How Infostealers Industrialize the Brute-Forcing of Corporate SSO Gateways
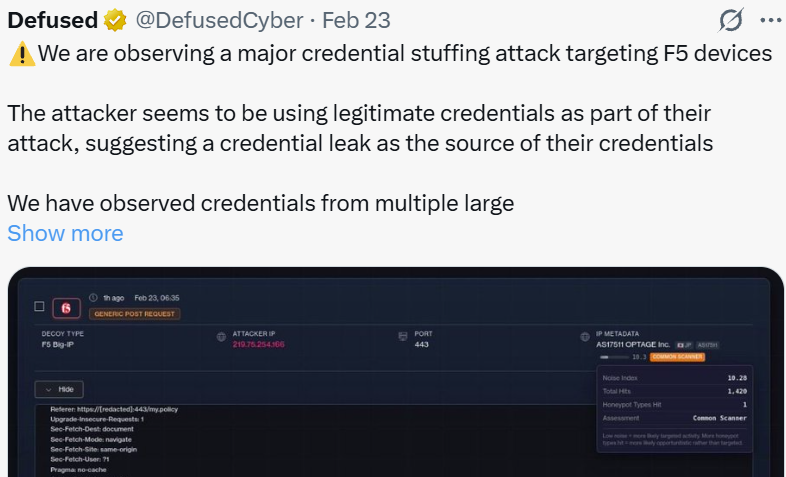
Recently, the cybersecurity community was alerted to a significant credential stuffing attack targeting F5 devices. The activity was first brought to light by threat intelligence group Defused Cyber, who noted that threat actors were attempting to access F5 infrastructure using seemingly legitimate corporate credentials.
We are observing a major credential stuffing attack targeting F5 devices
– Defused Cyber (@DefusedCyber) February 23, 2026
The attacker seems to be using legitimate credentials as part of their attack, suggesting a credential leak as the source of their credentials
We have observed credentials from multiple large corporations…
The screenshot accompanying the post showed a generic POST request captured by an F5 Big-IP honeypot, revealing an attacker attempting to pass email and password parameters. The source IP flagged in the attack was 219.75.254.166 (AS17511 OPTAGE Inc., Japan).
The Infostealer Connection: 77% Match Rate
Following this discovery, we reached out directly to Simo Kohonen, the founder of Defused Cyber, to dig deeper into the data captured by their honeypots. They graciously shared a sample of 70 unique email and password combinations that the threat actors attempted to use during the attack.
We ran these credentials against Hudson Rock’s global cybercrime database of Infostealer infections. The results were highly conclusive:
Out of the 70 credential combinations observed in the attack, 54 of them were directly matched to our Infostealer logs.
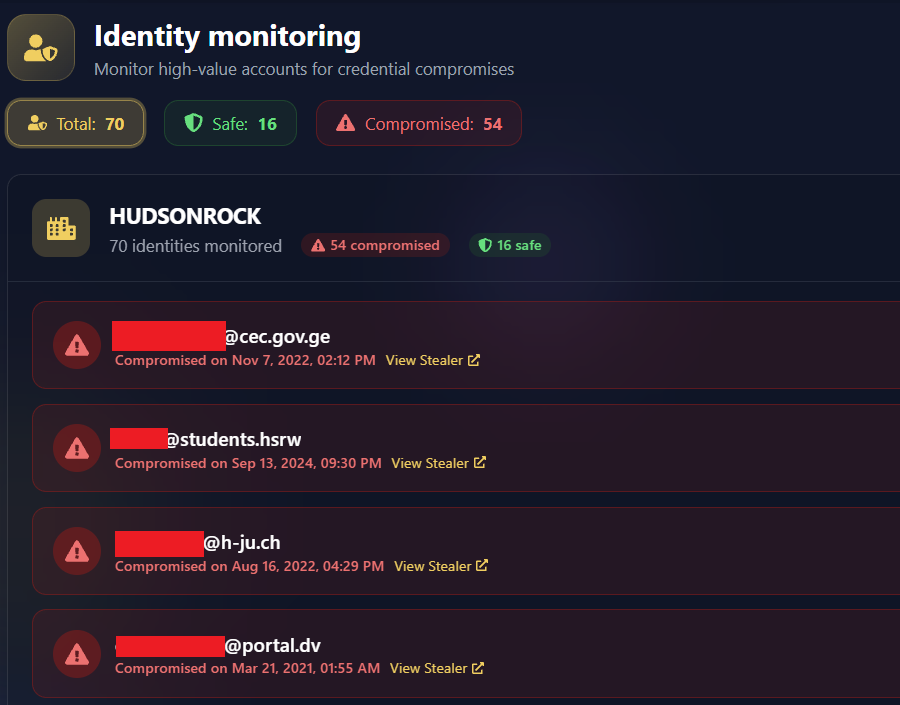
