Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100+ Company Ransomware Spree
By Hudson Rock Research Team
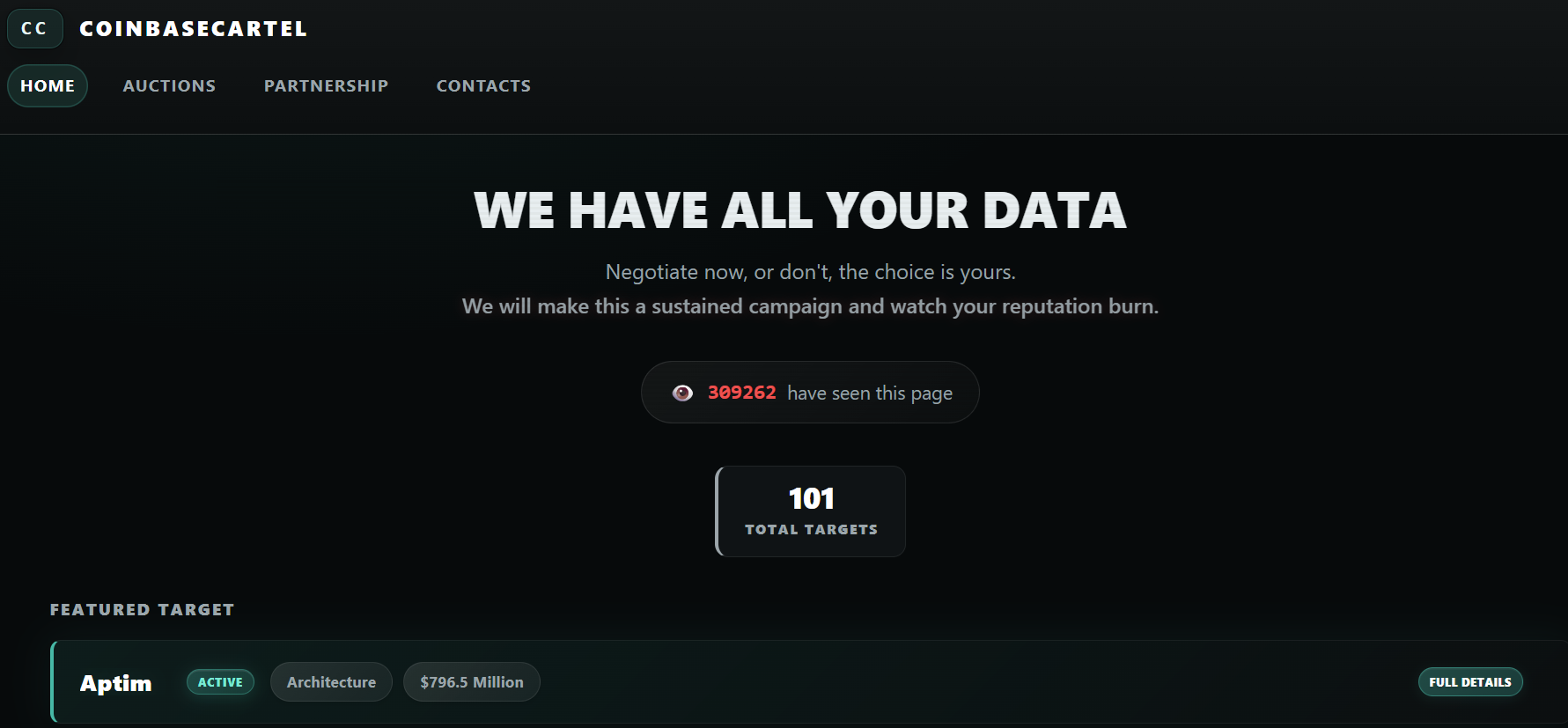
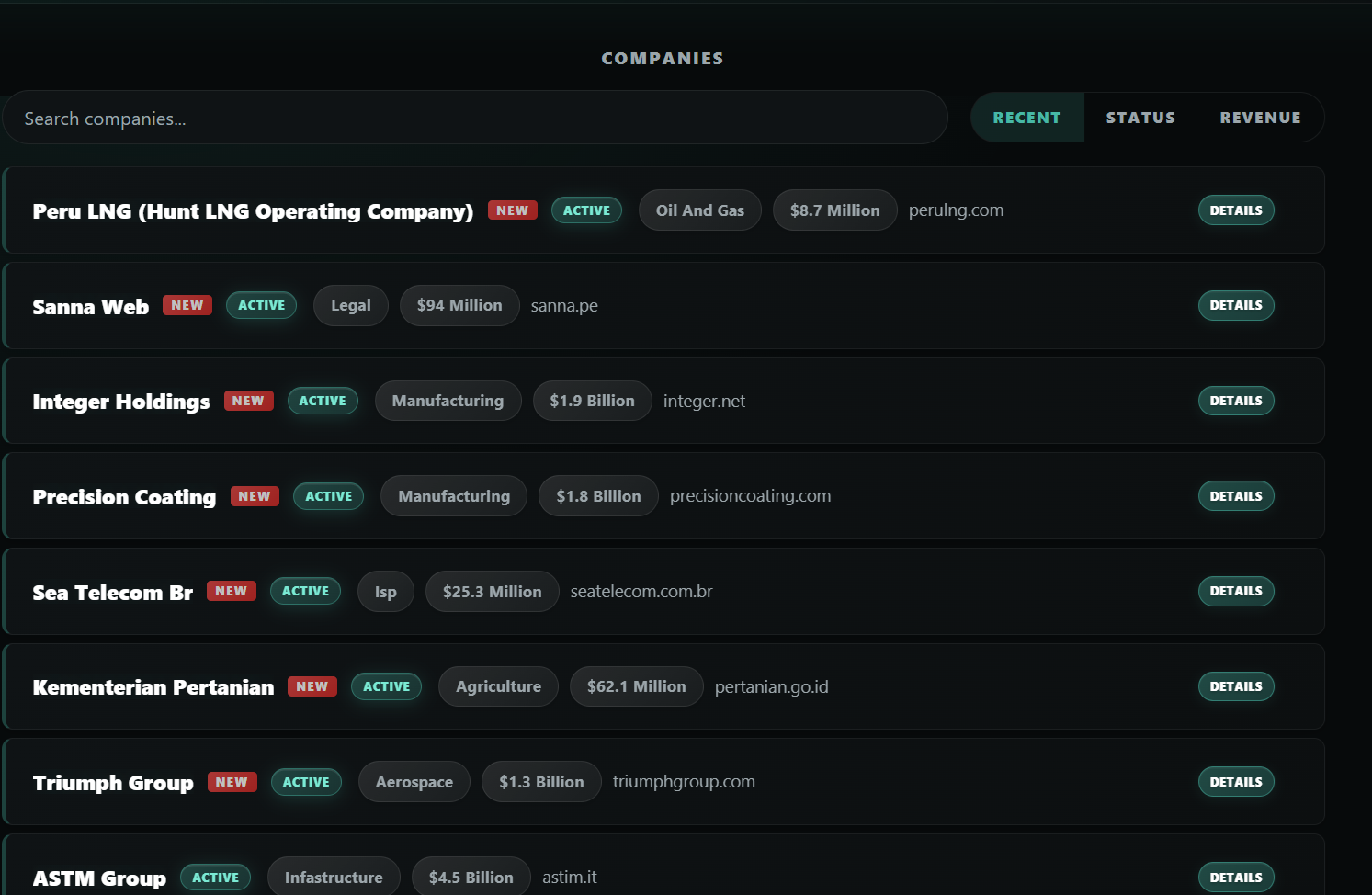
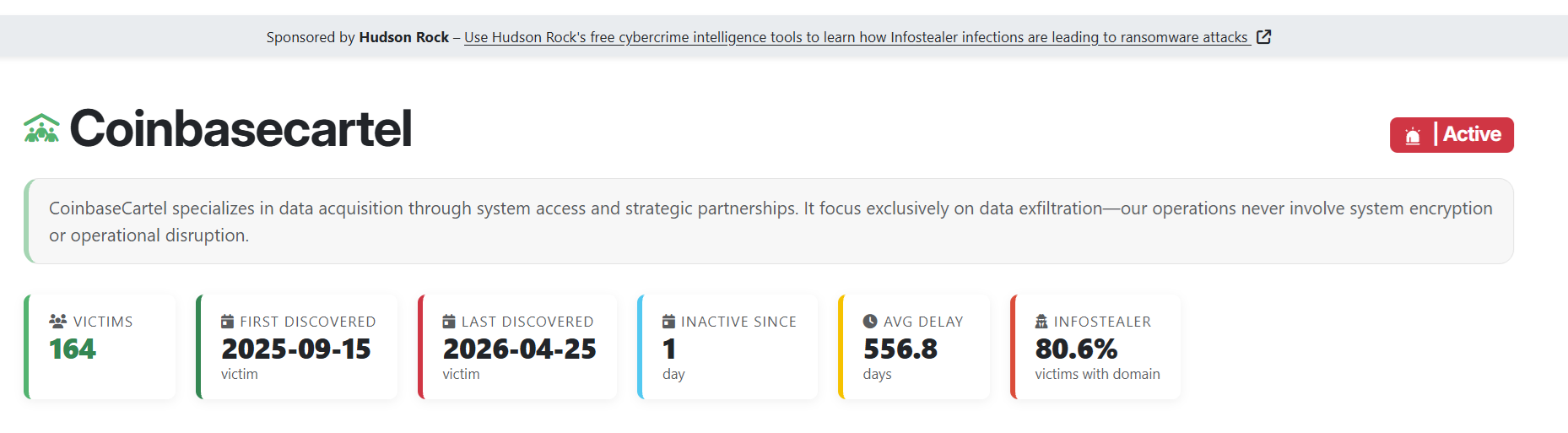
A rapidly expanding ransomware and extortion group known as Coinbase Cartel has officially claimed over 100 targets. The group, which first emerged in September 2025, has made a name for itself through pure data exfiltration and extortion, completely bypassing the use of traditional file encryptors.
While many victim organizations and incident response firms have incorrectly attributed the initial access of these breaches to sophisticated zero-day exploits or complex social engineering, Hudson Rock‘s cybercrime intelligence reveals a different, much simpler reality: Coinbase Cartel exclusively uses old Infostealer credentials to compromise cloud environments, FTP servers, and file transfer services.
The Origin and Operations of Coinbase Cartel
According to historical tracking by Bitdefender, Coinbase Cartel surfaced in late 2025 as part of a growing trend of “extortion-only” operations. By abandoning encryptors, the group ensures that their attacks are quieter and faster, leaving systems fully operational while they silently siphon massive amounts of sensitive corporate data.
