Hudson Rock is an Israeli cybercrime intelligence company. We specialize in sourcing compromised credentials from threat actors, which we then put to use in “Cavalier” — a threat-intelligence monitoring and notification product for cybersecurity professionals, that notifies them about compromised credentials of Employees, Partners and Users.
Threat actor “La_Citrix” is known for hacking companies and selling access to their citrix/vpn/RDP servers or otherwise for selling info-stealer logs from computer infections he is in charge of, he mainly operates on Russian speaking cybercrime forums from 2020 up until today.

The image shows La_Citrix’s exploit.in profile and threads that were opened by him, in which he attempts to sell info-stealer logs and access to various companies.
As it turns out, while infecting computers, La_Citrix accidentally infected his own computer and likely ended up selling it without noticing.
We identified La_Citrix while looking at other hackers who were infected by info-stealers and had access to prominent cybercrime forums.

Several compromised users of famous cybercrime forum “exploit.in”, one of which is la_citrix. This image is from Hudson Rock’s Cavalier.
This led us to investigate La_Citrix’s computer further:

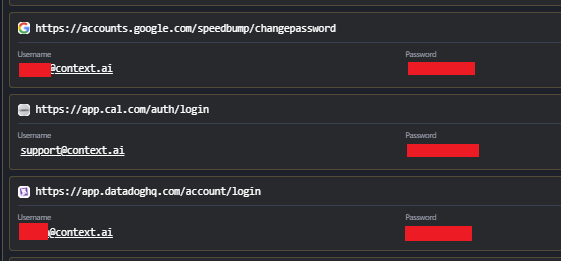
Raw credentials data from La_Citrix’s computer, showing he is registered to multiple cybercrime forums under the same alias “La_Citrix” or “Lacitrix”.
It is not uncommon for hackers to accidentally get infected by info-stealers, just as employees of highly technological companies often do. For example, raidforums.com, a prominent cybercrime forum that was shut down by law enforcement has over 7,000 compromised users in Hudson Rock’s database, many of which are hackers.

Compromised users of Raidforums.com in Hudson Rock’s Cavalier.
When going over the data from La_Citrix’s computer, researchers were surprised to see that Hudson Rock’s API determined this individual to be an employee at almost 300 different companies, but after seeing the credentials he had stored on the computer, they realized why:
Surprisingly, it was discovered that this threat actor orchestrated all of the hacking incidents using his personal computer, and browsers installed on that computer stored corporate credentials used for the various hacks.

The image shows a response from Hudson Rock’s API determining La_Citrix’s computer is an employee at 291 companies, and on the right side are actual corporate credentials from La_Citrix’s computer used to access various company servers.
Interestingly, La_Citrix’s method of infiltrating companies is done via corporate credentials found on computers that were infected by info-stealers. When we examined the corporate credentials La_Citrix had access to, we discovered most of them were already found in Hudson Rock’s Database.

Almost all of the corporate credentials from infected computers used by La_Citrix to infilitrate companies were already in Hudson Rock’s database.
Data from La_Citrix’s computer such as “Installed Software” reveals the real identity of the hacker, his address, phone, and other incriminating evidence such as “qTox”, prominent messenger used by ransomware groups, being installed on the computer.

The left image shows data such as first and last name, address, and phone that were stored in the “auto-complete” data stored by the browser. The right image shows some additional technical information from the computer, along with the installed software.
This is not the first time we’ve identified hackers who accidentally got IDENTIFIED IN INFOSTEALER INFECTIONS, and we expect to see more as info-stealer infections grow exponentially.
Hudson Rock will forward the data to relevant law enforcement agencies.
To learn more about how Hudson Rock protects companies from imminent intrusions caused by info-stealer infections of employees, partners, and users, as well as how we enrich existing cybersecurity solutions with our cybercrime intelligence API, please schedule a call with us, here: https://www.hudsonrock.com/schedule-demo
Hudson Rock also provide access to various free cybercrime intelligence tools that you can find here: www.hudsonrock.com/free-tools