How One Infostealer Infection Solved a Global Supply Chain Mystery and Unmasked DPRK Spies in U.S. Crypto.
Executive Summary: Key Findings
- The Infiltrator-in-Chief (Gate.us): The operative successfully infiltrated the American crypto exchange Gate.us. In a staggering display of irony, this sanctioned North Korean actor sat in on Google Meets with Western compliance vendors (Sumsub) to actively define the very AML/KYC logic designed to catch him, mapping their blind spots using real FBI fugitives.
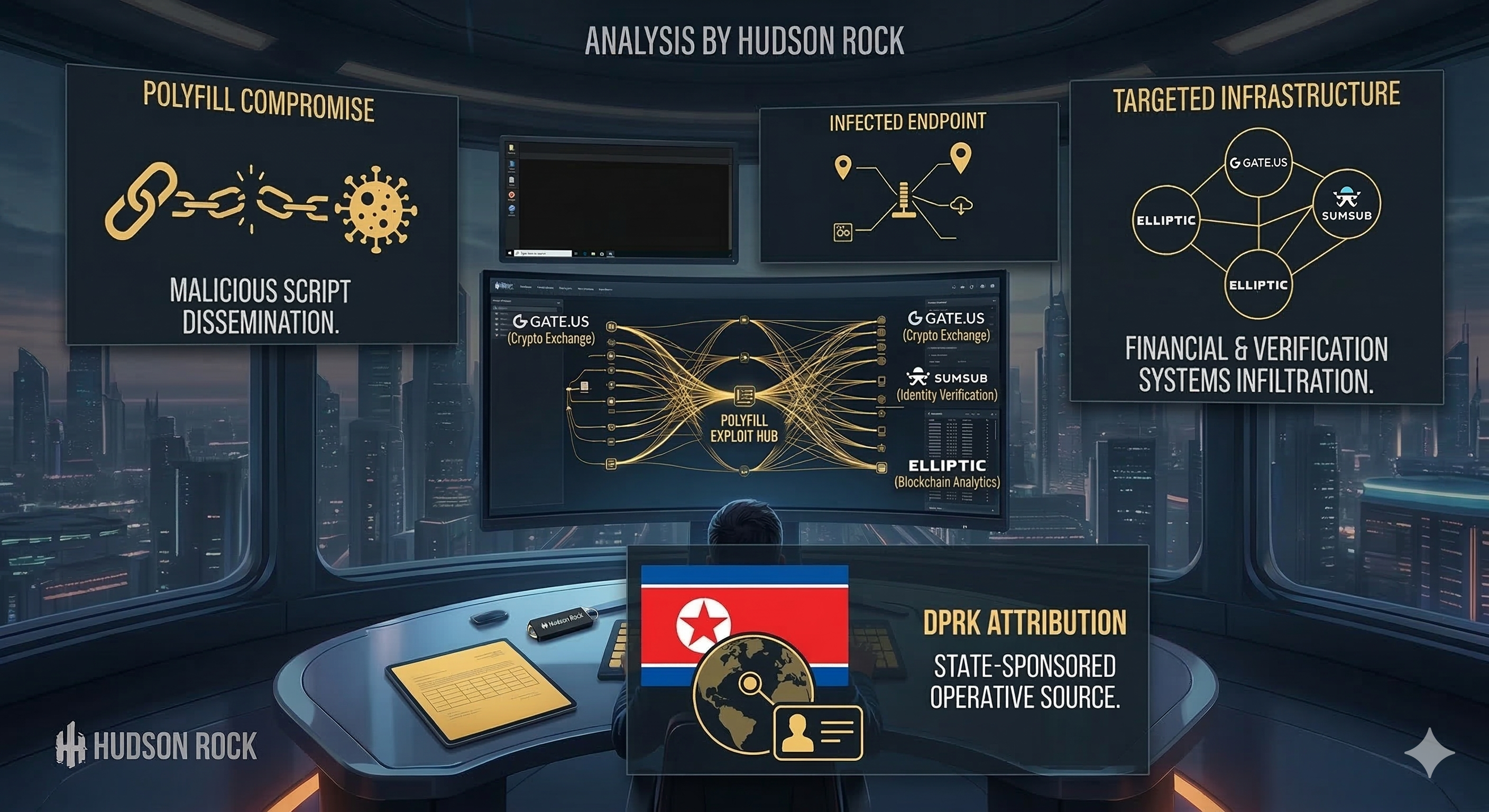
- The Polyfill.io Mastermind: Definitive forensic evidence links the catastrophic Polyfill.io supply chain attack (which compromised 100,000+ websites) directly to a North Korean state-sponsored actor embedded within a Chinese syndicate.
- Japanese Scientific Espionage: Transcending simple IT wage theft, the actor exfiltrated sensitive, air-gapped network blueprints from the National Institute for Materials Science (NIMS), demonstrating a pivot from illicit revenue generation to strategic state espionage targeting critical infrastructure.
- Automated Crypto Laundering: The actor built an automated Telegram-based cryptocurrency gateway to lease out poisoned CDN nodes and wash USDT without manual intervention.
- A Cybercriminal PIP: Despite orchestrating massive cyber warfare campaigns, the North Korean operative was put on a “Performance Improvement Plan” and given a salary cut to $3,000/month by his Chinese handlers for needing “too much guidance.”
The global cybersecurity community has spent the past year unraveling the catastrophic Polyfill.io supply chain attack, an event that compromised over 100,000 websites globally. Until now, researchers could only attribute the attack to a shadowy Chinese entity named “Funnull” and its ties to transnational organized crime. The missing link was definitive attribution.