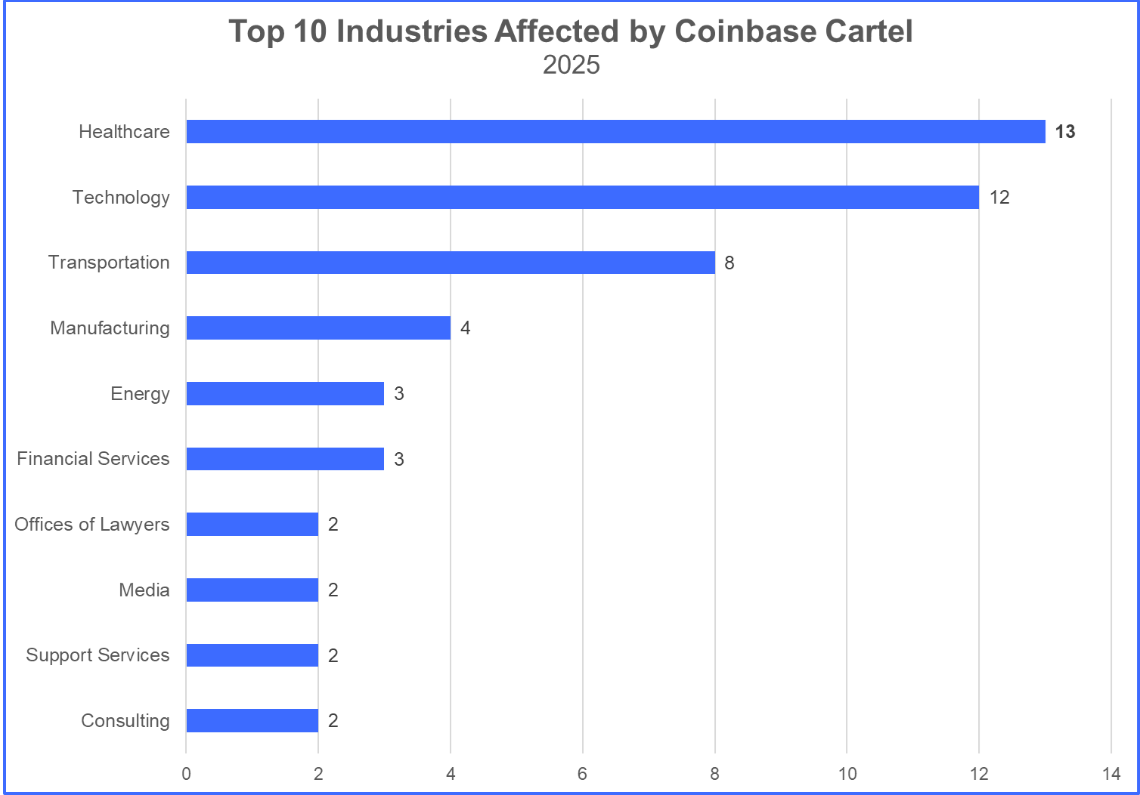
In their first few months alone, they skyrocketed to the top 10 most active ransomware groups globally. They specifically target high-revenue organizations in the healthcare, technology, and transportation sectors, banking on the fact that these industries cannot afford the regulatory and reputational fallout of a massive data leak.
The Initial Access Reality: It’s All Infostealers
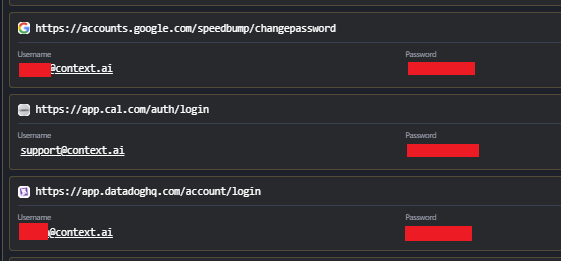
Despite public statements from breached companies pointing fingers at advanced intrusion methods, our analysis at Hudson Rock confirms that Coinbase Cartel’s playbook is heavily reliant on the underground ecosystem of Infostealer malware (like RedLine, Lumma, and Vidar).
By purchasing or aggregating logs of stolen credentials, the cartel identifies valid employee or contractor logins to corporate Cloud, FTP, and file-sharing infrastructure. Shockingly, these credentials are often years old and were indexed in Hudson Rock‘s database years before the actual ransomware attacks took place.
The Hudson Rock Intelligence Correlation
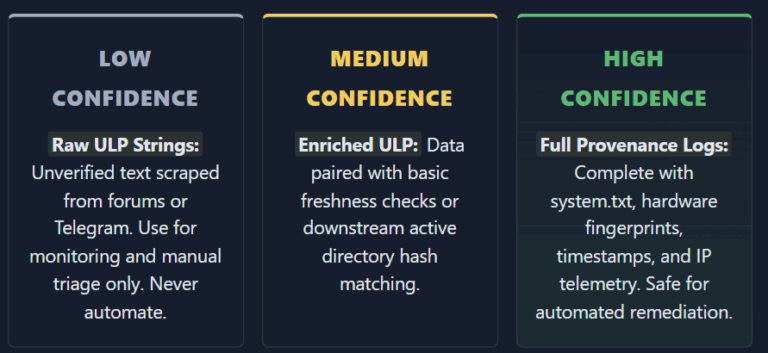
Through our partnership with Ransomware.live, we cross-referenced Coinbase Cartel’s victim list against our Cavalier database of Infostealer infections.
