
Hamster Kombat Players Threatened by Spyware & Infostealers
In the past few months, the Telegram clicker game Hamster Kombat has taken the world of cryptocurrency game enthusiasts by storm. Even though the gameplay,

In the past few months, the Telegram clicker game Hamster Kombat has taken the world of cryptocurrency game enthusiasts by storm. Even though the gameplay,

Key Points Introduction Threat actors continually evolve their tactics to stay ahead of detection. Traditional methods of malware distribution via emails containing malicious attachments are

American cybersecurity company KnowBe4 says a person it recently hired as a Principal Software Engineer turned out to be a North Korean state actor who
On July 22, 2024, CrowdStrike Intelligence identified a Word document containing macros that download an unidentified stealer now tracked as Daolpu. The document impersonates a Microsoft

Hudson Rock’s database, with tens of millions of computers infected worldwide, enables cybersecurity and law enforcement customers to investigate suspicious infected computers that are using
In the ever-evolving world of cybersecurity, staying ahead of emerging threats is crucial. One such threat that has been gaining traction is info stealers. These
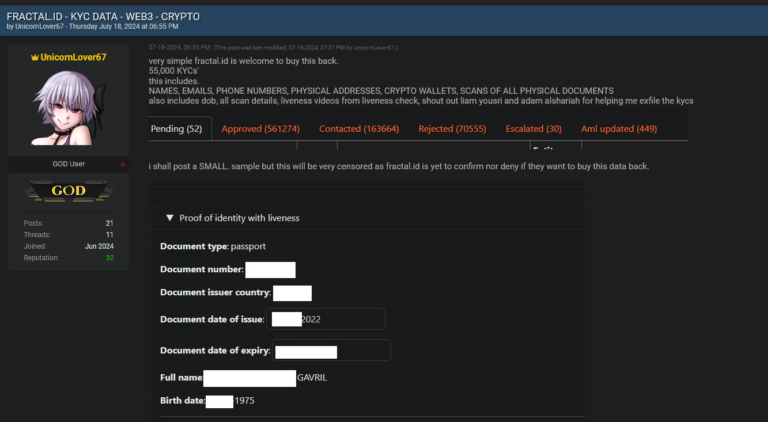
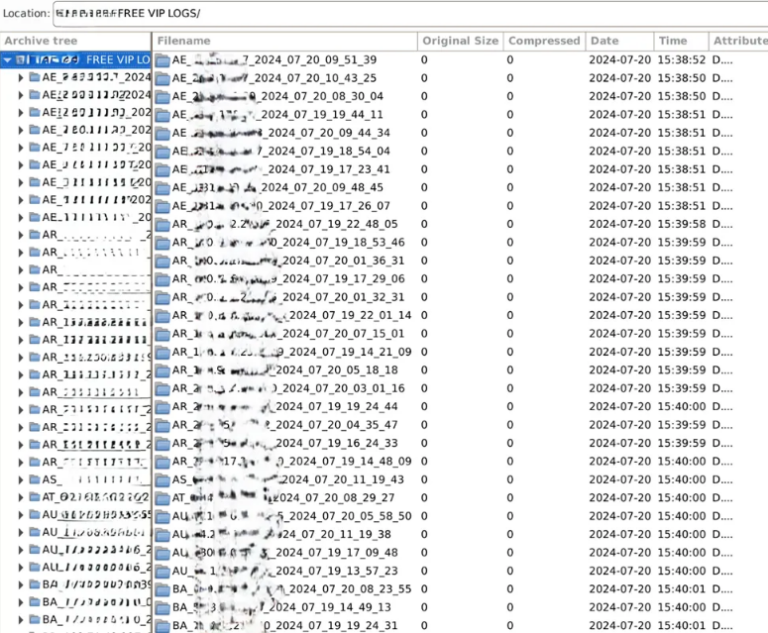
On July 14th, 2024 Blockchain identity platform Fractal ID suffered a data breach resulting in sensitive KYC data of over 55,000 individuals being exposed online.

