The Missing Link: How Infostealers Fuel Ransomware Attacks (and Our New Partnership with Ransomware.live)
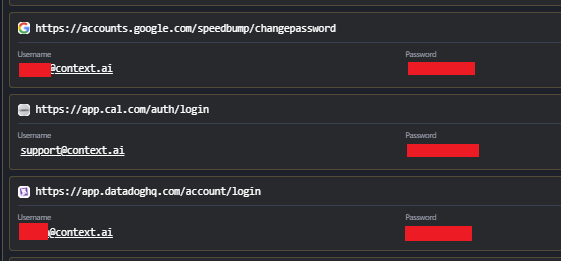
In the ever-evolving landscape of cyber threats, understanding the full lifecycle of an attack is crucial for defense. While ransomware deployment represents the devastating final act that grabs headlines, the silent precursor to these intrusions is frequently an Infostealer infection. Threat actors routinely rely on harvested credentials to gain that critical, initial foothold into corporate networks.
Empowering the Community: The Ransomware.live Partnership

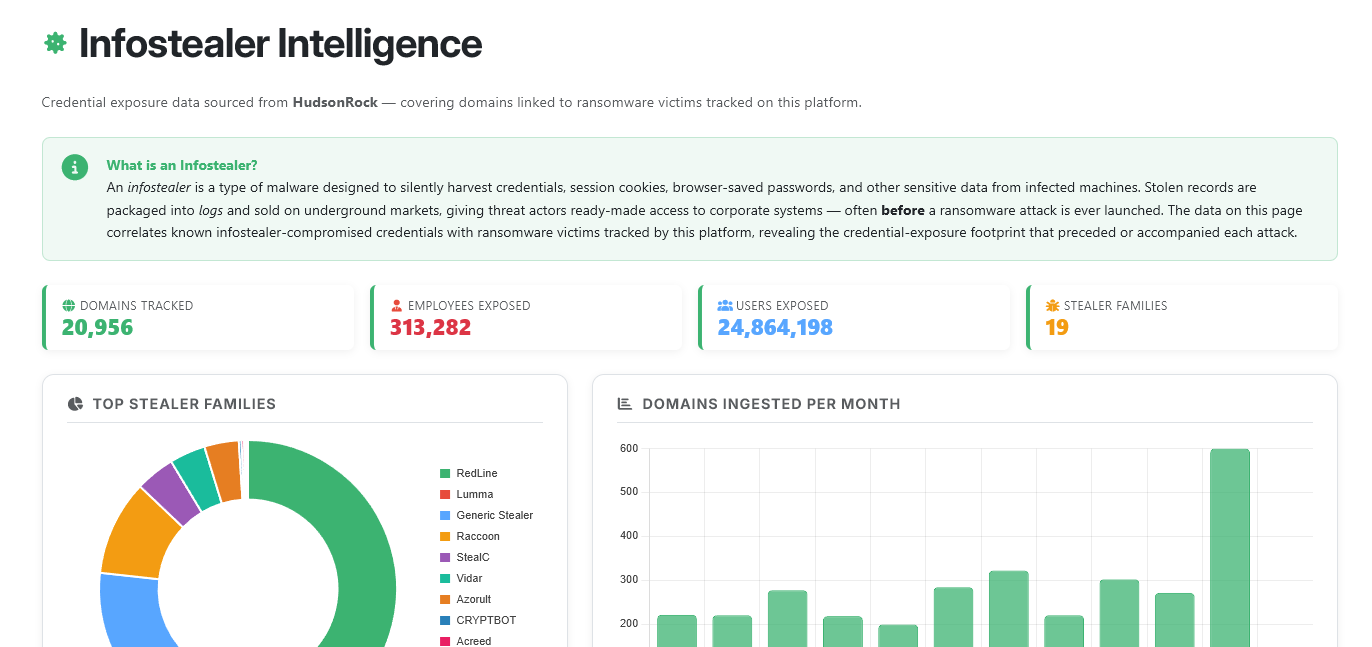
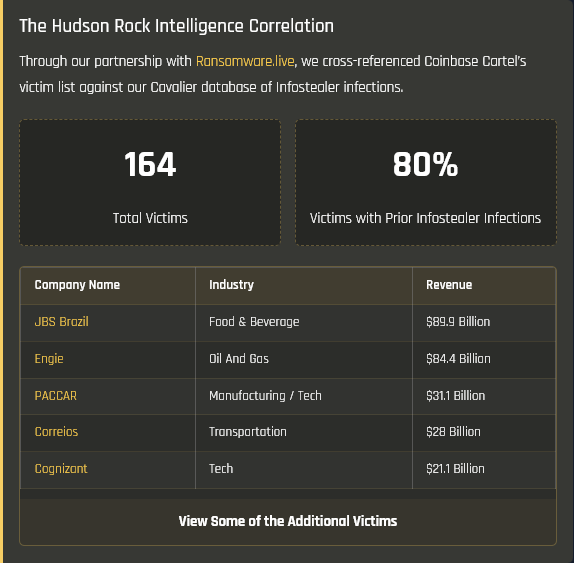
To shed light on this crucial connection, Hudson Rock is thrilled to announce a new partnership with Ransomware.live. Together, we have launched a dedicated dashboard highlighting the direct pipeline between Infostealers and ransomware groups.