| Company Name | Industry | Revenue |
|---|---|---|
| JBS Brazil | Food & Beverage | $89.9 Billion |
| Engie | Oil And Gas | $84.4 Billion |
| PACCAR | Manufacturing / Tech | $31.1 Billion |
| Correios | Transportation | $28 Billion |
| Cognizant | Tech | $21.1 Billion |
View Some of the Additional Victims
| Ceva Logistics | Logistics | $20.2 Billion |
| Amcor | Packaging | $17.4 Billion |
| Desjardin Bank / Group | Bank | $13.7 Billion |
| SK-Telecom | Technology | $13.5 Billion |
| Balfour Beatty | Construction | $10.6 Billion |
| Renesas Electronics | Manufacturing | $10 Billion |
| Avery Dennison | Manufacturing | $8.7 Billion |
| Insight | Tech | $8.7 Billion |
| Staples | Retail | $8 Billion |
| Ralph Lauren | Retail | $7.8 Billion |
| Commscope | Technology | $5.3 Billion |
| ASTM Group | Infastructure | $4.5 Billion |
| ILLUMINA | Manufacturing | $4.3 Billion |
| SIG.biz | Manufacturing | $3.9 Billion |
| ChampionX | Industrial Machinery | $3.6 Billion |
| Carters | Retail | $2.9 Billion |
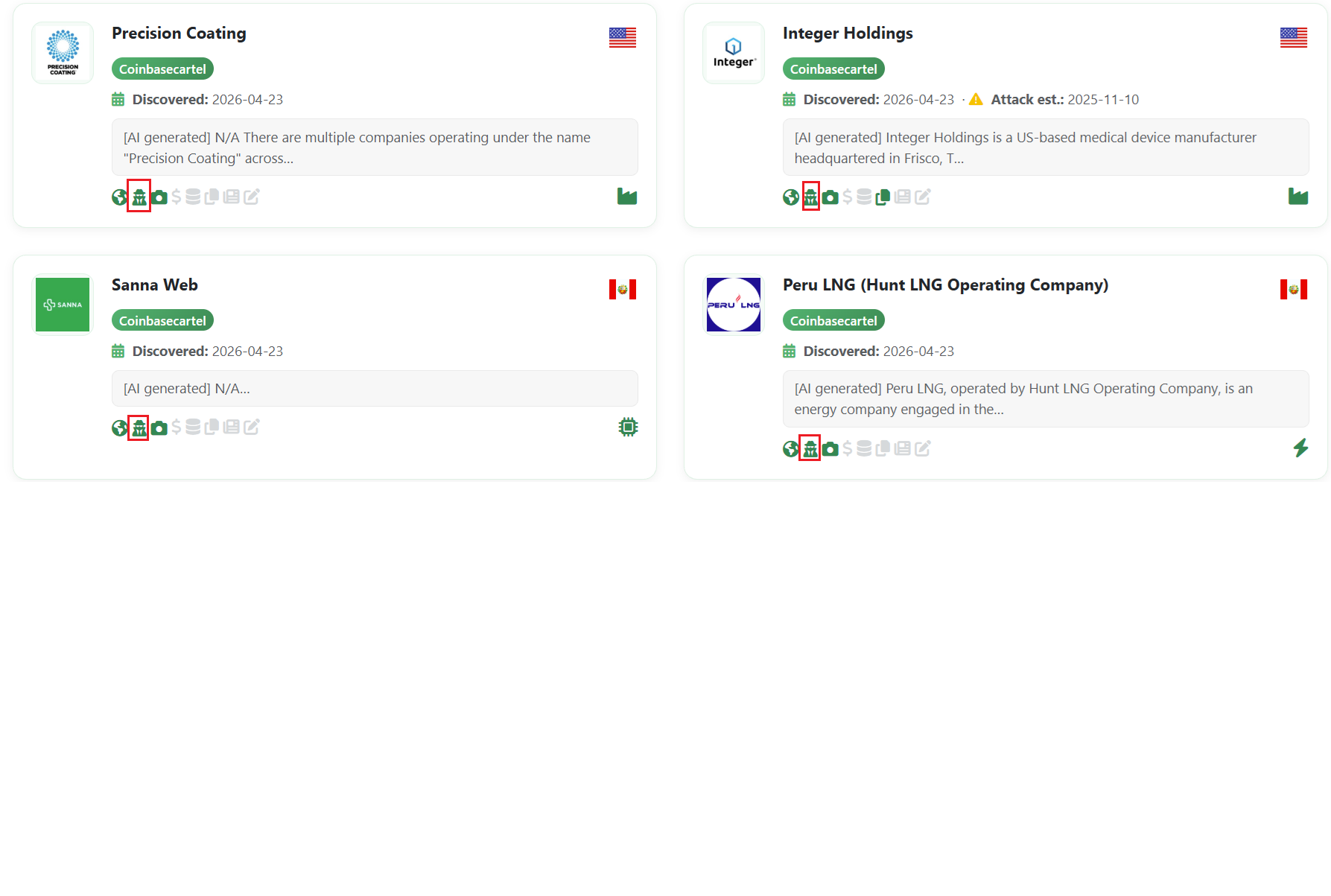
| Integer Holdings | Manufacturing | $1.9 Billion |
| Precision Coating | Manufacturing | $1.8 Billion |
| Lacoste | Fashion | $1.7 Billion |
| Canada Goose | Fashion | $1.3 Billion |
| Triumph Group | Aerospace | $1.3 Billion |
| Triumph International | Manufacturing | $1.3 Billion |
| Dolby Laboratories | Manufacturing | $1.3 Billion |
| Helzberg | Gold And Diamonds | $1.1 Billion |
| Aptim | Architecture | $796.5 Million |
| Propertyfinder / PropSpace CRM | Real Estate Tech | $614.8 million |
| SGK INC | Advertising & Marketing | $548 Million |
| Pellenc | Industrial Machinery | $543.1 Million |
| Westwing Home & Living | Manufacturing | $470.8 Million |
| GDEV | Gaming | $464.5 Million |
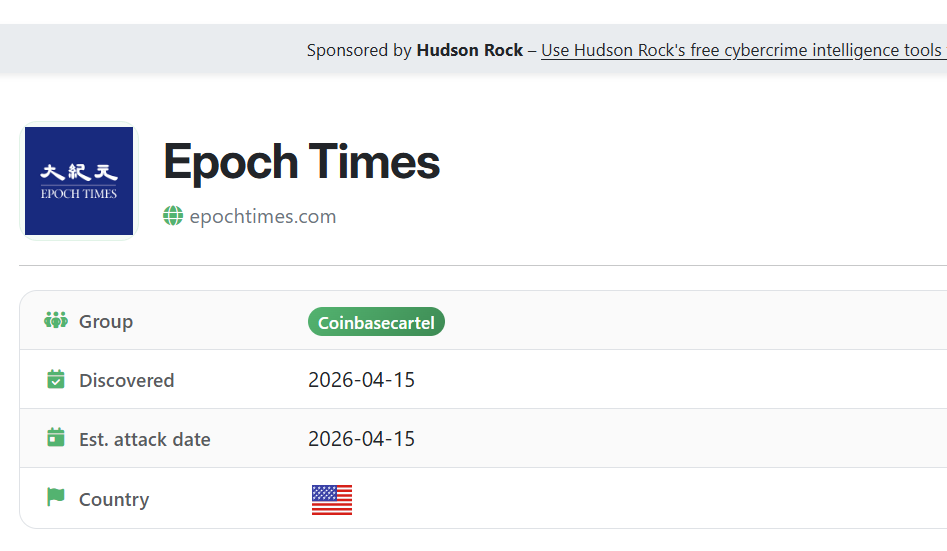
| The Epoch Times | News | $352 Million |
| Wayne Brothers Construction | Construction | $318 Million |
| Posiflex | Tech | $302.4 Million |
| UOM University | Technology | $297.3 Million |
| Studiosus Reisen Munchen | Hospitality | $287.8 Million |
| Cinvestav | Education | $224.4 Million |
| Symeta | Business Services | $203.4 Million |
| KEB | Manufacturing | $174.2 Million |
| Pacific Airlines | Aviation | $173 Million |
Case Studies: From Infostealer Log to Ransomware Leak
To further demonstrate this exact pipeline from an employee accidentally downloading an Infostealer to Coinbase Cartel extorting the company, we have highlighted 5 notable examples from the cartel’s recent 100+ target milestone. While we have identified the infostealer credentials attributed to the breaches of many more organizations on their victim list, these 5 case studies clearly illustrate the consistent attack vector. In every instance, the likely credential used for the attack was sitting in our Cavalier database long before the breach occurred.
