With cyber espionage on the rise, opportunistic Infostealer malware, designed to harvest credentials indiscriminately, is being repurposed by Advanced Persistent Threat (APT) groups to devastating effect. Hudson Rock‘s threat intelligence reveals a global wave of compromised Ministry of Foreign Affairs (MOFA) email accounts, from Saudi Arabia’s mofa.gov.sa to South Korea’s mail.mofa.go.kr, the United Arab Emirates’ mofa.gov.ae, Qatar’s mofa.gov.qa, and others, including Oman.
When these infections, often triggered by phishing or unsafe downloads, compromise diplomats with official access, they hand state-sponsored actors authentic credentials to craft highly convincing malware campaigns for intelligence gathering.
This article explores how infostealers escalate into geopolitical weapons, using recent incidents and a deep dive into Oman’s compromised embassies to highlight risks and prevention strategies.
A Global Net of Opportunistic Infections
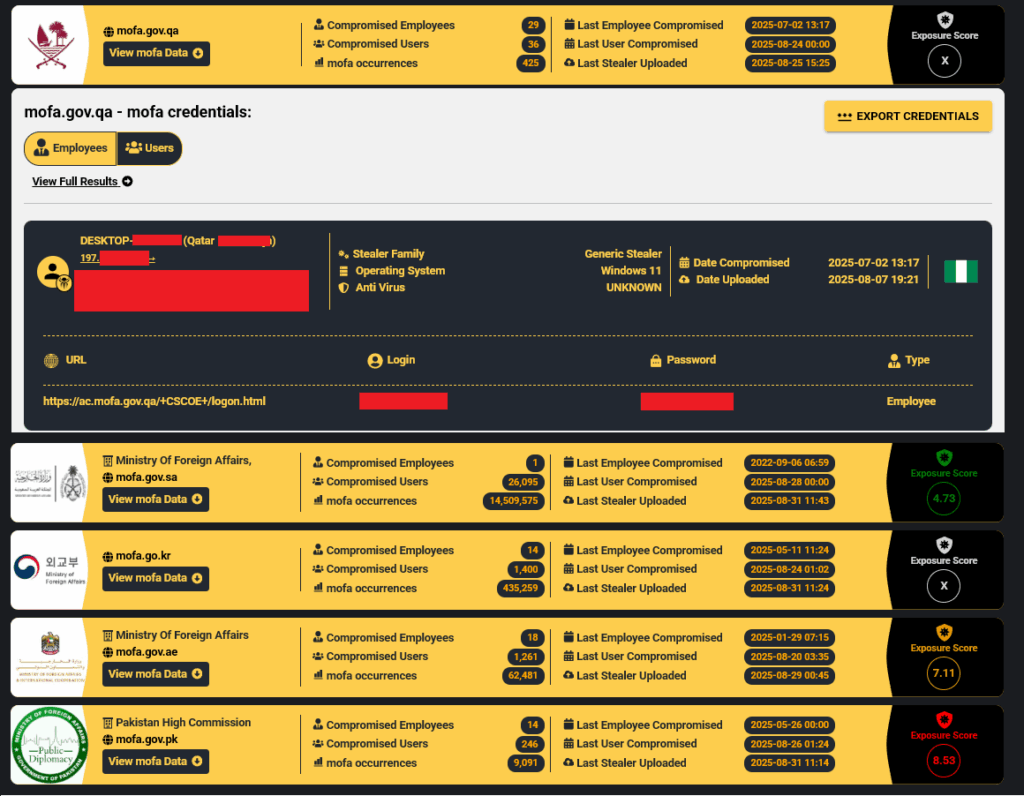
Hudson Rock’s platform, Cavalier, has detected Infostealer infections compromising MOFA credentials across multiple nations, exposing diplomatic infrastructure to exploitation:
- Saudi Arabia (mofa.gov.sa): Credentials tied to the Kingdom’s MFA, vulnerable to misuse in Middle Eastern diplomacy.
