How The Gentlemen Ransomware Group Operates: A Blueprint Built on Infostealer Credentials
A recent internal data leak from “The Gentlemen” ransomware-as-a-service (RaaS) group has provided the cybersecurity community with a rare, unfiltered look into their daily operations. Exposed on underground forums, the internal communications shed light on exactly how ransomware affiliates organize, breach, and extort global organizations.
But among the many technical details revealed in Checkpoint Research’s comprehensive analysis (“Thus Spoke… The Gentlemen”), one operational pattern stands out prominently: their heavy reliance on infostealer credential logs for initial access.

Searching the Logs: Snusbase and Credential Exploitation
Checkpoint’s analysis highlights that rather than constantly burning expensive zero-days, The Gentlemen operators frequently take the path of least resistance. They exploit the massive underground ecosystem of stolen credentials to pivot deeper into corporate networks.
“The group claims to usually gain initial access through exposed edge devices… They combine different methods to achieve this, including credential brute‑forcing… OWA/M365 credential logs… Screenshots shared in the chats also show them searching for accounts and credentials in data-breach search engines. Once they obtain a foothold, they treat these systems as pivots to move deeper into the internal network.”
— Checkpoint Research
The usage of specialized data-breach search engines is critical to their operational workflow. The operators actively scour aggregated infostealer logs to identify valid employee logins, essentially using past malware infections as an open door.
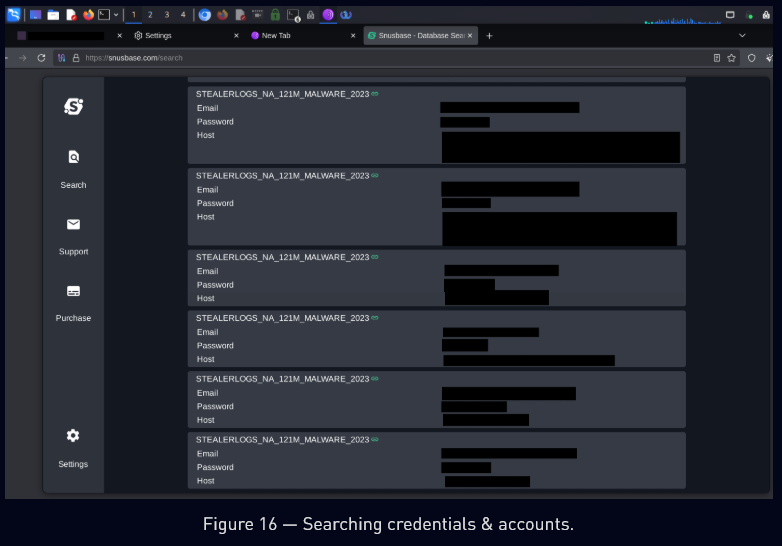
Leaked chats show the group uses Snusbase to actively search for compromised infostealer logs and credentials.
This focus on credential exploitation isn’t just an ad-hoc tactic used by low-level affiliates; it is baked directly into the group’s organizational structure. The leaked data reveals distinct roles within the gang, with specific threat actors dedicated solely to acquiring and weaponizing these logs. Checkpoint’s breakdown categorizes the threat actor known as “quant” directly under the purview of “credential logs.”
