Analysis
From LNK Payload to Infostealer Source Code
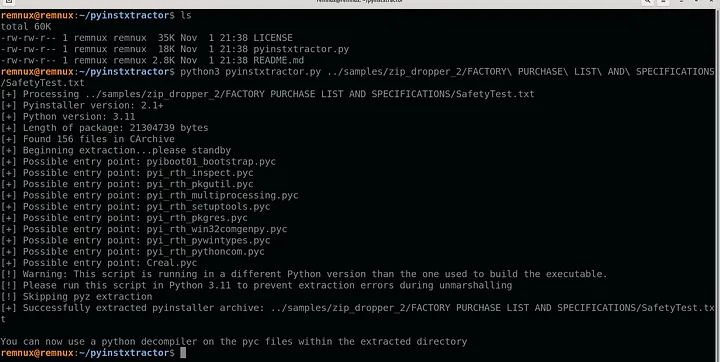
A ZIP/LNK payload and, with some luck, we will end up identifying the infostealer that is being dropped and its source code…
Home » Infostealer Source Code
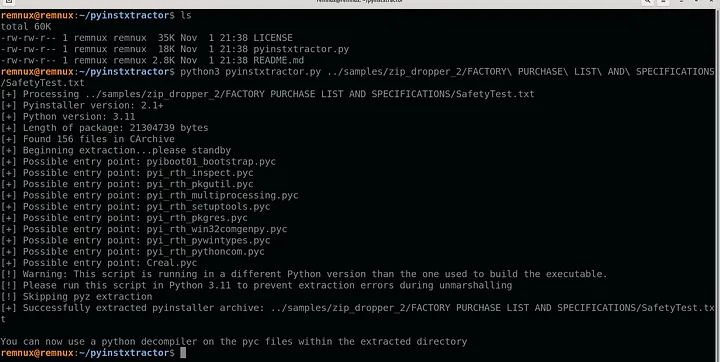
A ZIP/LNK payload and, with some luck, we will end up identifying the infostealer that is being dropped and its source code…
How One Infostealer Infection Solved a Global Supply Chain Mystery and Unmasked DPRK Spies in U.S. Crypto. Researcher & Law Enforcement Notice: Hudson Rock welcomes
Infected by GTA 5 Cheats: How an Infostealer Infection Unmasked a North Korean Agent State-sponsored cybercrime is evolving. Foundational research by Kudelski Security, utilizing Hudson

My friend Alex Bovicelli just shared some excellent insights on the current SMB ransomware wave. If you want to understand the reality of the threat