1. Aptim
Aptim, a major architecture and engineering firm, was breached and actively leaked by the cartel. Our intelligence shows clear historical Infostealer compromises linked to the organization’s infrastructure.
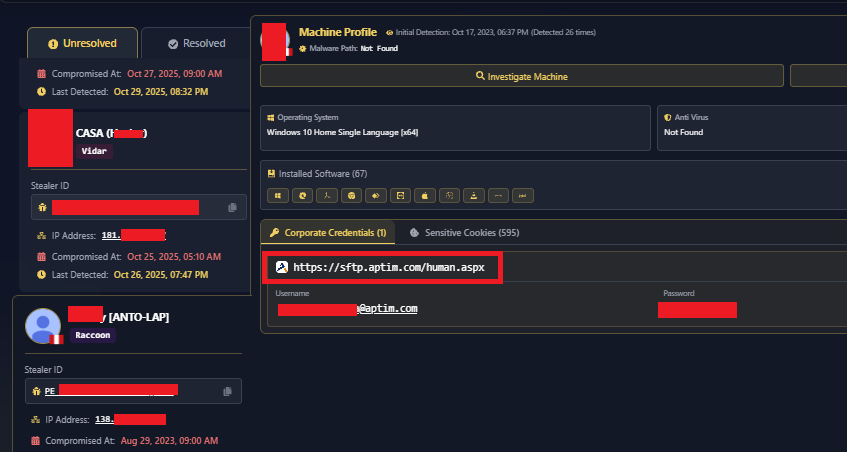
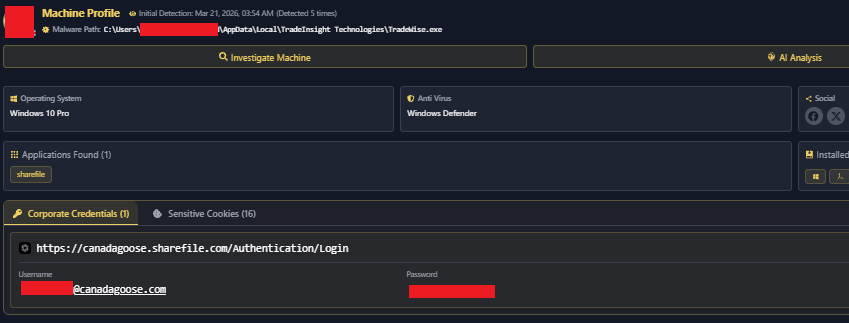
2. Canada Goose
Global fashion brand Canada Goose suffered a significant data leak. The cartel posted proof of the stolen data, which was easily accessible via cloud credentials that were previously compromised. They utilized a very fresh infection data for this attack.
