the ever-evolving landscape of cyber threats, Hudson Rock‘s research team has uncovered a potent new Infostealer builder: Logins(.)zip. Marketed as the “go-to infostealer” on
It is human nature to be competitive, to try your best when competing against others. It is no different when it comes to video games.
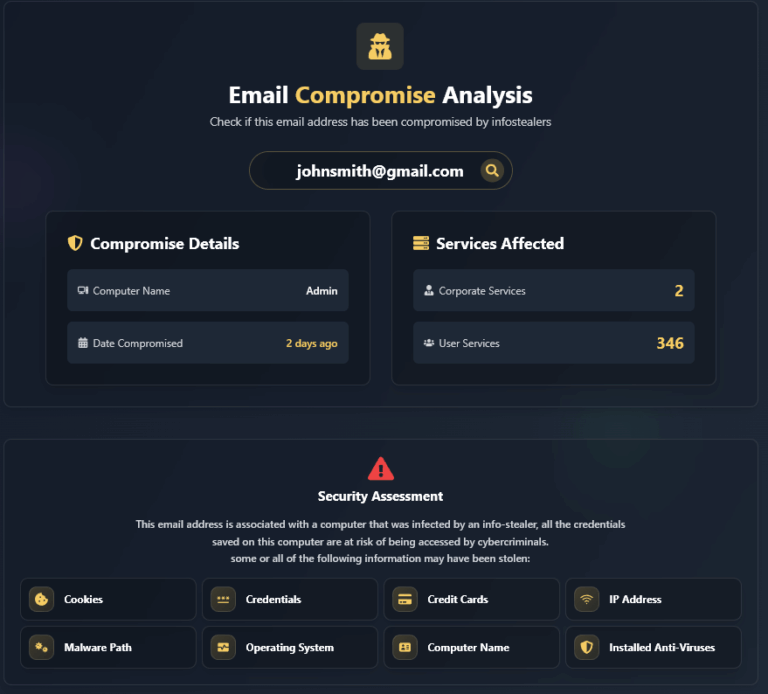
How to Check if an Email Address Has Been Compromised To determine if an email address has been affected by an Infostealer infection and has
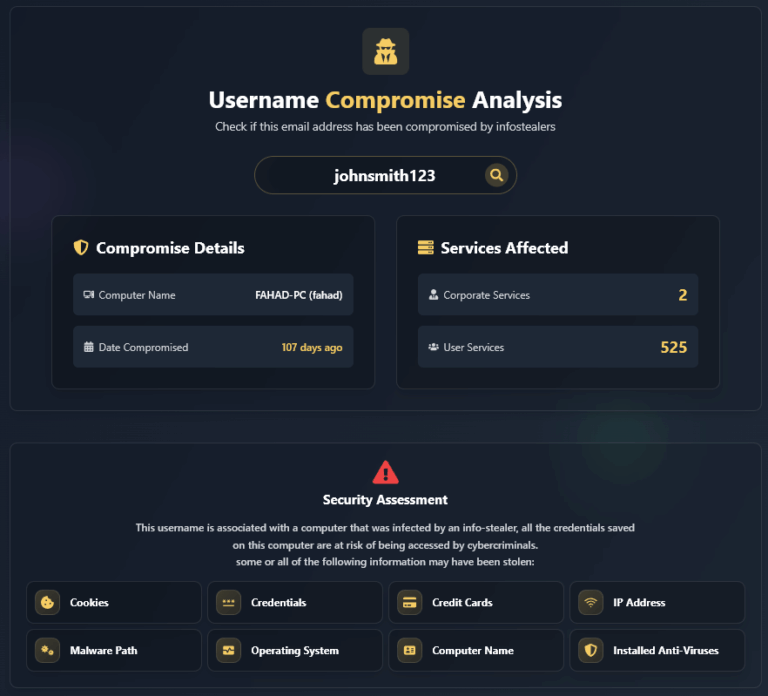
How to Check if a Username Has Been Compromised To determine if a username has been affected by an Infostealer infection and has leaked credentials
The Incident Breakdown At Hudson Rock, we’ve been closely analyzing the cyber incidents that struck Collins Aerospace, a subsidiary of RTX Corporation, during the week
To completely understand what’s going on in a market that has been growing in the last years I found mandatory to know which players are