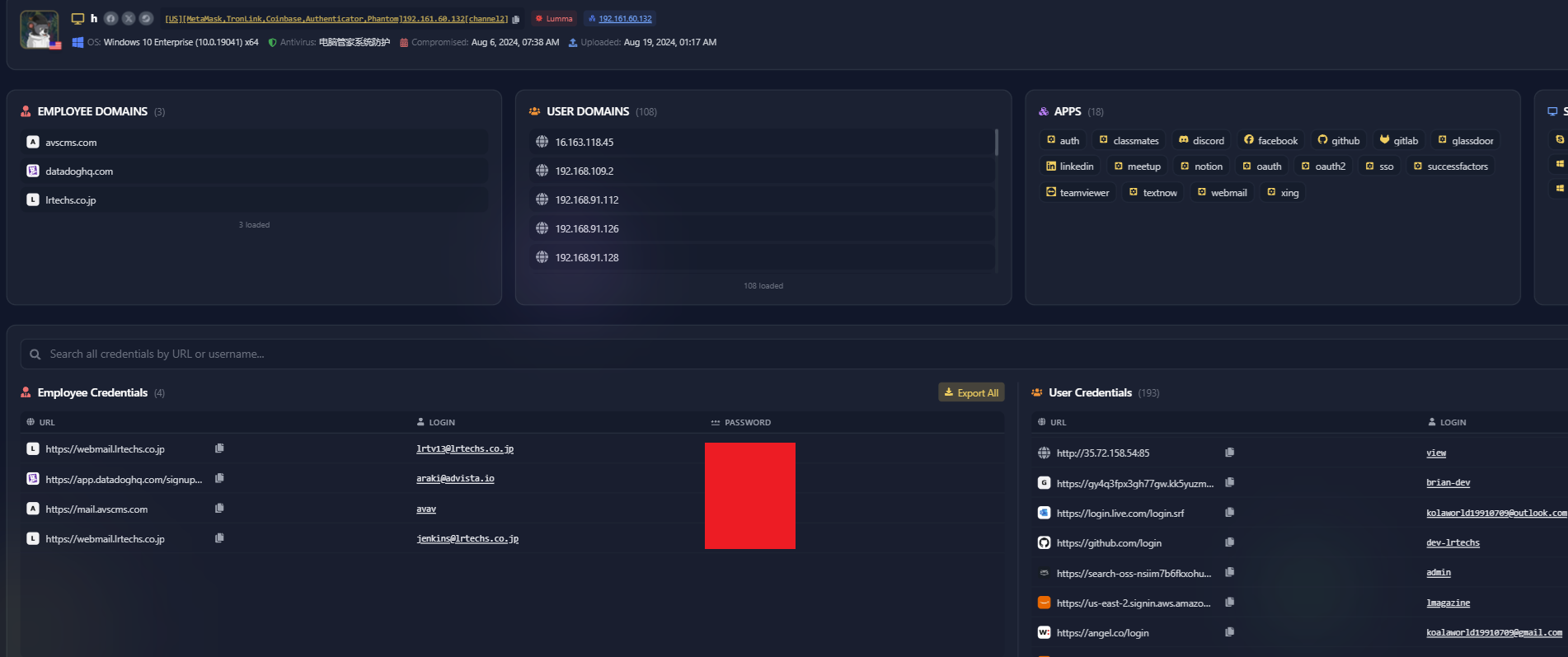
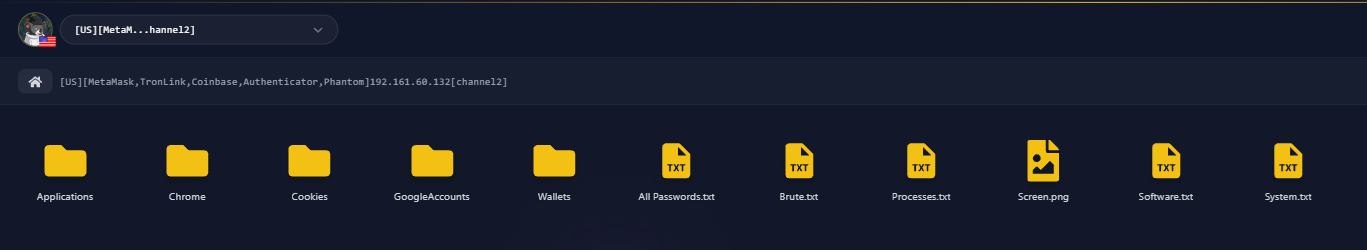
That link has just been found. An exhaustive, forensic-level analysis of browsing history, credential dumps, and operational telemetry recovered from a compromised endpoint by Hudson Rock definitively links the Polyfill.io operator to state-sponsored cyber activities aligned with the Democratic People’s Republic of Korea (DPRK).
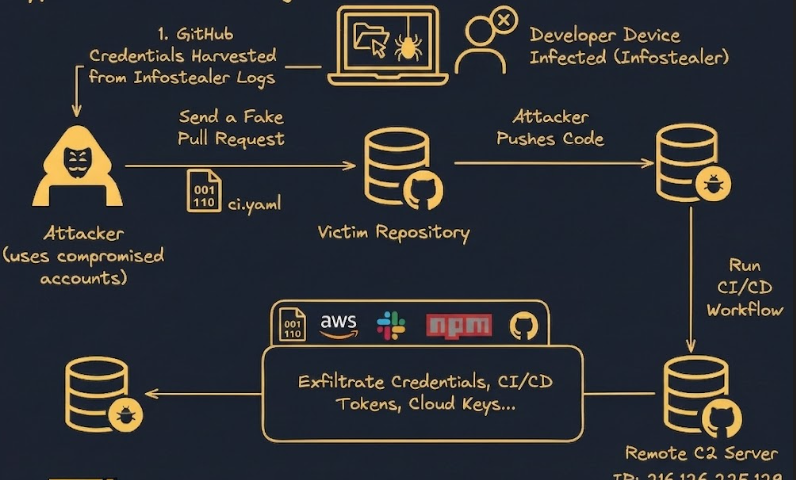
The evidence was not found via advanced network intrusion. It was found because the elite North Korean operative made a fatal operational security (OPSEC) mistake: they downloaded a fake software setup file and infected their own machine with the LummaC2 infostealer.