This means that over 77% of the credentials used in this specific campaign were harvested from machines infected with Infostealers. The threat actors were not using credentials explicitly stolen from F5 data breaches. Instead, they were relying on the opportunistic nature of Infostealers, taking corporate credentials previously used for internal portals (like ADFS, STS, and OWA) and “stuffing” them against external-facing F5 interfaces, hoping for password reuse or lack of MFA.
The Corporate SSO Bypass: Identity as the New Perimeter
A critical technical insight from our analysis is that the credentials found in the Hudson Rock database weren’t inherently “F5 passwords” – they were primarily ADFS (Active Directory Federation Services) and STS (Security Token Service) credentials.
The hackers aren’t looking for F5-specific passwords; they are using the keys to the kingdom that happen to work on the F5.
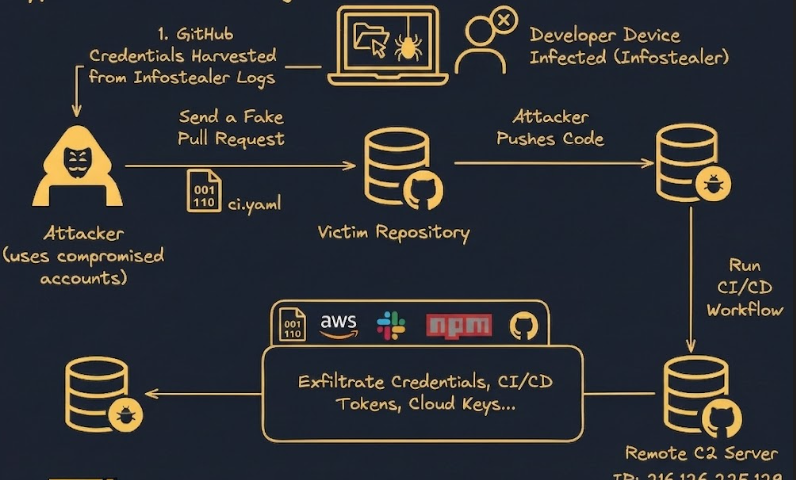
1. The Infection
An employee’s device is infected by an Infostealer. Master SSO and ADFS credentials saved in their browser are silently harvested.
2. The Marketplace
Raw infostealer logs are aggregated, filtered by valuable corporate domains, and sold to Initial Access Brokers (IABs) on the dark web.
3. The Front Door Bypass
Attackers use the harvested master credentials against corporate edge devices (like F5 BIG-IP) taking advantage of password functional equivalence.
4. Network Compromise
The perimeter is bypassed entirely. The attacker successfully authenticates into the corporate network—logging in rather than hacking in.
The threat actors are banking on functional equivalence. Because devices like the F5 BIG-IP often act as the front door for an organization, they are typically configured to accept the same master corporate credentials used for Windows logins, internal portals, and Corporate SSO.