- South Korea (mail.mofa.go.kr): Infections hitting Seoul’s foreign affairs systems, risking exposure of Indo-Pacific negotiations.
- United Arab Emirates (mofa.gov.ae): Breaches at Abu Dhabi’s MFA, a key player in Gulf diplomacy.
- Qatar (mofa.gov.qa): Compromised accounts in Doha, critical for mediating conflicts like Gaza.
- Others: Detections span MFAs in Europe, Asia, Africa, and the Americas, showing a widespread threat.
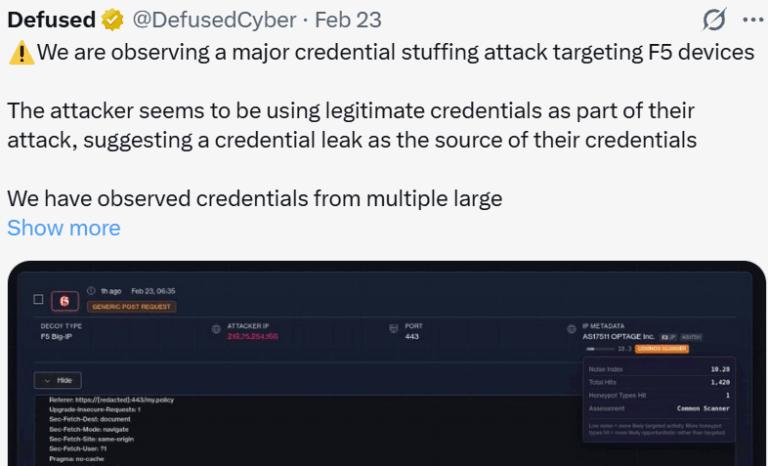
These infections are opportunistic, often infecting diplomats via phishing or malicious downloads. When credentials belong to officials with MFA mailbox access, they become high-value targets for APTs seeking geopolitical leverage.
From Opportunistic Theft to Targeted Espionage
Infostealers like StealC, Lumma, or Redline cast wide nets, but their compromise of diplomatic credentials enables APTs to execute precise, credible attacks. Two cases illustrate how these stolen credentials fuel intelligence operations with real-world consequences:
Dream Security Group’s Omani Phishing Campaign
In August 2025, Dream Security Group exposed a spear-phishing campaign leveraging a compromised Omani MFA email (masked as ******@fm.gov.om, tied to the Paris embassy) to distribute malware. Attackers, likely Iranian-aligned groups like Homeland Justice or MOIS, used the stolen credential to send deceptive emails posing as diplomatic invitations to over 195 global recipients, including the UN and World Bank. Word attachments with VBA macros deployed “sysProcUpdate,” a malware that collected data and connected to a C2 server via a Jordanian NordVPN node.
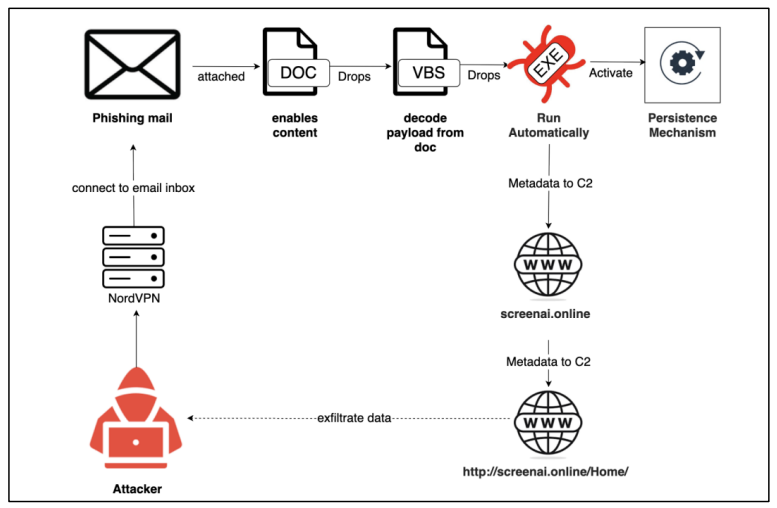
Timed during Middle East ceasefire talks, the campaign aimed to harvest intelligence and disrupt diplomacy. The authentic Omani email made the lures highly convincing, showing how APTs exploit infostealer-compromised credentials for strategic advantage.