The browsing history extracted directly from the machine perfectly captures the exact user journey that led to the compromise. The operative, likely searching for cracked software or IT tools to facilitate their operations, navigated to a MediaFire file-sharing link. They proceeded to download a password-protected ZIP archive deceptively named to appear as a legitimate software installer. This archive contained the trojanized payload:
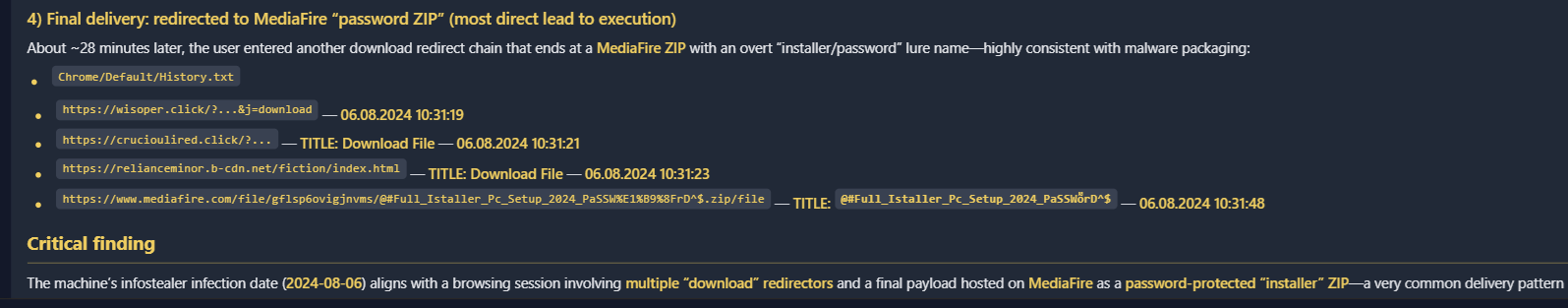
What followed was a massive exfiltration of operational data. This report meticulously deconstructs the actor’s identity matrices, corporate targets, cryptographic financial operations, internal communications, and backend infrastructure. It provides a terrifying look at the convergence of illicit revenue generation (the “DPRK IT Worker” program) and advanced cyber espionage.
1. Persona Architecture and The “Mental Bridge” OPSEC Failure
A defining characteristic of DPRK IT worker operations is the systematic, industrialized creation of synthetic identities. These personas are deployed across global freelance platforms, code repositories, and communication channels to subvert Know Your Customer (KYC) regulations and secure privileged employment within high-value target organizations.
The actor relies heavily on stolen identities, but maintaining the digital footprint of these identities is difficult. The translation history shows a panicked internal communication regarding a burned identity: “This issue that has surfaced with Josue’s SSN/ID can that be fixed without further integration?… What can we do that will not require Twilio as of right now?” The actor is trying to figure out how to maintain corporate access for the stolen “Josue” persona without having to pass Twilio’s SMS multi factor authentication.
Crucially, the massive volume of Google Translate URL telemetry definitively exposes the operator’s native language and true location. The actor uses a “Mental Bridge” workflow: constantly receiving English messages from US employers and Chinese messages from the Funnull syndicate, translating both into Korean to comprehend them, formulating thoughts in Korean, and translating outwards.
English (US Boss) / Chinese (Handler)
Translate to Korean
Native Korean Processing
Translate from Korean
Polite Corporate Replies
In one egregious OPSEC failure, this mental bridge caught the actor slipping up on time zones. After crafting a highly professional English excuse to miss a US corporate meeting, the actor immediately messages their Chinese handler (“ggbond”) referencing Beijing time:
This asynchronous deception allows them to dodge live video standups (which could expose their accent or location) and maintain the facade of a reliable remote worker while hiding their physical reality.
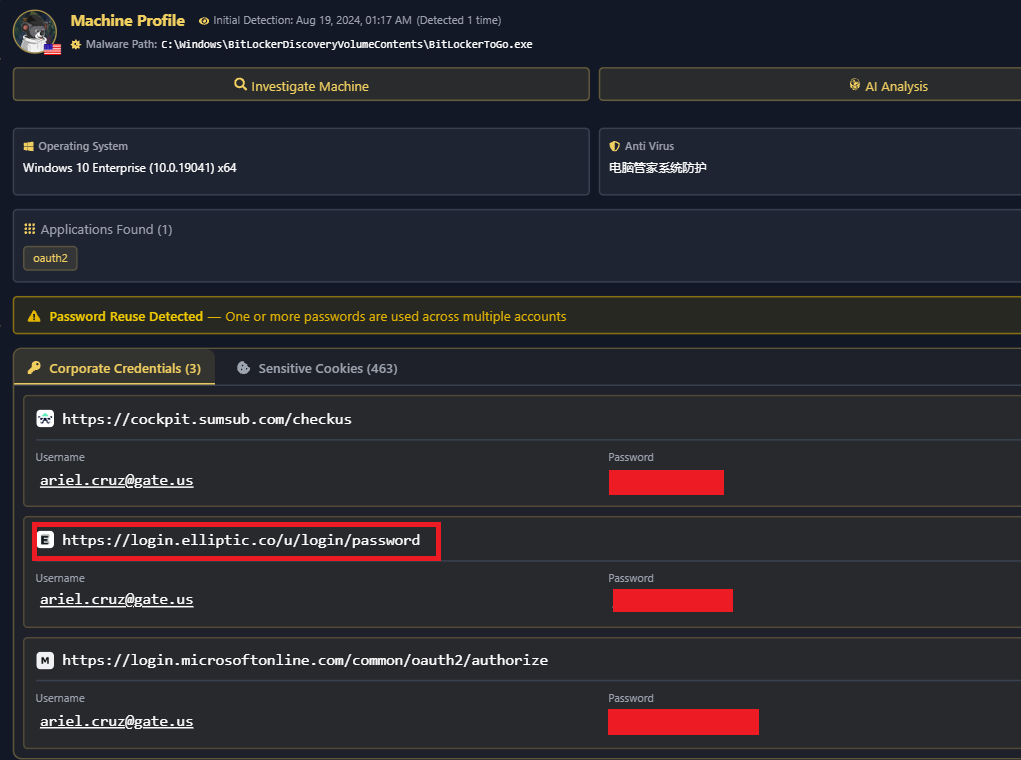
2. Credential Recycling and the Tiered Security Matrix
Despite their sophisticated persona management, the actor exhibits severe credential recycling. This vulnerability allowed analysts to definitively link disparate accounts back to a single operator. The passwords extracted by LummaC2 fall into distinct, functionally segregated groups.
