Cracked software beats gold: new macOS backdoor stealing cryptowallets
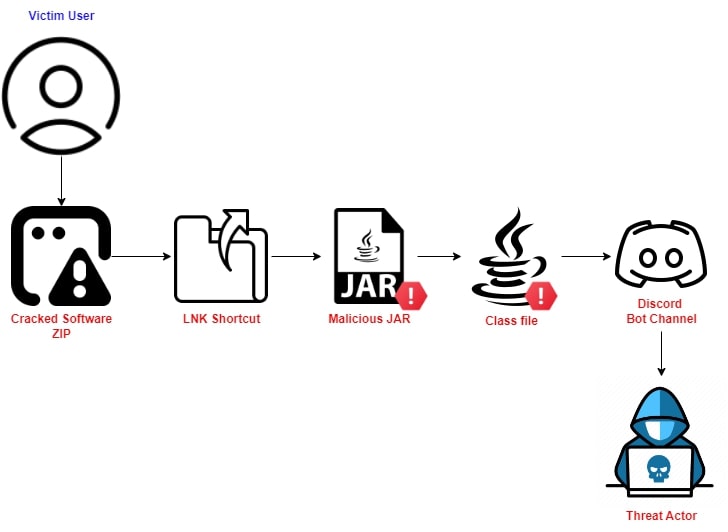
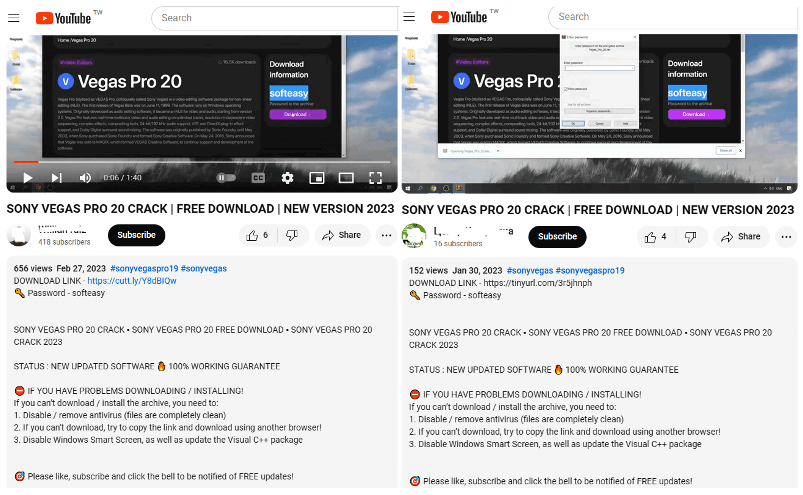
A month ago, we discovered some cracked apps circulating on pirating websites and infected with a Trojan proxy. The malicious actors repackaged pre-cracked applications as PKG files with…