While this accident is not directly tied to an Infostealer infection resulting in the hacking of the official Omani mailbox, it does show how once the access is obtained, it can be leveraged for cyber-political gains.
Bitter APT’s Exploitation of PTCL in Pakistan
During the 2025 India-Pakistan ‘Operation Sindoor’ conflict, Hudson Rock linked Bitter APT’s attack on Pakistan Telecommunication Company Limited (PTCL) to credentials stolen via infostealers. A Counter Terrorism Department (CTD) email at Islamabad Police, compromised in 2024 via cracked software, provided the entry point.
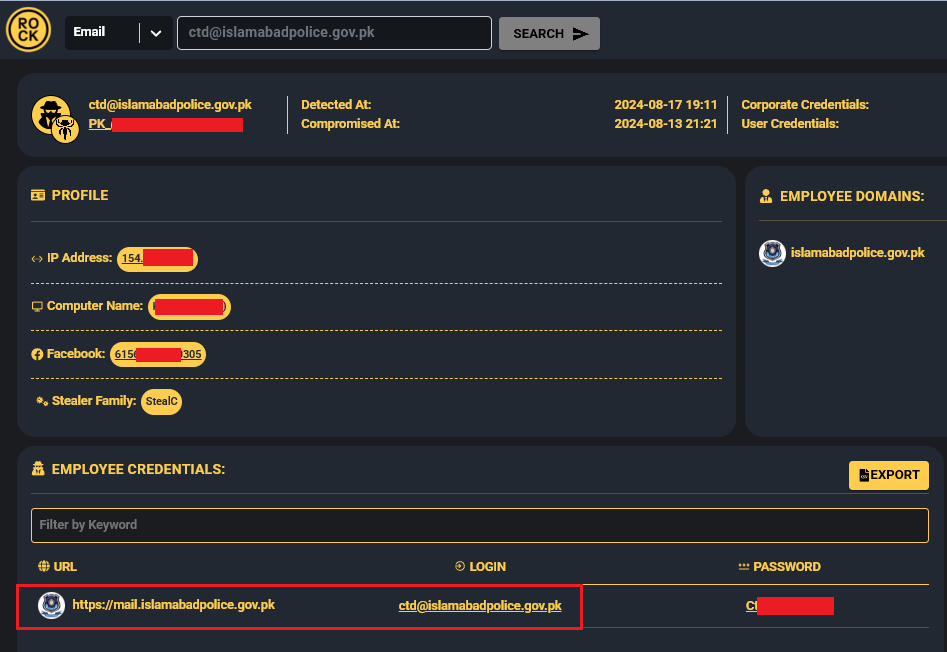
These credentials enabled Bitter APT to craft targeted phishing emails delivering WmRAT, compromising PTCL’s critical infrastructure.
The credentials’ authenticity allowed seamless intelligence collection during conflict, showing how infostealers serve as a stepping stone for APTs to achieve geopolitical goals.