| Security Tier | Password String | Associated Use Cases |
|---|---|---|
| Tier 1: Expendable | rty20210104, Rty@20210104 | Public-facing profiles, HR platforms, daily communication (GitHub, Notion, Lusha, Deel). |
| Tier 2: Infrastructure | QWE@#$qwe234, !QAZXSW@1qazxsw2 | High-value technical infrastructure, VPS hosting, Web3 platforms (Cryptomus, Infura, Gate.us admin). |
| Tier 3: Bulletproof C2 | nk******** | Exclusive, siloed access to stark-industries.solutions endpoints (Russian state-linked bulletproof hosting). |
| Tier 4: Polyfill Admin | keC************** | Exclusive access to [email protected] for managing the weaponized Cloudflare CDN. |
Most critically, the Tier 3 password (nk********) is isolated strictly for Stark Industries, a known bulletproof host used by DPRK threat actors. The prefix “nk” within the Stark password likely serves as an internal mnemonic for “North Korea”, highlighting the distinct operational silo of this specific Command and Control (C2) infrastructure.
3. The Smoking Gun: Linking DPRK to Polyfill.io
Perhaps the most globally significant finding in this analysis is the definitive, operational link between this North Korean endpoint and the infrastructure responsible for the massive Polyfill.io supply chain attack of 2024.
In early 2024, a Chinese Content Delivery Network (CDN) company named “Funnull” acquired the ubiquitous open-source JavaScript library polyfill.io. By June, Funnull weaponized the script, injecting malware that redirected mobile users on over 100,000 websites to malicious sports betting and scam sites.
Hudson Rock has been tracking the Funnull nexus closely. In our previous investigation, Infected by GTA 5 Cheats: How an Infostealer Infection Unmasked a North Korean Agent, we revealed how a careless malware infection exposed a DPRK IT worker acting as a core developer for the Funnull network. The forensic evidence recovered from this new endpoint elevates that initial discovery, tying the same DPRK-Funnull cell directly to the administration of the catastrophic Polyfill.io supply chain attack.
The forensic evidence ties the confiscated endpoint directly to the administration of this campaign. We can establish an ironclad chain of evidence linking the North Korean operator to the Chinese syndicate and the Polyfill control panels, all running on the exact same infected machine (DESKTOP-OG1CFR5).
First, the operator used the persona “Brian” to act as a high-level systems administrator for Funnull’s backend infrastructure. The infostealer successfully extracted the actor’s direct developer credentials to Funnull’s dynamically generated DNS management portal:
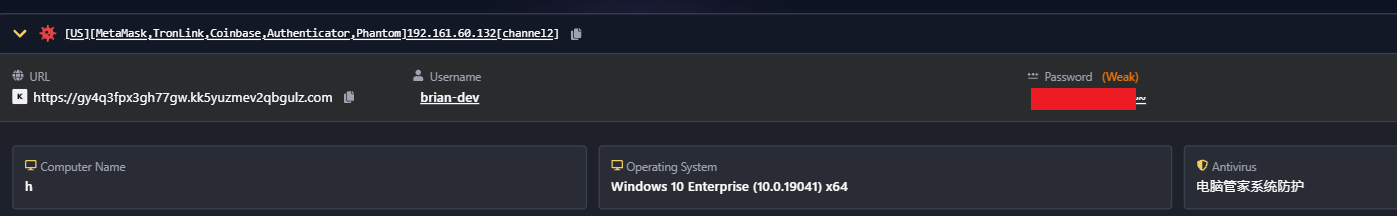
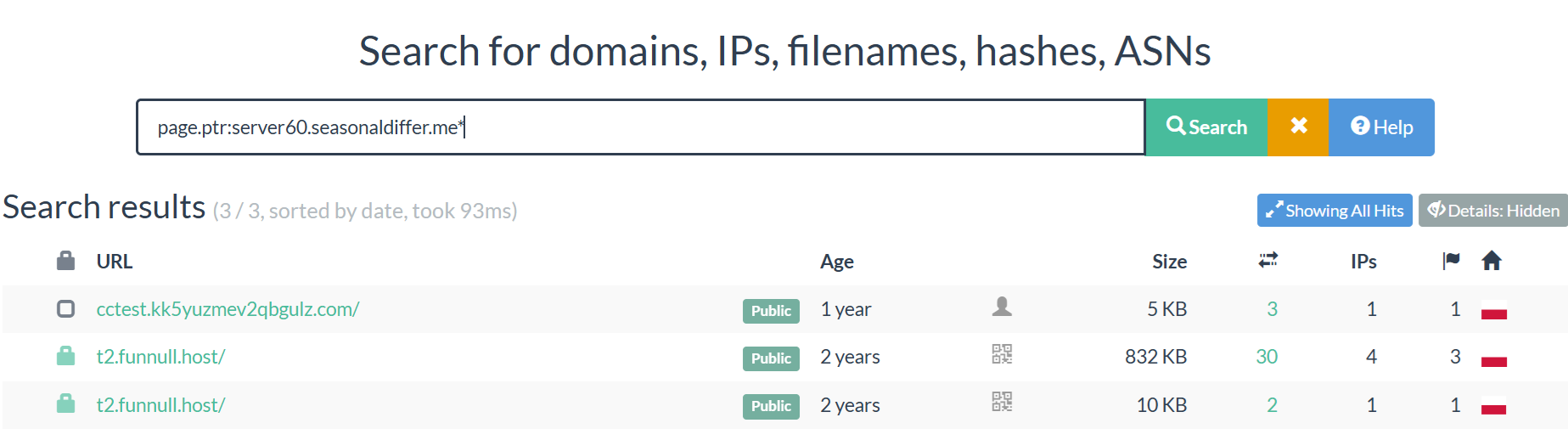
This technical overlap was independently verified by external threat intelligence. Zach Edwards from Infoblox confirmed the structural ties connecting this DPRK actor’s workspace to the Chinese CDN. Specifically, the DGA-style domain used for the FunnullDNS login (kk5yuzmev2qbgulz.com) shares infrastructure with other test domains (like cctest.kk5yuzmev2qbgulz[.]com) that have reverse PTR records pointing directly to t2.funnull[.]host.
