The New Era of Initial Access: How Infostealer Lookup Services are Changing Cybercrime
We are currently witnessing a massive shift in how cyberattacks begin. Infostealer lookup services are rapidly fueling a new era of initial access, transforming what used to be a complex hacking process into a simple, automated transaction. These platforms have effectively turned billions of compromised credentials and active session cookies into a highly searchable, low-cost commodity available to the masses.
In the past, accessing corporate networks required specialized skills. Today, anyone can simply log into a centralized database and pay via cryptocurrency to access conveniently structured logs. These logs contain the exact URL, login, and password data stolen from infected computers across the globe. Because these platforms require absolutely no KYC (Know Your Customer) verification, the barrier to entry for aspiring threat actors has completely disappeared.
Hiding in Plain Sight
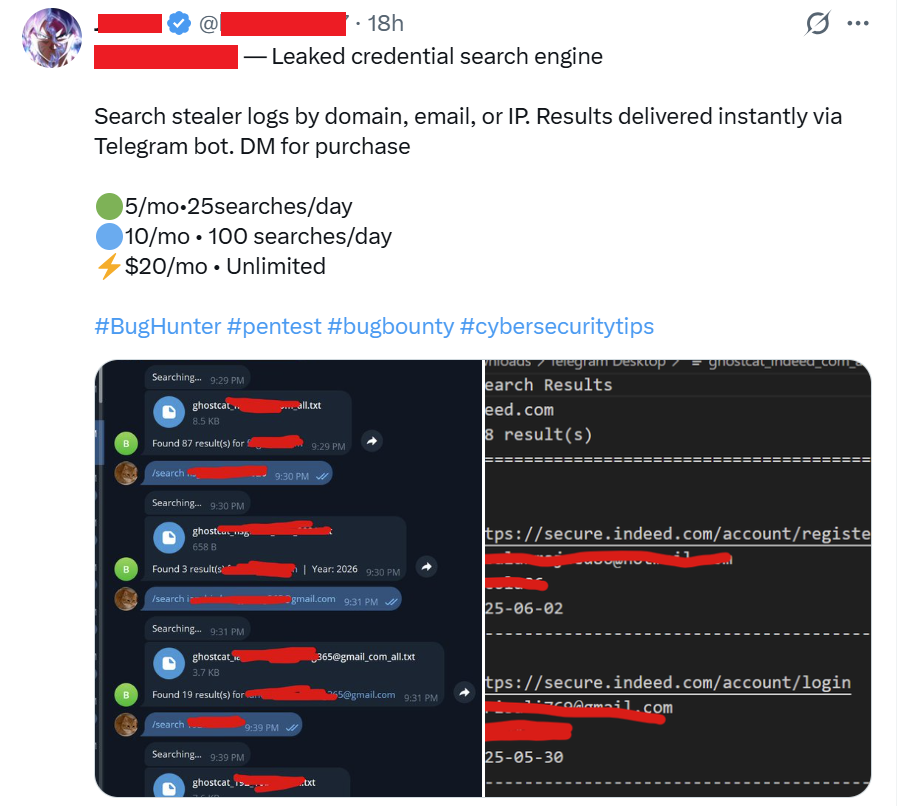
There is a common misconception that this level of illicit data exchange only happens in the deepest corners of the “Dark Web.” The reality is far more concerning. Look closely at the images below. What you are seeing is not hidden behind the Tor network. It is a sponsored Google search result. These platforms literally show up as paid advertisements whenever an amateur hacker searches for a “compromised credentials search” tool.
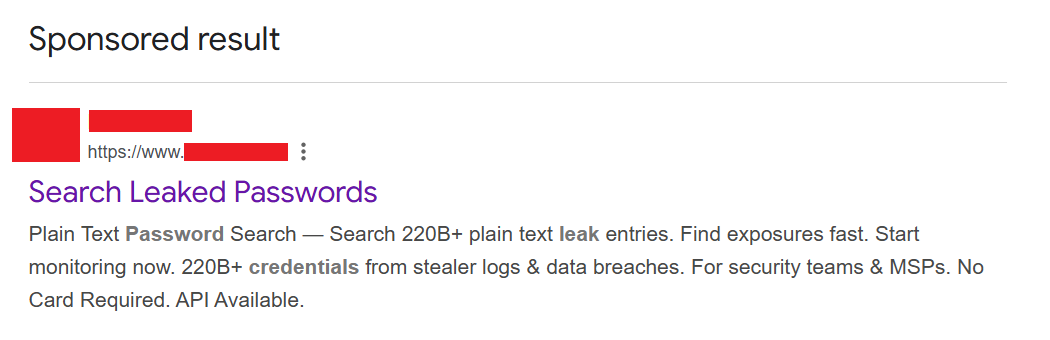
A startling reality: Google sponsored results openly advertising compromised credential search services to anyone looking for them.