In one of the most significant data breaches in recent history, hackers stole AT&T customers’ call and text metadata spanning several months. Hackers broke into
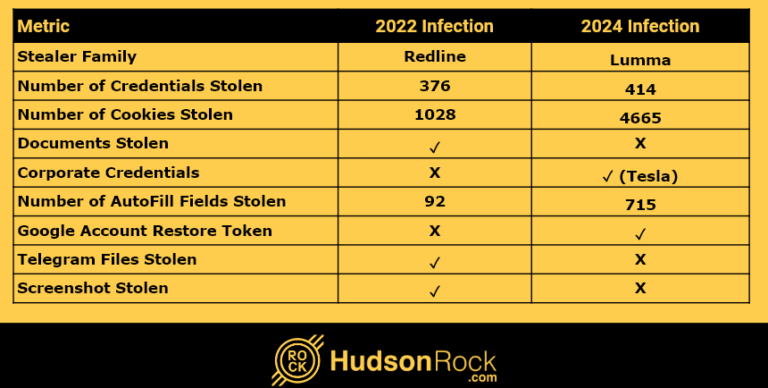
Having your data stolen once is bad enough, but for some people, it happens repeatedly. Infostealer infections are not a new phenomenon in the cybersecurity

Executive Summary On Tuesday, June 18th, 2024, Rapid7 initiated an investigation into suspicious activity in a customer environment. Our investigation identified that the suspicious behavior
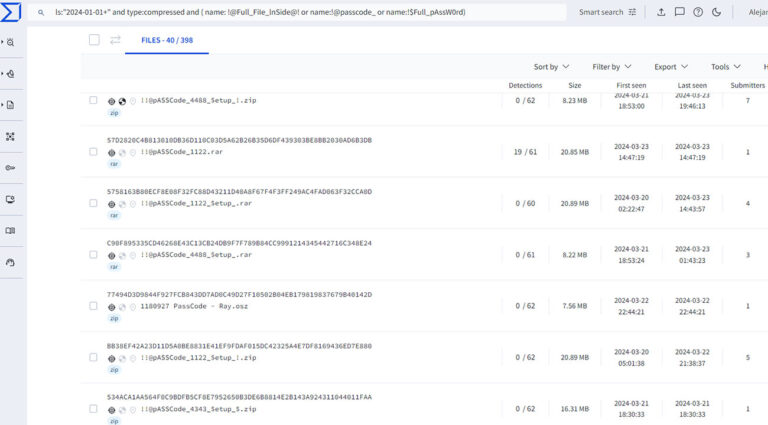
A potential shift in Infostealers might be happening again. Traditionally, teams of cybercriminals develop an Infostealer family (variant) such as Redline, Lumma, Raccoon, etc., and
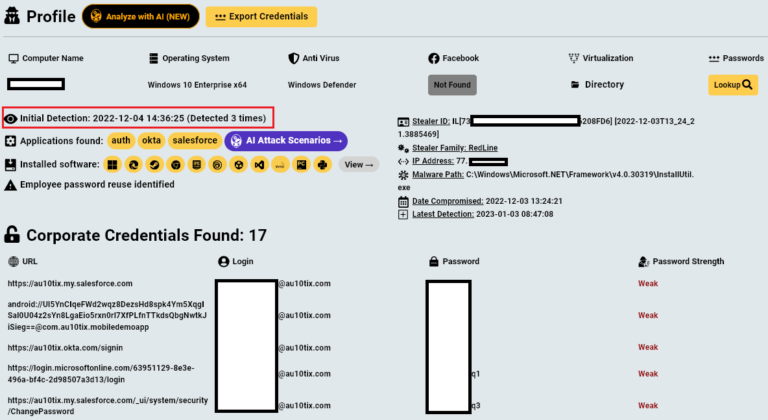
AU10TIX, a company that verifies the identities of TikTok, Uber, and X users, sometimes by processing photographs of their faces and pictures of their drivers’
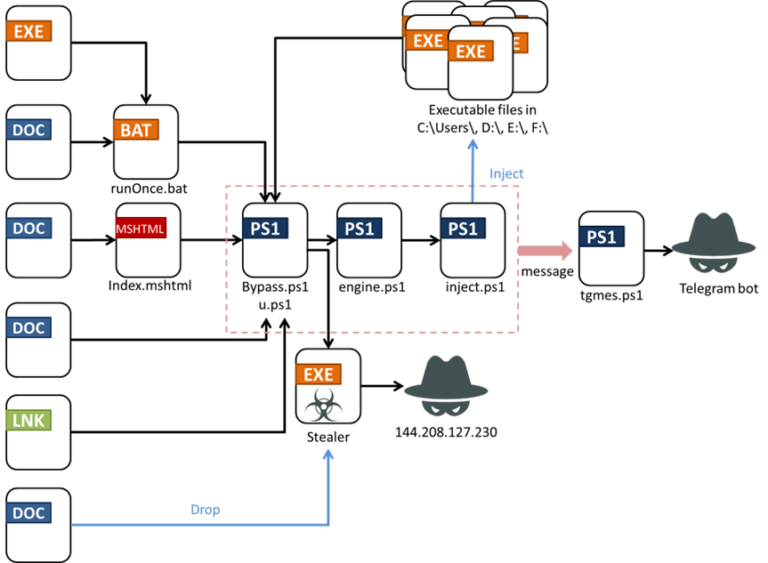
Affected Platforms: Microsoft WindowsImpacted Users: Microsoft WindowsImpact: The stolen information can be used for future attackSeverity Level: High The past few years have seen a significant increase in the
Case Summary It was a quiet Monday morning in March 2024 when the EDR researchers with our Trellix Advanced Research Center identified an interesting sequence

