Redline Stealer: A Novel Approach
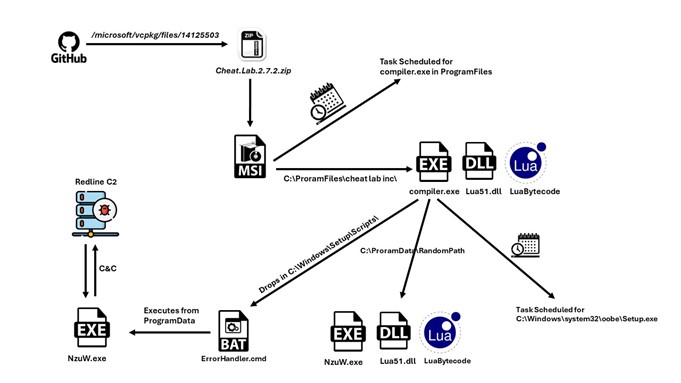
A new packed variant of the Redline Stealer trojan was observed in the wild, leveraging Lua bytecode to perform malicious behavior.McAfee telemetry data shows this
Home » C2 Servers
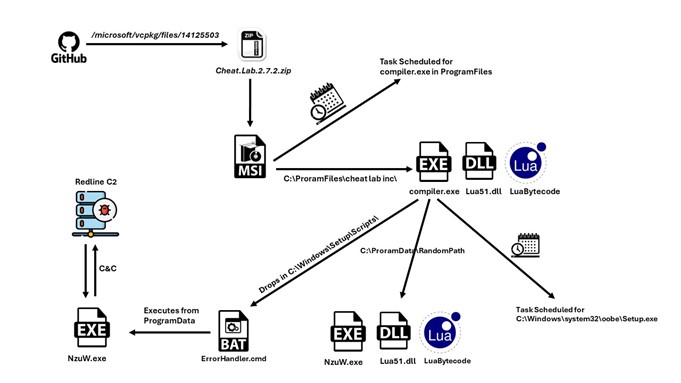
A new packed variant of the Redline Stealer trojan was observed in the wild, leveraging Lua bytecode to perform malicious behavior.McAfee telemetry data shows this
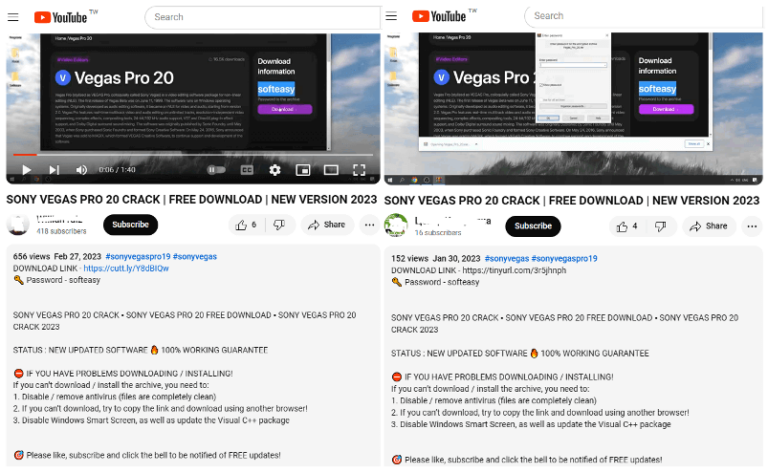
FortiGuard Labs recently discovered a threat group using YouTube channels to distribute a Lumma Stealer variant…
This method can be applied to multiple other C2 servers that we come across on a daily basis to check for any security misconfigurations…

Recordbreaker is also the first User Agent found on Raccoon V2 builds in order to communicate to C2 servers…
How One Infostealer Infection Solved a Global Supply Chain Mystery and Unmasked DPRK Spies in U.S. Crypto. Researcher & Law Enforcement Notice: Hudson Rock welcomes
Infected by GTA 5 Cheats: How an Infostealer Infection Unmasked a North Korean Agent State-sponsored cybercrime is evolving. Foundational research by Kudelski Security, utilizing Hudson

My friend Alex Bovicelli just shared some excellent insights on the current SMB ransomware wave. If you want to understand the reality of the threat