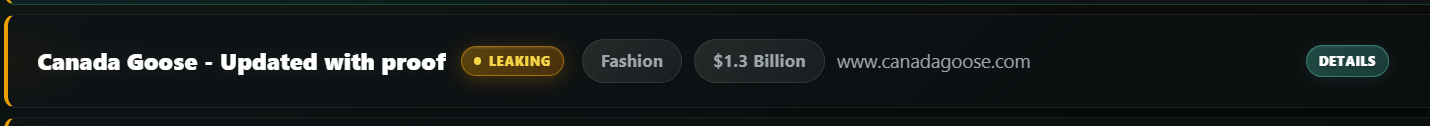

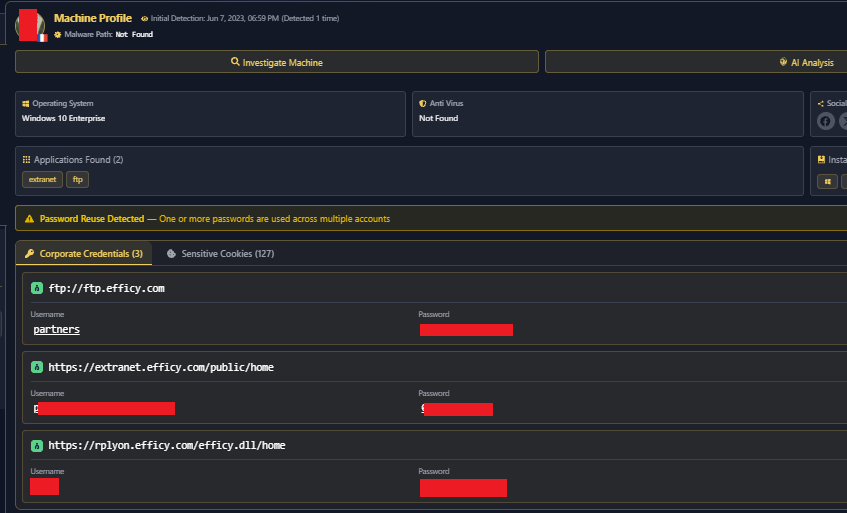
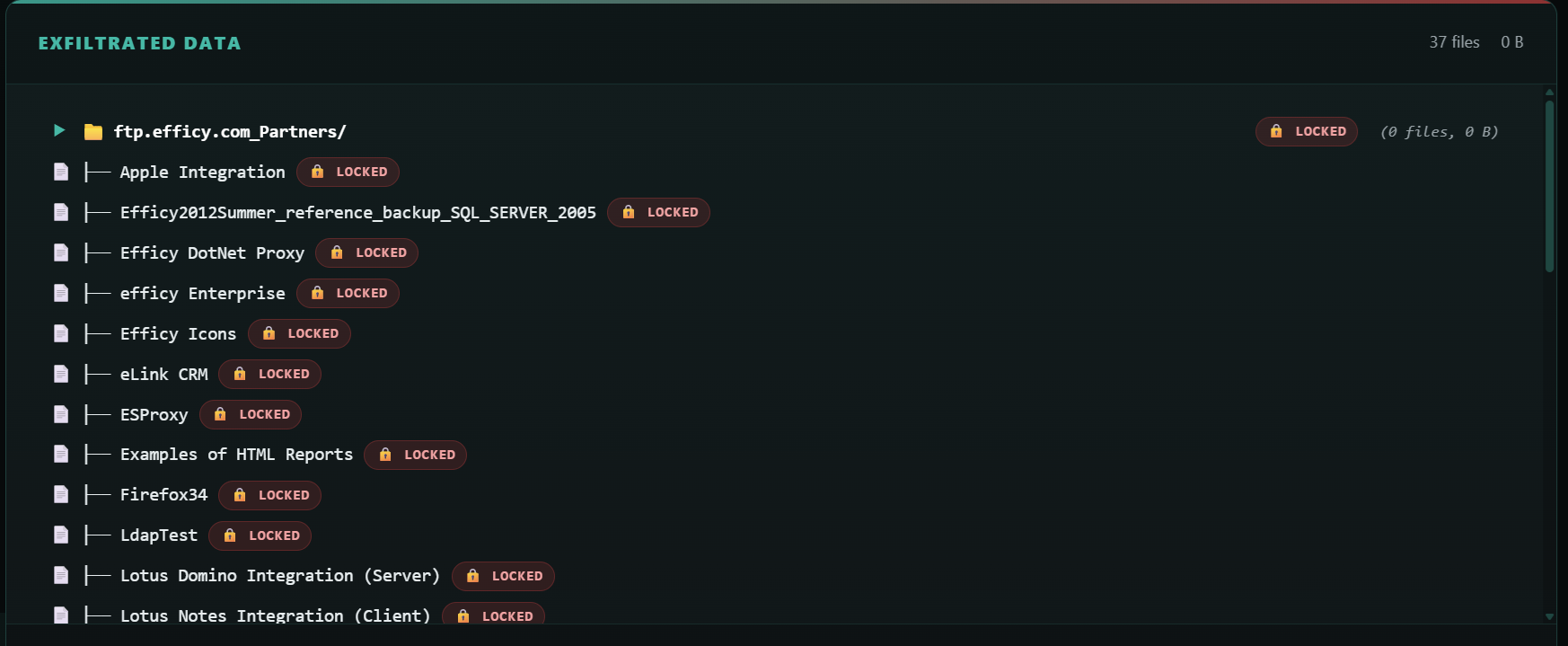
3. Efficy
Efficy, a prominent business services provider, saw 43GB of their data leaked. Once again, the initial access traces back to Infostealer logs.
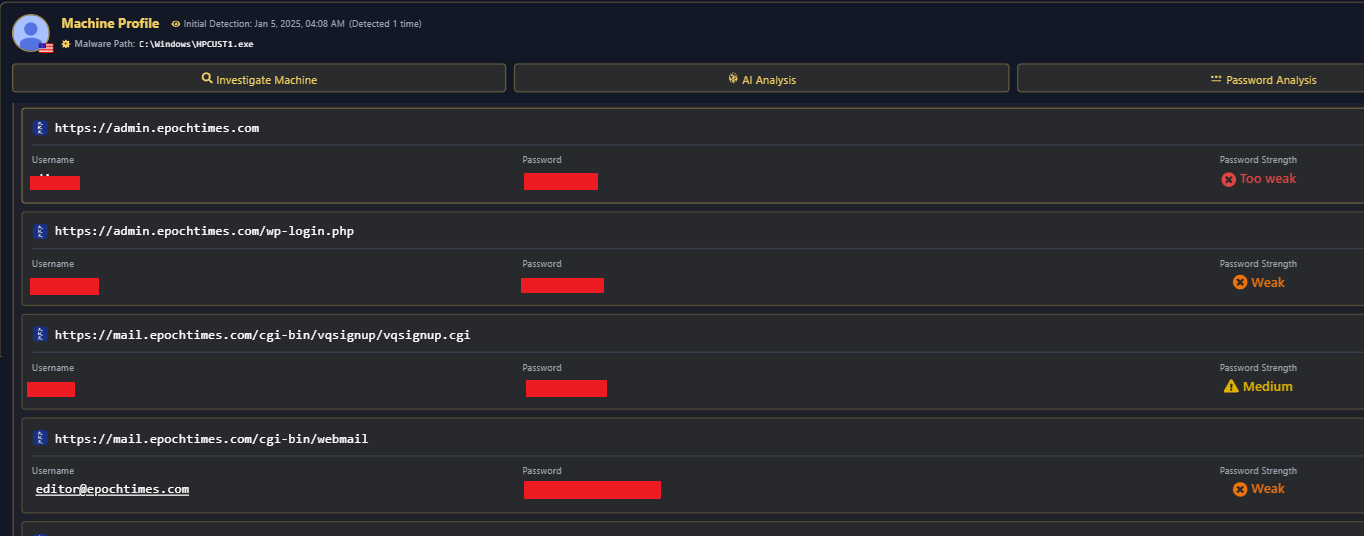
4. The Epoch Times
Media organizations are not immune. The Epoch Times was successfully targeted, with their exposed credentials heavily documented in our historical records.