Learn about Infostealers with actual real life breaches caused by Infostealer infections with Leonid Rozenberg, Hudson Rock’s Head of Partnerships & Integrations. To discover how

Infostealers commit close to the perfect crime. They sneak into your computer, grab your logins, passwords, and anything of value, and then delete themselves on
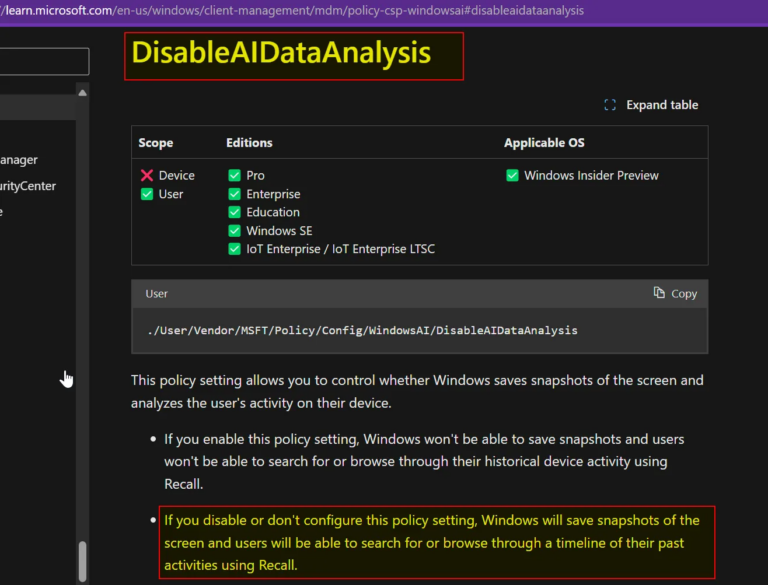
I wrote a piece recently about Copilot+ Recall, a new Microsoft Windows 11 feature which — in the words of Microsoft CEO Satya Nadella- takes “screenshots”
EXECUTIVE SUMMARY At CYFIRMA, we are committed to offering up-to-date insights into prevalent threats and tactics employed by malicious actors who target organizations and individuals.