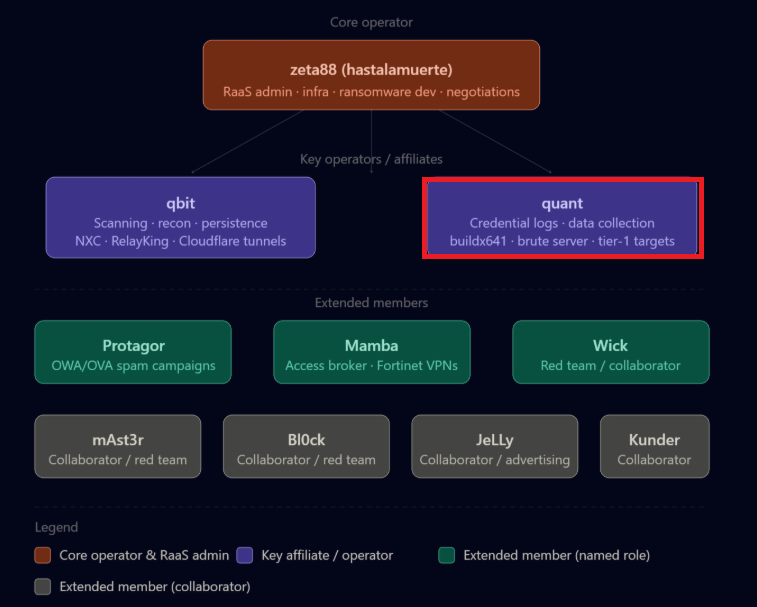
The Gentlemen organizational structure, showing threat actor “quant” is categorized by Checkpoint for handling “credential logs”.
A Rapidly Growing Trend: Lessons from the Coinbase Cartel
The Gentlemen’s reliance on infostealers is part of a massive paradigm shift in the cybercrime landscape. It is rapidly becoming the standard operational procedure for top-tier threat actors. Recently, Hudson Rock published extensive research on another group dubbed the Coinbase Cartel.
Unlike traditional ransomware groups, the Coinbase Cartel entirely abandoned the use of file encryptors. Instead, they relied exclusively on old Infostealer credentials (from malware strains like RedLine, Lumma, and Vidar) to silently compromise corporate cloud environments, FTP servers, and file transfer services. Hudson Rock’s intelligence confirmed that 80% of Coinbase Cartel’s 100+ victims had prior infostealer infections indexed in our Cavalier database.
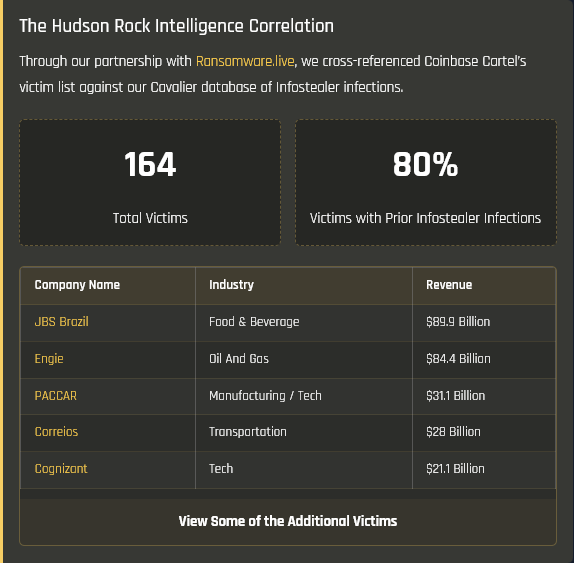
Hudson Rock data mapping Coinbase Cartel victims to prior infostealer infections. (Note: Threat actors bypassed endpoint defenses entirely by using valid, stolen employee credentials).
By bypassing encryptors, they siphoned massive amounts of sensitive data without triggering standard endpoint alerts. It serves as a stark reminder: an infostealer log is practically an indefinite backdoor into an organization until the exposed credentials are forcefully reset.
The Critical Need for Infostealer Monitoring
To combat this rising threat, monitoring for infostealer infections is no longer an optional security layer; it is a critical prerequisite to preventing ransomware attacks before the initial access phase even begins. Threat actors are counting on the fact that most organizations lack visibility into their compromised third-party contractors, partners, and off-network employees.
To emphasize this pipeline, Hudson Rock has partnered with Ransomware.live to track the exact correlation between active ransomware victims and prior infostealer infections. At ransomware.live/infostealer, the cybersecurity community can view direct threat intelligence tying catastrophic ransomware breaches back to the very credentials that enabled them.