Second, the same password dump explicitly contains the master credentials for the Polyfill Cloudflare tenant, proving the actor had direct control over the weaponized domain:
Third, the Google Translate telemetry captures the exact moment the Funnull syndicate discussed modifying the Polyfill domains and DNS routing during the peak of the attack:
Even more damning, the logs expose the exact technical directives the Chinese handlers gave the North Korean coder to build and debug the malware. The handlers instructed “Brian” to hide the malicious code (the “injection function”) inside a specific build process of the “GoEdge” CDN network so that open-source users wouldn’t detect it, and actively complained when the payload failed to execute properly:
This is absolute, irrefutable proof of the supply chain attack mechanics, linking the Chinese Funnull CDN operator directly to the DPRK coding apparatus.
4. The Infiltrator-in-Chief: Spying on Gate.us Compliance
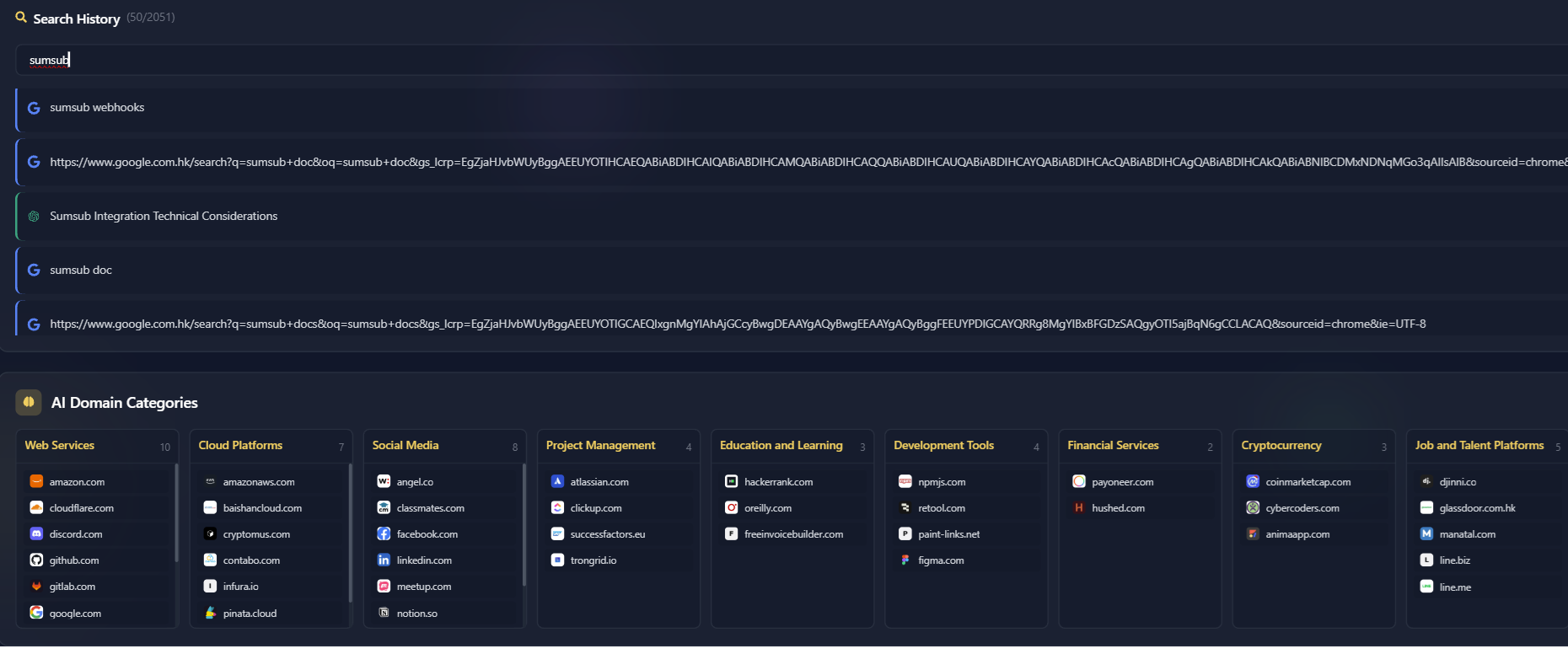
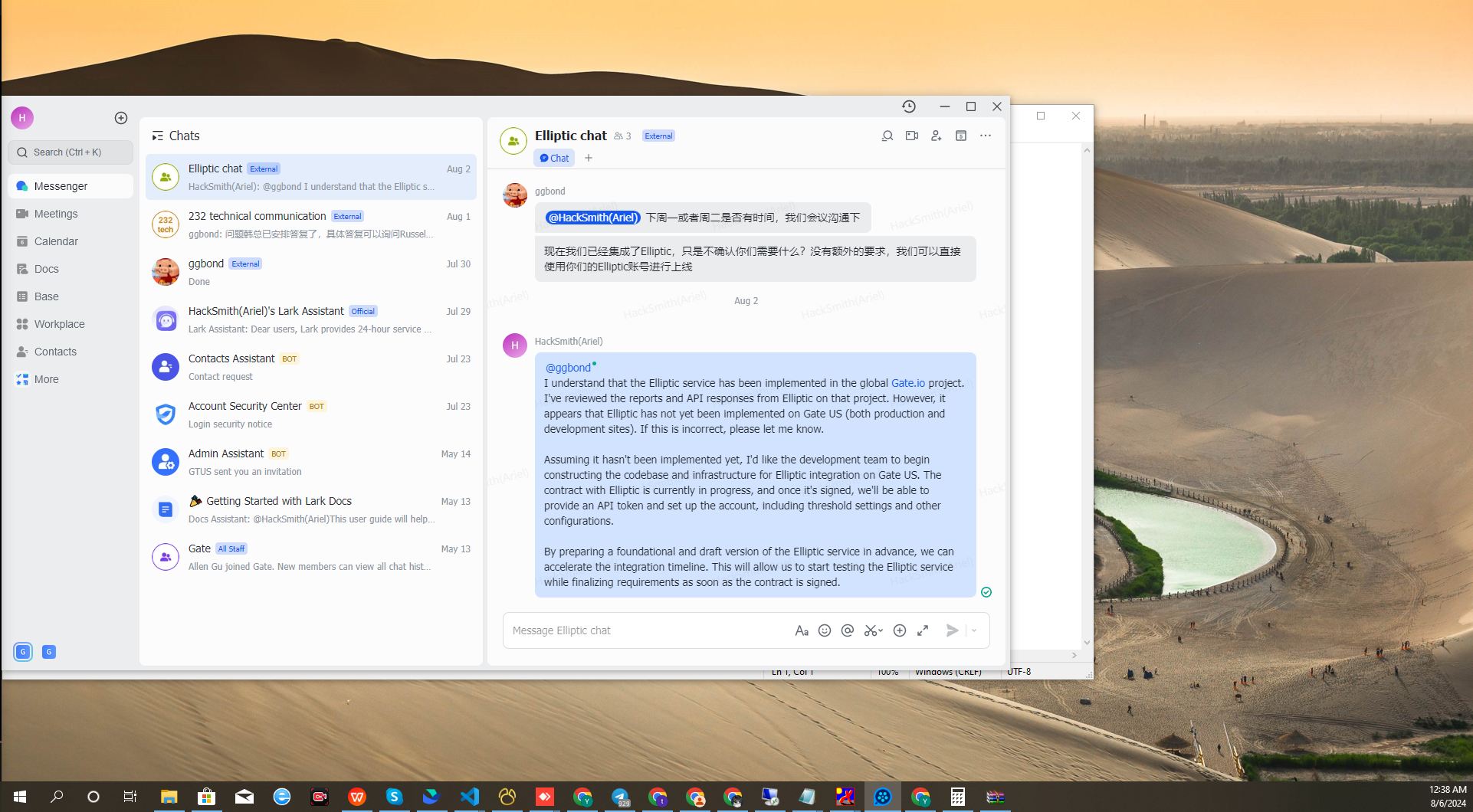
The credential dumps, screenshots, and internal translation logs reveal what is undoubtedly one of the most bizarre and ironic scenarios ever recorded in threat intelligence. The DPRK actor successfully infiltrated Gate.us, an American cryptocurrency exchange, securing a high level administrative role under the synthetic persona Ariel Cruz ([email protected]).
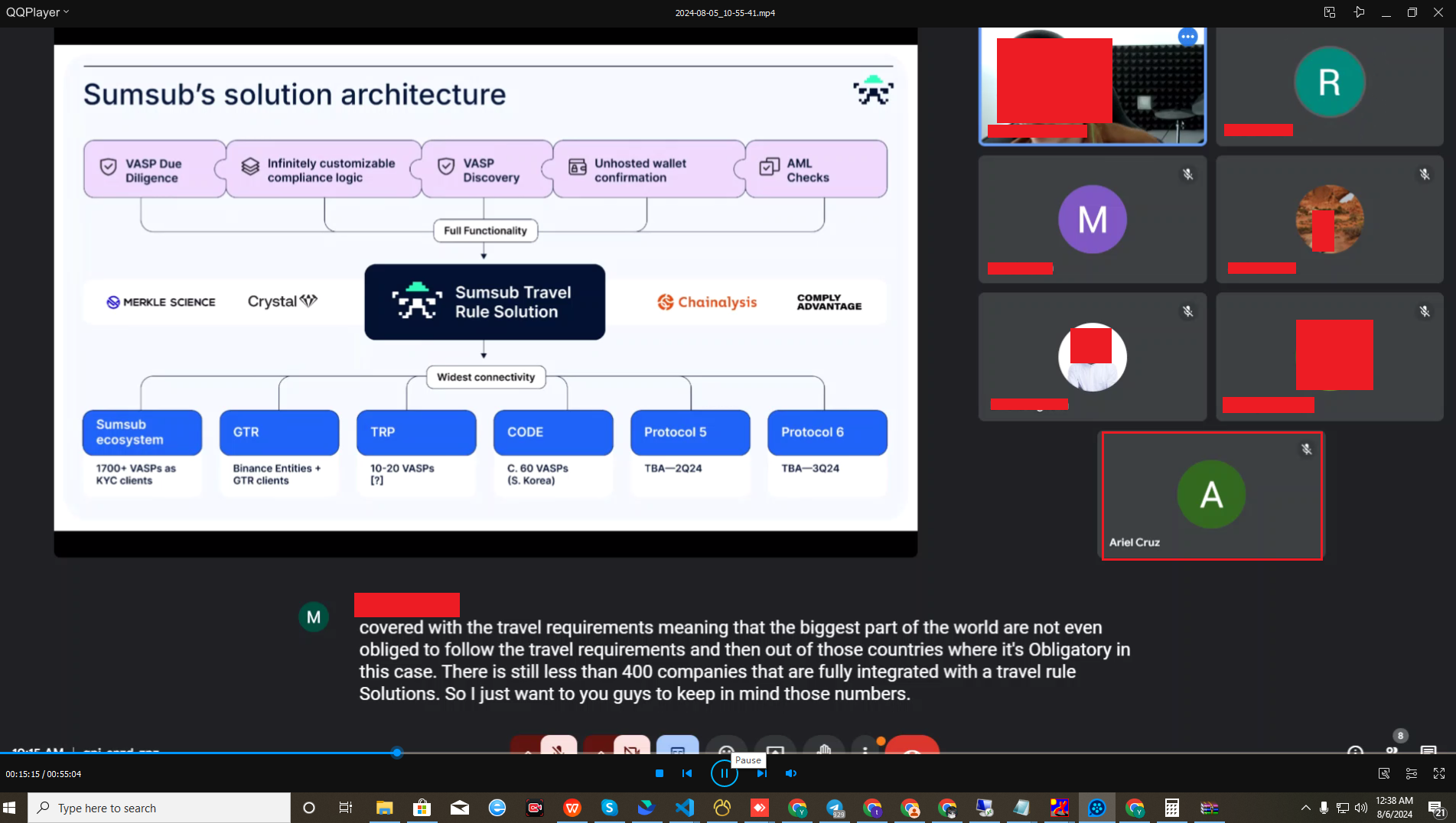
The actor is literally positioned inside a US crypto exchange, directing the implementation of the very AML and KYC tools (Sumsub and Elliptic) designed to keep sanctioned actors like themselves out of the global financial system.