Deep Dive: Oman’s Compromised Embassies as a Case Study
Oman’s MOFA infections highlight the path from opportunistic infection to geopolitical risk. Hudson Rock detected infostealers compromising two diplomatic emails:
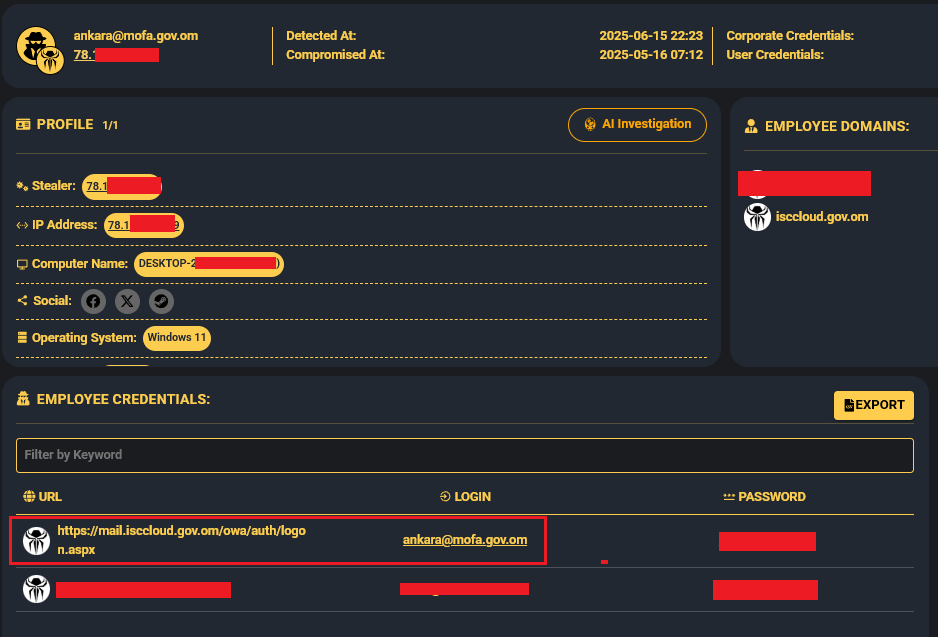
- [email protected] (Embassy of the Sultanate of Oman in Ankara, Turkey) – a May 2025 Infostealer infection of a computer operating out of Turkey resulted in hundreds of credentials stolen from the machine, among them are corporate credentials to the official MOFA mailbox of the Embassy of Oman in Ankara:
- [email protected] (Embassy of Oman in Brasilia, Brazil) – a June 2023 Redline Infostealer infection of a computer operating out of Brazil resulted in hundreds of credentials stolen from the machine, among them are corporate credentials to the official MOFA mailbox of the Embassy of Oman in Brasilia, Brazil:
 These credentials, likely stolen through phishing or downloads, could enable APTs to impersonate Omani diplomats, intercept communications on Gulf security or mediation efforts, or launch convincing phishing campaigns, as seen in the Paris embassy case. Oman’s neutral role in diplomacy amplifies the risk, where breaches could escalate tensions through leaked intelligence or missteps.
These credentials, likely stolen through phishing or downloads, could enable APTs to impersonate Omani diplomats, intercept communications on Gulf security or mediation efforts, or launch convincing phishing campaigns, as seen in the Paris embassy case. Oman’s neutral role in diplomacy amplifies the risk, where breaches could escalate tensions through leaked intelligence or missteps.
Disrupting the Infostealer-to-APT Pipeline
Infostealers exploit human error, but their exploitation by APTs demands proactive defense. Tools like Hudson Rock’s Cavalier detect compromised credentials in real-time, enabling:
- Credential Monitoring: Scan infostealer databases for MOFA domains to identify breaches early.
- Behavioral Detection: Flag suspicious email activity or process executions (e.g., macro-enabled documents).
- Training and Tools: Educate diplomats on phishing risks; deploy EDR to catch infostealer signatures.
To learn more about how Hudson Rock protects companies from imminent intrusions caused by info-stealer infections of employees, partners, and users, as well as how we enrich existing cybersecurity solutions with our cybercrime intelligence API, please schedule a call with us, here: https://www.hudsonrock.com/schedule-demo
We also provide access to various free cybercrime intelligence tools that you can find here: www.hudsonrock.com/free-tools
Thanks for reading, Rock Hudson Rock!
Follow us on LinkedIn: https://www.linkedin.com/company/hudson-rock
Follow us on Twitter: https://www.twitter.com/RockHudsonRock
Learn more about us: https://en.wikipedia.org/wiki/Hudson_Rock