You can view the new page here: https://www.ransomware.live/infostealer
Powered by Hudson Rock’s cybercrime intelligence data, this page provides the cybersecurity community with free, up-to-date statistics detailing just how frequently ransomware attacks originate from compromised employee or partner credentials.
The Data Speaks: Infostealers as the Initial Attack Vector
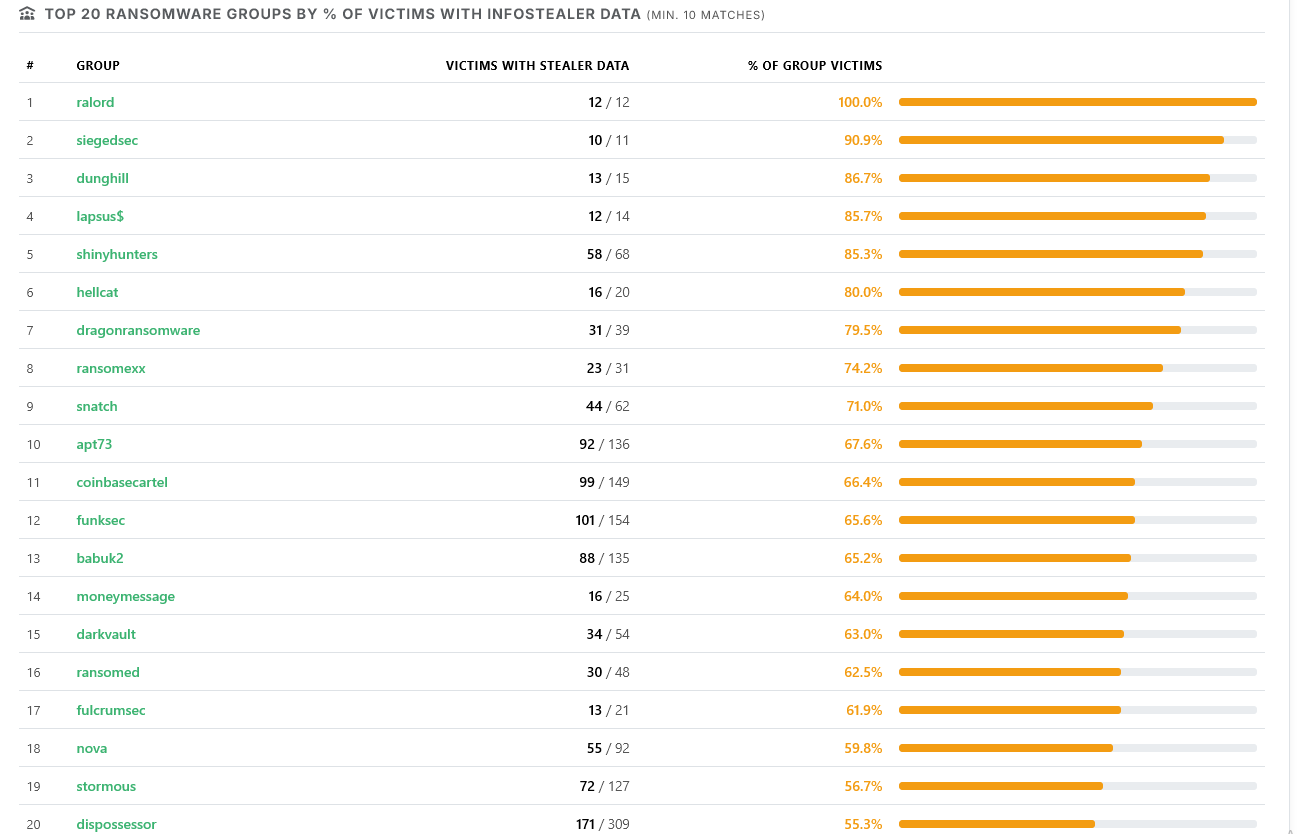
By cross-referencing publicly claimed ransomware victims with our extensive database of compromised computers, a stark reality emerges. Certain ransomware groups exhibit a massive percentage of victims who had prior Infostealer infections on their networks. This data definitively proves that Infostealers are not just a nuisance; they are a major precursor to enterprise-destroying ransomware events.