To gather intelligence on their own employer’s security posture, the actor scoured internal repositories and search engines to understand the exact technical specifications of the exchange’s KYC implementation.
The internal translation logs reveal a stunning dynamic. The DPRK operative was not just writing code; they were intercepting, translating, and studying high-level executive communications between Gate.us leadership and their compliance vendors. The telemetry (showing English being translated to Korean via sl=en&tl=ko) proves the North Korean spy was silently monitoring his American employers (R., C., and Dr. H.) as they negotiated biometric data liability with Sumsub:
By covertly feeding these internal executive emails into Google Translate to read in his native Korean, the operative gained a masterclass in US legal vulnerabilities, corporate liability fears, and exactly how Western exchanges evaluate the cost of identity verification (down to the 24 cent per user margin).
This reconnaissance wasn’t limited to intercepted emails. The operative successfully exfiltrated highly sensitive internal architecture diagrams detailing exactly how the crypto exchange routes user data through Sumsub’s verification engine.
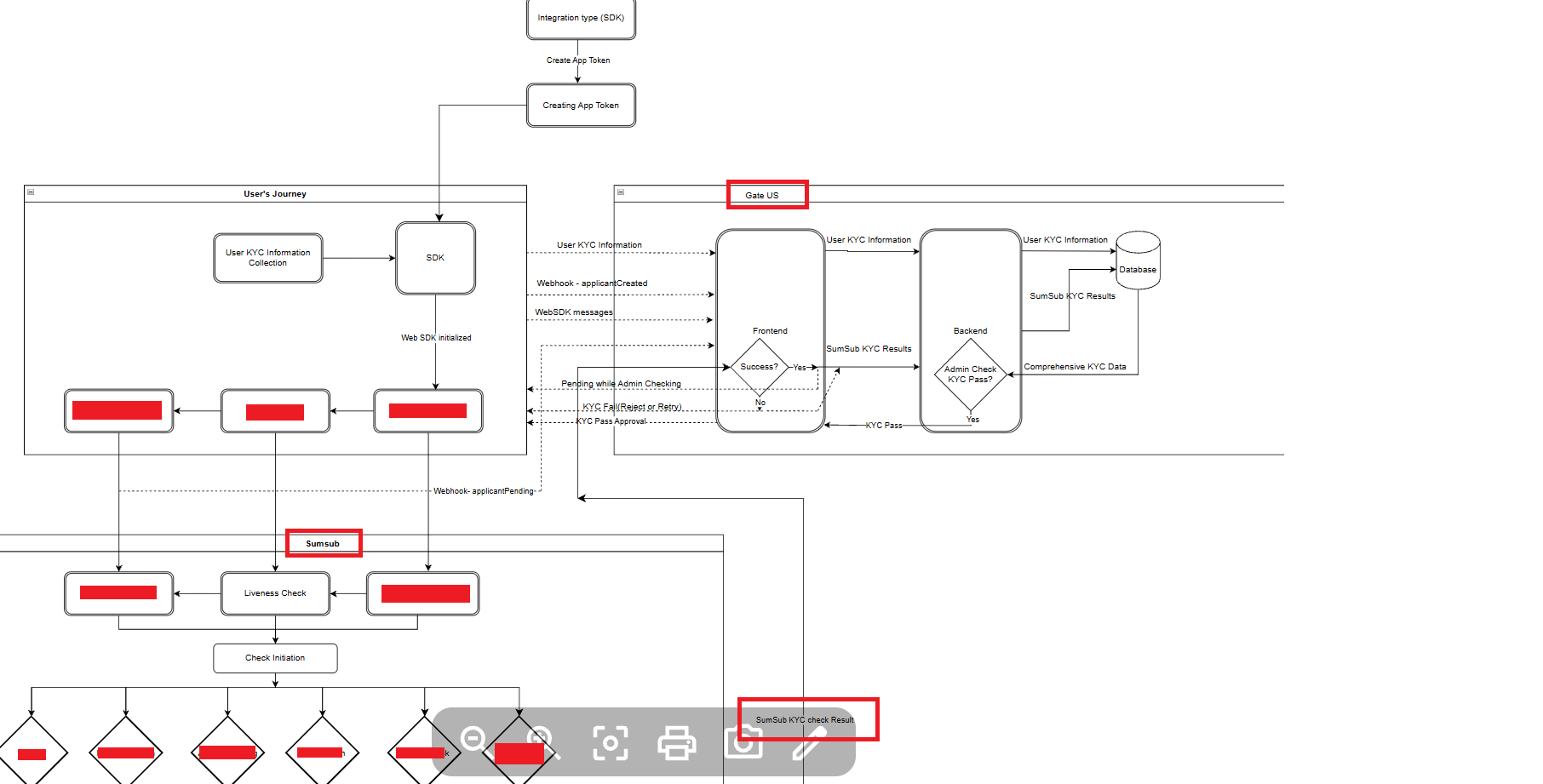
But the infiltration goes deeper than eavesdropping. To ensure Gate.us’s compliance systems worked (or to map their exact blind spots), the US team tasked the actor with testing the staging environment. The actor didn’t just use dummy data; they actively searched for and translated the profiles of real FBI fugitives and heavily sanctioned individuals to feed into the test environment. Translation logs show them researching Bernard Madoff (the architect of the largest Ponzi scheme in history), George Wright (a fugitive hijacker), and Milovan Bjelica (a sanctioned Bosnian politician).
By pushing real world criminal and sanctioned profiles through the staging environment (including testing “Saddam Hussein” and getting an approval), the North Korean operative was successfully reverse-engineering the precise detection thresholds, fuzzy matching logic, and blind spots of the West’s premier anti-money laundering algorithms.
5. The “So What?” of NIMS: A Pivot to Strategic Espionage
While the DPRK IT worker program is widely understood as an illicit revenue generation scheme, the recovered telemetry proves this actor used their access to conduct strategic, state-sponsored data exfiltration.