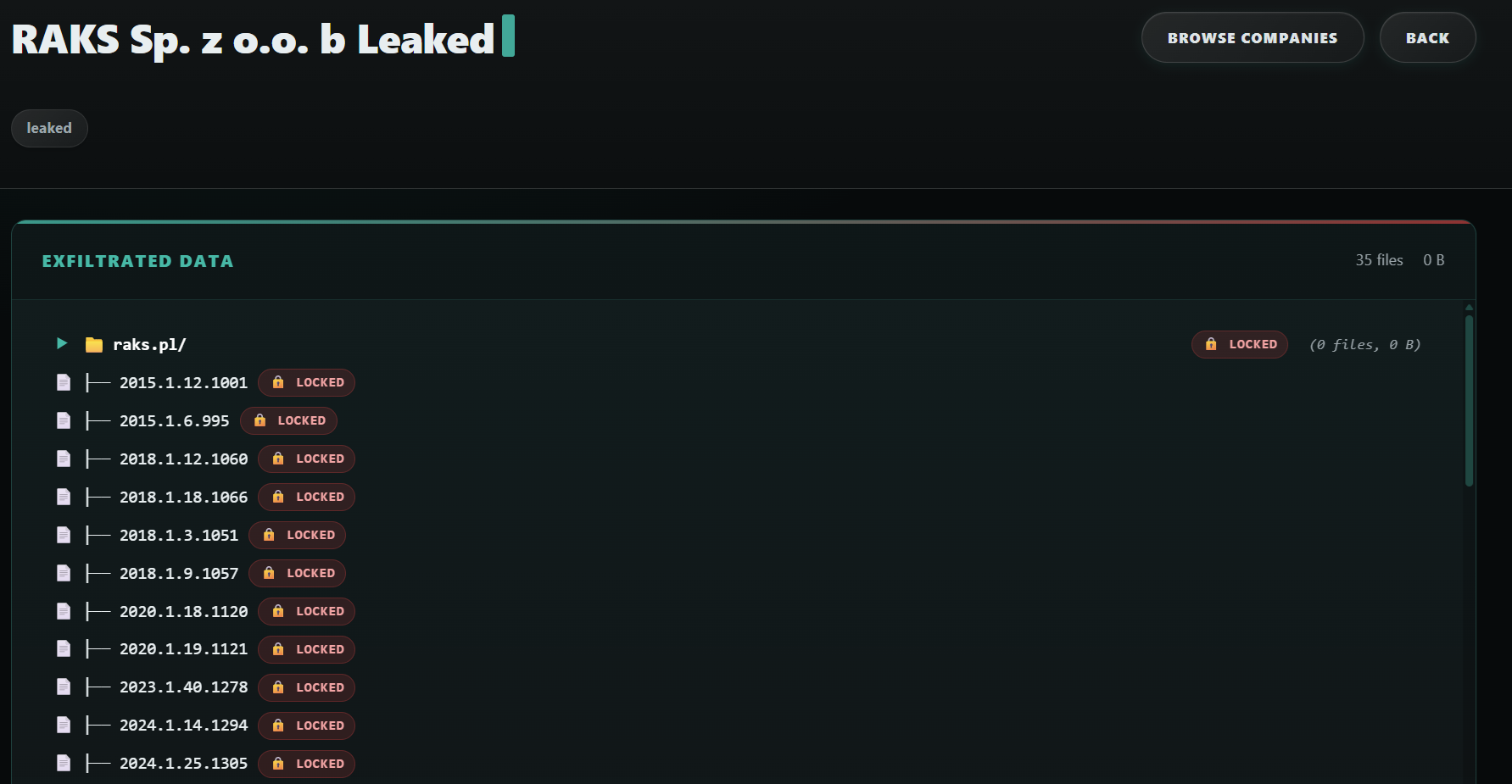
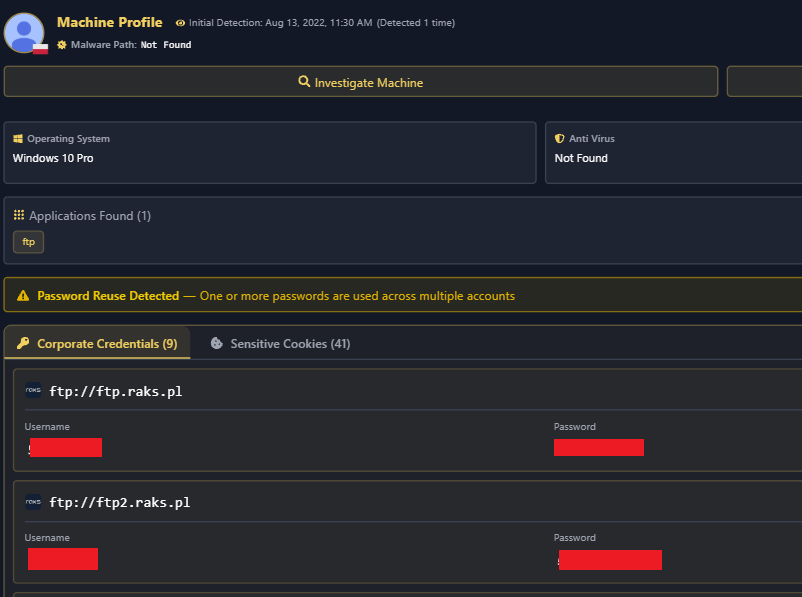
5. RAKS
RAKS, a technology firm, was also breached using this identical methodology, transitioning from a seemingly harmless forgotten malware infection to a full-blown corporate data leak.