Real-World Impact: The “Coinbase Cartel” Discovery
This partnership isn’t just about high-level statistics; it provides actionable intelligence that unravels active campaigns.
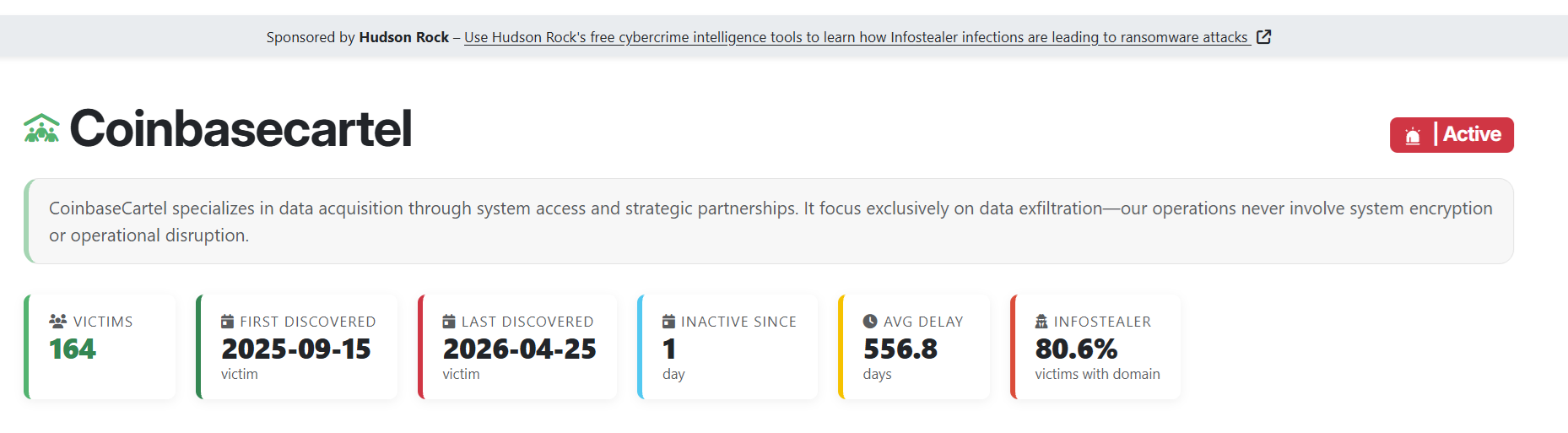
Thanks to the visibility provided by this joint effort, Hudson Rock was recently able to identify Infostealer data as the definitive initial attack vector used by one of the most active threat actors operating today. In our recent investigation, we uncovered how a group dubbed the “Coinbase Cartel” utilized harvested Infostealer credentials to bypass security perimeters.
This single vector fueled a massive, devastating spree, resulting in ransomware deployment across more than 100 different companies. You can read the full breakdown of this attack here: Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100-Company Ransomware Spree.
The evidence is undeniable: if you want to stop ransomware, you must first stop the Infostealer.
To learn more about how Hudson Rock protects companies from imminent intrusions caused by info-stealer infections of employees, partners, and users, as well as how we enrich existing cybersecurity solutions with our cybercrime intelligence API, please schedule a call with us, here:
https://www.hudsonrock.com/schedule-demo
We also provide access to various free cybercrime intelligence tools that you can find here:
www.hudsonrock.com/free-tools
Thanks for reading, Rock Hudson Rock!
Follow us on LinkedIn: https://www.linkedin.com/company/hudson-rock
Follow us on Twitter: https://www.twitter.com/RockHudsonRock