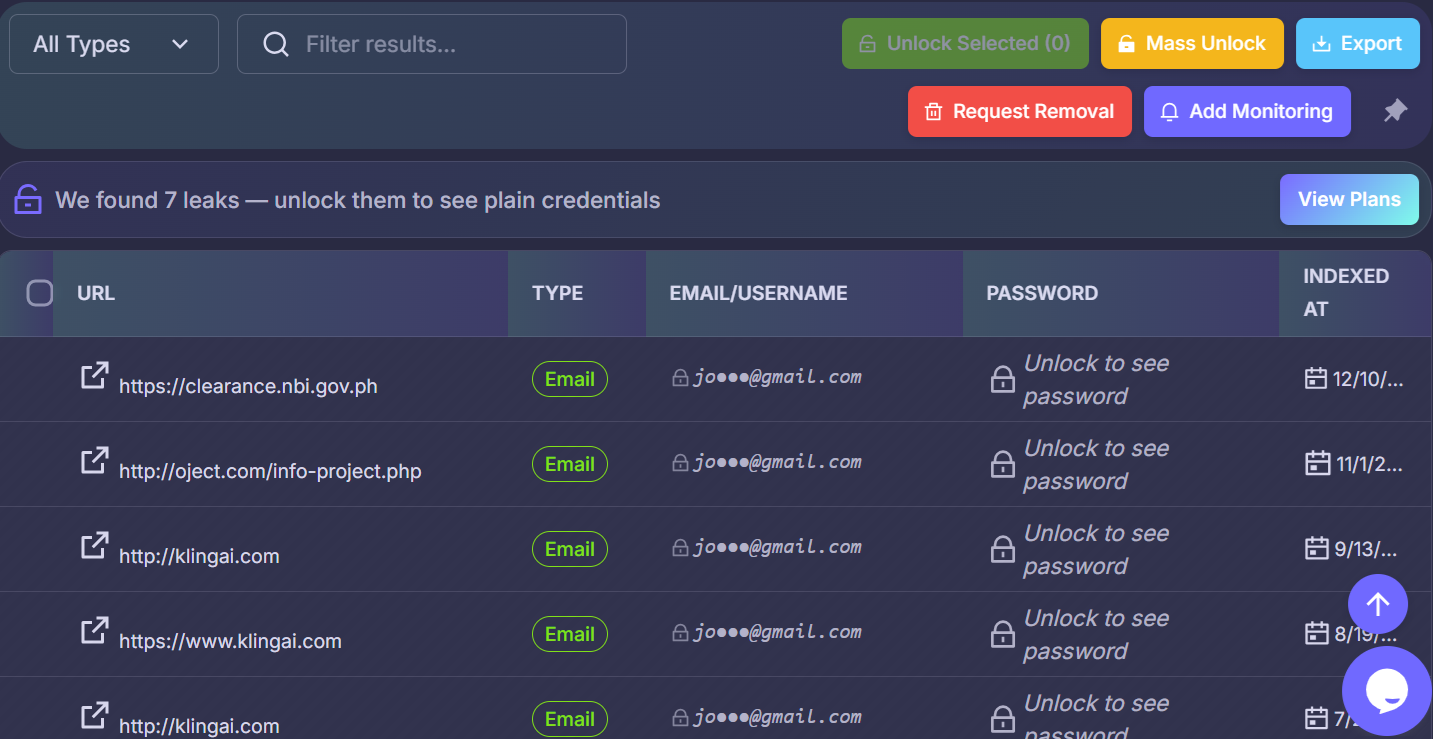
Inside the platform: A streamlined, user-friendly interface offering structured URL, login, and password data stolen from victims worldwide.
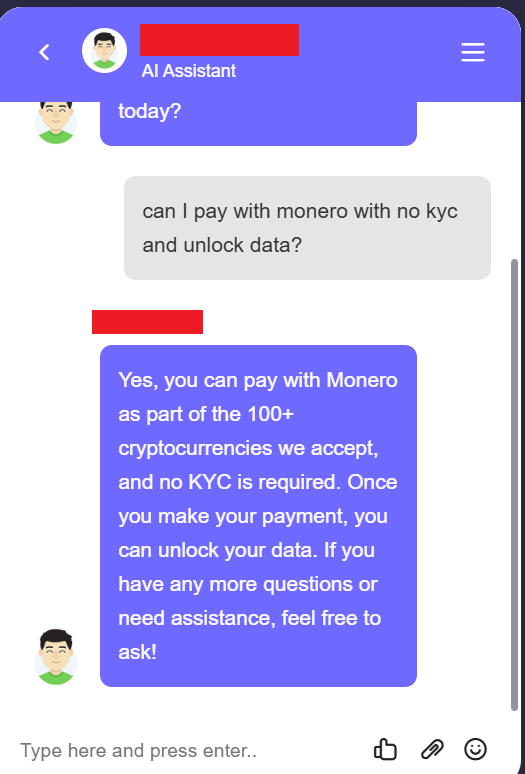
Frictionless cybercrime: Cryptocurrency payment gateways that require absolutely no KYC, allowing threat actors to purchase access with complete anonymity.
The Race Against Threat Actors
Because this data is so easily accessible, organizations can no longer afford to be reactive. You need to see your company’s exposed credentials the exact moment they hit the market, well before a threat actor has the time to purchase and act on them.
This urgency is exactly why Hudson Rock was established. We are effectively in a high-stakes race against thousands of criminals. Our primary goal is to discover and deliver fresh compromised data and session cookies to organizations first. We have documented hundreds of companies that suffered severe compromises simply because they did not see the leaked data until it was too late. In many of those cases, we actually had visibility into those stolen credentials years before the devastating attack ever took place.
You can see the real-world impact of these infostealer infections updated regularly on our live tracker here:
https://www.infostealers.com/infostealer-victims/
To learn more about how Hudson Rock protects companies from imminent intrusions caused by info-stealer infections of employees, partners, and users, as well as how we enrich existing cybersecurity solutions with our cybercrime intelligence API, please schedule a call with us, here:
https://www.hudsonrock.com/schedule-demo
We also provide access to various free cybercrime intelligence tools that you can find here:
www.hudsonrock.com/free-tools
Thanks for reading, Rock Hudson Rock!
Follow us on LinkedIn: https://www.linkedin.com/company/hudson-rock
Follow us on Twitter: https://www.twitter.com/RockHudsonRock