This is part of a larger, systemic threat representing a “Log-to-Lead” pipeline. Valid credentials for SSO, ADFS, or VDI stored in a compromised browser are rapidly repurposed to brute-force sensitive edge infrastructure. In modern architectures, identity is the new perimeter. If a password for an ADFS portal is saved in a browser infected by an Infostealer, the firewall is effectively bypassed because the hacker is “logging in,” not “hacking in.”
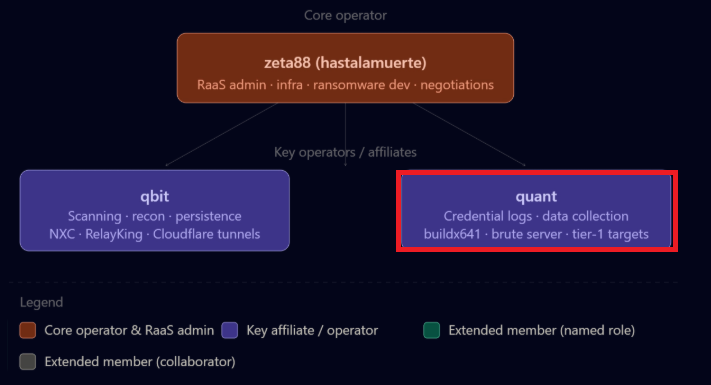
What we are observing is a highly industrialized supply chain: raw Infostealer logs are meticulously filtered by corporate domain, packaged, and sold to initial access brokers and attackers specifically looking for frictionless entry points into high-value corporate networks.
Targeted Organizations: A Look at the Compromised Data
The credentials deployed in this attack belong to employees across multiple large, multinational corporations and government entities. The threat actors essentially threw a massive list of high-value corporate credentials at the wall to see what would stick.
If hackers “throw a massive list” at many diverse targets, the statistical likelihood of finding at least one organization with valid credentials and no MFA, or an exhausted employee susceptible to MFA fatigue, is exceptionally high. In cybersecurity, this is a classic “low-effort, high-reward” technique; the attacker only needs to be right once, while the defenders must be right every single time.
Below is a mapping of some of the most notable organizations whose employee credentials were observed in this attack payload:
| Organization | Industry / Sector | Compromised Domain |
|---|---|---|
| Rolls-Royce | Aerospace & Defense | @ps.rolls-royce.com |
| Johnson & Johnson | Pharmaceuticals & Medical | @ITS.JNJ.com |
| Ericsson | Telecommunications | @ericsson.com |
| Deloitte | Professional Services | @deloitte.com |
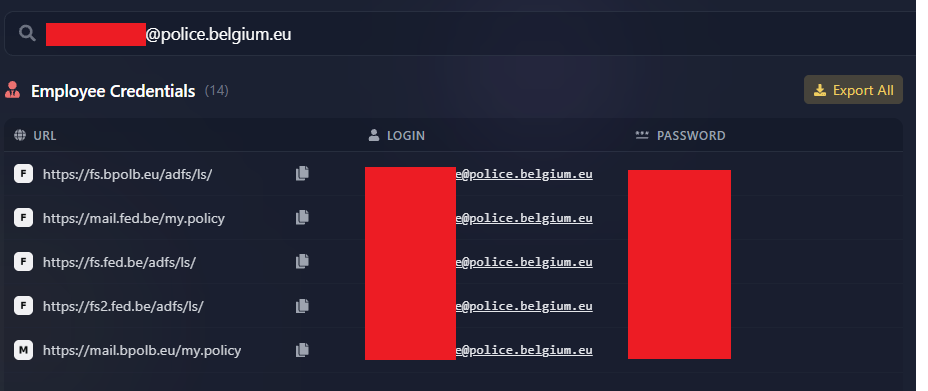
| Belgian Police | Law Enforcement | @police.belgium.eu |
| Queensland Police | Law Enforcement | @police.qld.gov.au |
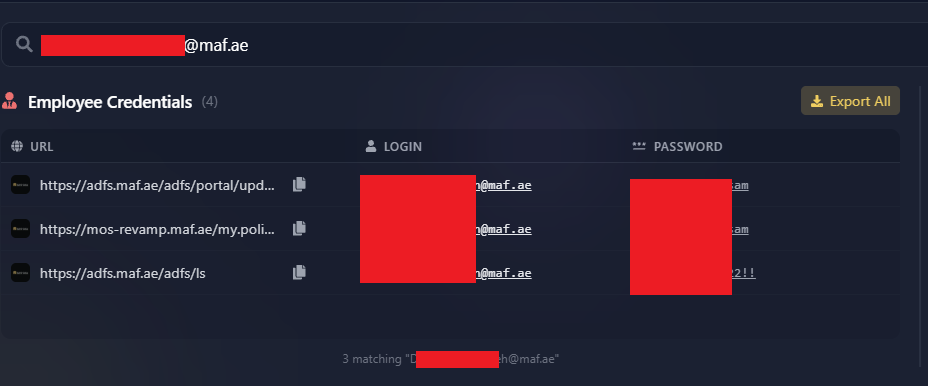
| Majid Al Futtaim (MAF) | Retail / Conglomerate | @maf.ae |
| Cellebrite | Digital Intelligence | @cellebrite.com |
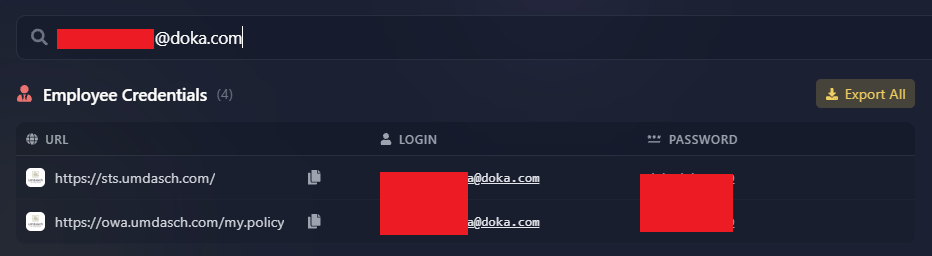