The telemetry explicitly identifies the compromised Japanese consultancy as LR Techs (lrtechs.co.jp). Embedded deep within their internal development team under the alias “Wenyi Han” ([email protected] and GitHub handle wenyidev921), the DPRK operative secured a devastating supply-chain foothold. By infiltrating LR Techs’ Backlog workspaces, Slack channels, and AWS environments, the actor didn’t just breach a single target, they gained lateral access to a massive portfolio of downstream Japanese enterprise clients.
But the espionage goes much further than financial data. The Autofills.txt telemetry captures the exact moment the North Korean operative exfiltrated highly sensitive, air-gapped network blueprints from the National Institute for Materials Science (NIMS).
NIMS is not just another corporate target; it is the absolute backbone of Japanese aerospace, defense, and nanotechnology research. In Google Workspace (Docs/Drive), when a user clicks “Make a copy” to clone a document to their own private drive, the browser captures the title in the DOM element ID copy-filename-input. The autofill logs definitively prove the actor wasn’t just reading these documents, they were actively cloning the closed-network architecture blueprints of NIMS for exfiltration.
Cloning “closed-network” infrastructure blueprints indicates a terrifying pivot. This operative was not just stealing wages, they were conducting strategic state espionage targeting critical national infrastructure.
6. Automated Crypto Laundering and the “Cybercriminal PIP”
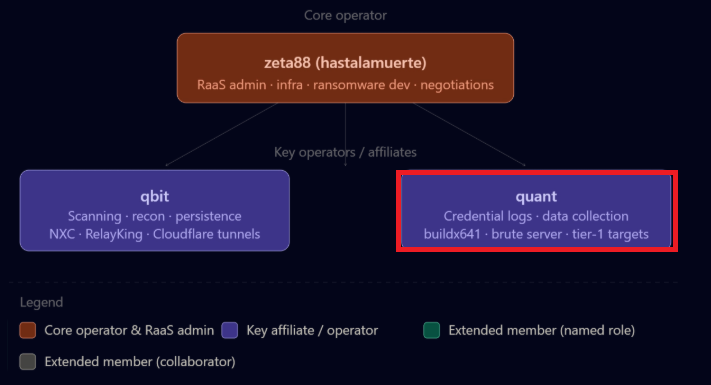
As a revenue generating arm of the DPRK, the threat actor’s endpoint exhibits significant interaction with cryptocurrency infrastructure. The actor was building an automated Telegram-based payment gateway designed to route and wash USDT using rented TRON energy to avoid transaction fees entirely, directly supporting the Lazarus and Suncity money laundering pipeline.
Translated internal chats expose exactly what this bot was for: automating the sale of malicious CDN infrastructure. The actor writes a status report to his Chinese handlers detailing the exact mechanics of the API integration to wash the funds:
The team is extremely paranoid about operational security regarding this bot’s source code, stating: “Severe Warning: The current repository code belongs to core commercial secrets, and must never be leaked!”
However, despite the massive scale of the global supply chain attack they were facilitating, the telemetry reveals a hilarious, almost mundane reality. The Chinese Triad bosses were apparently unsatisfied with the North Korean hacker’s CDN coding efficiency. In a chat reminiscent of a toxic corporate HR meeting, his handlers formally docked his pay and put him on a literal “Cybercriminal Performance Improvement Plan” (PIP):
Even state-sponsored elite hackers, responsible for compromising 100,000+ global websites, aren’t immune to the soul-crushing bureaucracy of middle management. Slapped with a PIP, the APT had his salary slashed by his organized crime bosses for needing “too much guidance.” Cyber warfare, it turns out, still has micromanagers.
7. Malicious Infrastructure and Contagious Interview
To sustain operations while evading detection, the actor relies heavily on Stark Industries Solutions. The credentials recovered include logins for vision.stark-industries.solutions and friday.stark-industries.solutions. Stark Industries is a notorious bulletproof hosting provider sanctioned by the EU for enabling Russian hybrid threats.
Prior to these sanctions, threat intelligence analysts identified Stark Industries as the primary infrastructure provider for a North Korean-aligned threat group tracked as “Contagious Interview” (G1052). The presence of these credentials confirms that this operator is a constituent member of the G1052 cluster.
Defensive Playbook: Spotting the Infiltrator
The forensic analysis of this endpoint dictates that organizations must move beyond simple identity verification and implement stringent behavioral analytics for remote contractors. Key markers of infiltration include:
- Latency/IP Audits: Flag “domestic” workers with consistent 200ms+ latency. This is a primary signature of residential proxy networks and commercial VPNs masking overseas traffic.
- Clock-Skew Analysis: Monitor for burst activity, commits, and logins that consistently align with Pyongyang or Beijing working hours (UTC+8/UTC+9) rather than the employee’s stated local time zone.
- The “Google Translate” Pattern: Monitor for high volumes of translation queries paired with “Make a copy” events (
copy-filename-input) in Google Workspace, especially when those events involve sensitive internal infrastructure, network diagrams, or PII databases.
Conclusion
The forensic analysis of this endpoint yields profound implications. It conclusively proves that DPRK IT workers are not merely low level coders generating freelance wages. They are highly capable advanced persistent threats (APTs) who embed themselves into the core infrastructure of foreign targets to conduct strategic espionage.
The attribution of the Polyfill.io supply chain attack to a coordinated operation involving North Korean cyber elements and transnational organized crime is a watershed moment in threat intelligence. Furthermore, their ability to gain employment writing the very KYC compliance code designed to stop them demonstrates a catastrophic failure of current corporate vetting paradigms.
Infostealers have become a powerful, evidence-based tool for researchers, law enforcement, and security agencies conducting deep-dive investigations. Hudson Rock specializes in customizing and analyzing this raw telemetry to fit the exact needs of these critical investigations, uncovering the hidden mechanics of global cybercrime.
To learn more about how Hudson Rock protects companies from imminent intrusions caused by info-stealer infections of employees, partners, and users, as well as how we enrich existing cybersecurity solutions with our cybercrime intelligence API, please schedule a call with us, here: https://www.hudsonrock.com/schedule-demo
We also provide access to various free cybercrime intelligence tools that you can find here: www.hudsonrock.com/free-tools
Thanks for reading, Rock Hudson Rock!
Follow us on LinkedIn: https://www.linkedin.com/company/hudson-rock
Follow us on Twitter: https://twitter.com/RockHudsonRock