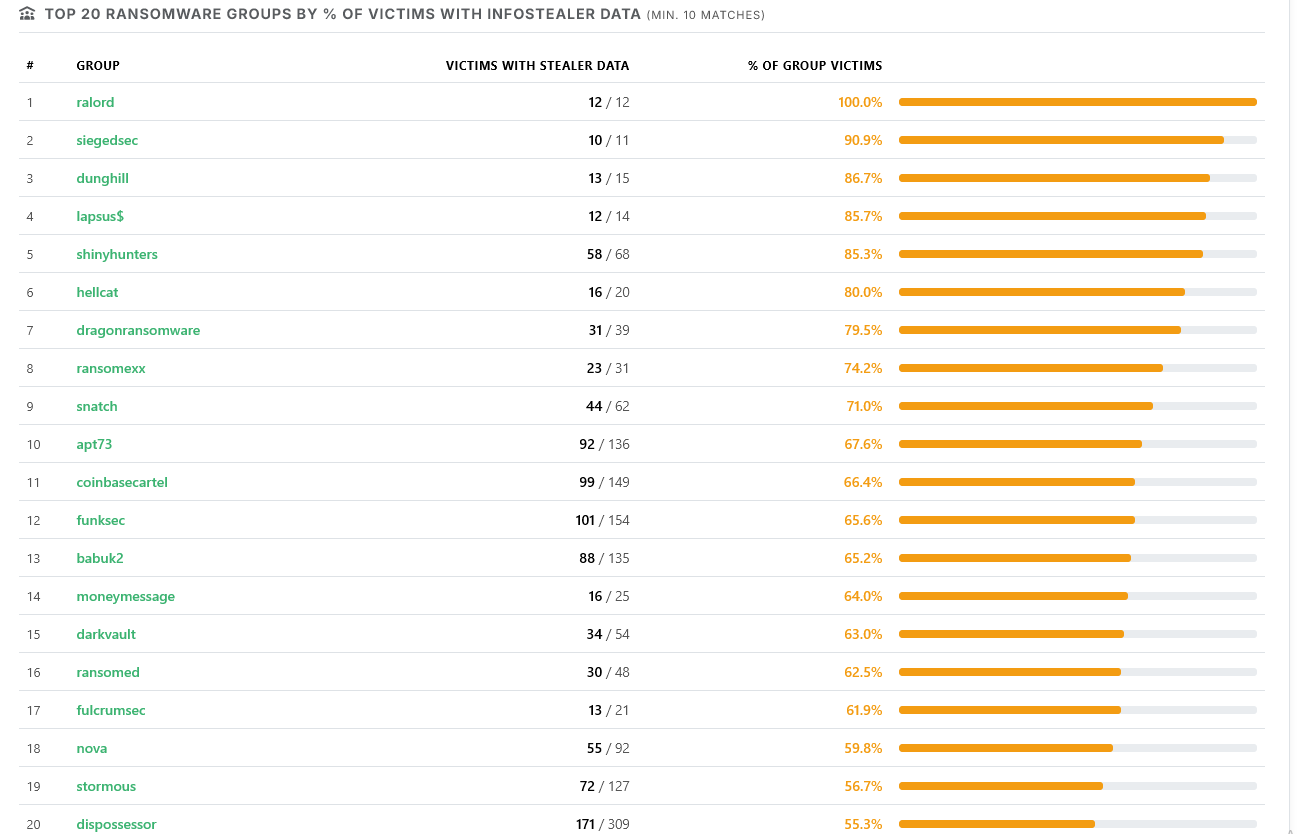
Hudson Rock data on Ransomware.live highlighting ransomware groups with a high percentage of victims suffering prior infostealer infections.
To learn more about how Hudson Rock protects companies from imminent intrusions caused by info-stealer infections of employees, partners, and users, as well as how we enrich existing cybersecurity solutions with our cybercrime intelligence API, please schedule a call with us, here:
https://www.hudsonrock.com/schedule-demo
We also provide access to various free cybercrime intelligence tools that you can find here:
www.hudsonrock.com/free-tools
Thanks for reading, Rock Hudson Rock!
Follow us on LinkedIn: https://www.linkedin.com/company/hudson-rock
Follow us on Twitter: https://www.twitter.com/RockHudsonRock