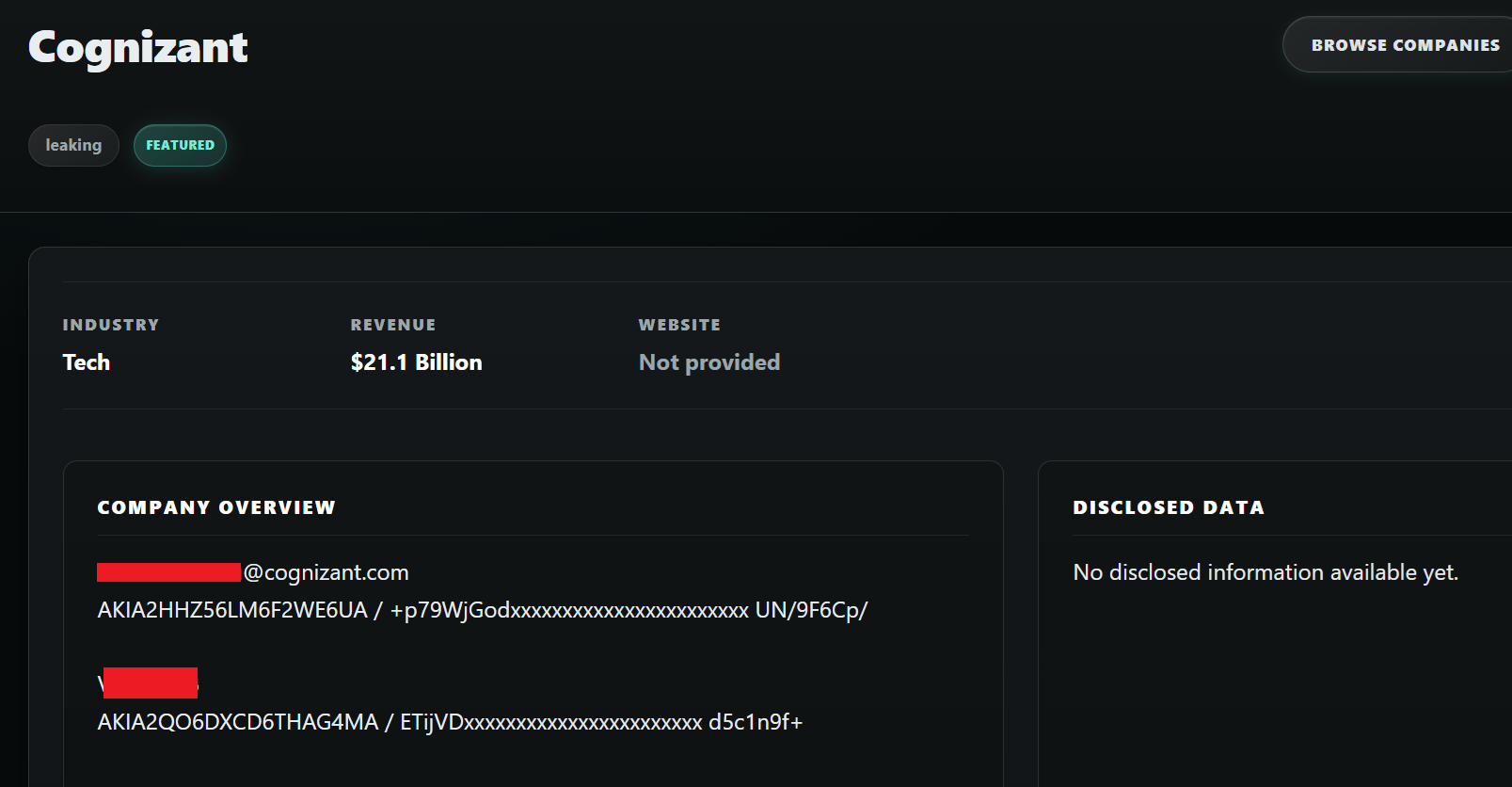
The Attribution Nightmare: The Cognizant Example
One of the primary reasons organizations fail to identify the root cause of these breaches is the sheer volume of compromised employees. In many cases, victims of Coinbase Cartel had tens of employees infected via infostealers over several years.
When an enterprise has hundreds or thousands of exposed corporate credentials floating around the dark web, attributing the breach to one specific compromised credential becomes incredibly difficult without granular threat intelligence. This is perfectly illustrated in the case of Cognizant, where a multitude of employee infections created a massive attack surface for the cartel to choose from.

Conclusion
The rise of Coinbase Cartel is a stark reminder that the lifespan of an Infostealer log is practically indefinite until those credentials are changed. Threat actors are no longer relying purely on burning expensive zero-days to breach organizations. Instead, they are taking the path of least resistance: exploiting old, forgotten credentials to directly access Cloud and file-sharing infrastructure, bypassing traditional endpoint defenses entirely. We’ve seen similar credentials resulting in tens of millions of dollars paid to groups who used infostealer credentials to hack Change Healthcare.
To learn more about how Hudson Rock protects companies from imminent intrusions caused by info-stealer infections of employees, partners, and users, as well as how we enrich existing cybersecurity solutions with our cybercrime intelligence API, please schedule a call with us, here:
https://www.hudsonrock.com/schedule-demo
We also provide access to various free cybercrime intelligence tools that you can find here:
www.hudsonrock.com/free-tools
Thanks for reading, Rock Hudson Rock!
Follow us on LinkedIn: https://www.linkedin.com/company/hudson-rock
Follow us on Twitter: https://www.twitter.com/RockHudsonRock