| Doka | Construction & Engineering | @doka.com |
| Turkish Ministry of Trade | Government | @ticaret.gov.tr |
Proof of Compromise
To provide further context, we extracted screenshots from our platform proving these exact credentials originated from Infostealer infections affecting these specific organizations. Below are visual confirmations of the compromised credentials for Doka, the Belgian Police, Ericsson, and Majid Al Futtaim:

The Attack Origin: Compromised Edge Devices
While the credentials themselves were sourced from Infostealers, the infrastructure used to carry out the attack adds another layer of complexity. Cybersecurity expert Daniel Card replied to the initial alert with crucial context regarding the source IP.
The IP is a Fortinet FW.
– Daniel Card (@UK_Daniel_Card) February 23, 2026
The attacker compromised an edge device and is using it to attack another edge device. Modern cyber ecosystem in a nutshell.
According to Shodan data, the source IP (219.75.254.166) actually hosts a Fortinet FortiGate-60E firewall from OPTAGE Inc. in Japan. The device has open ports 541/tcp and 10443/tcp and utilizes a self-signed SSL certificate.
This strongly indicates that the attacker is leveraging a compromised edge device (the Fortinet firewall) as a proxy to launch attacks against other edge devices (F5 Big-IP). This underscores an evolving, dual-threat landscape: attackers are combining the mass-harvested identities from Infostealers with the anonymizing power of hijacked edge infrastructure.
Conclusion
This incident is a textbook example of how initial access brokers and threat actors operate today. They are not hacking into networks in the traditional sense; they are simply logging in. By purchasing or scraping logs from Infostealer infections, attackers gain access to valid corporate credentials meant for ADFS or OWA, and ruthlessly stuff them into VPNs and F5 interfaces until they break through.
Organizations must realize that edge devices like F5 and Fortinet are under constant siege. Securing them requires not just patching vulnerabilities, but actively monitoring the dark web and cybercrime databases for compromised employee identities before they can be weaponized in credential stuffing campaigns.