Infected by GTA 5 Cheats: How an Infostealer Infection Unmasked a North Korean Agent
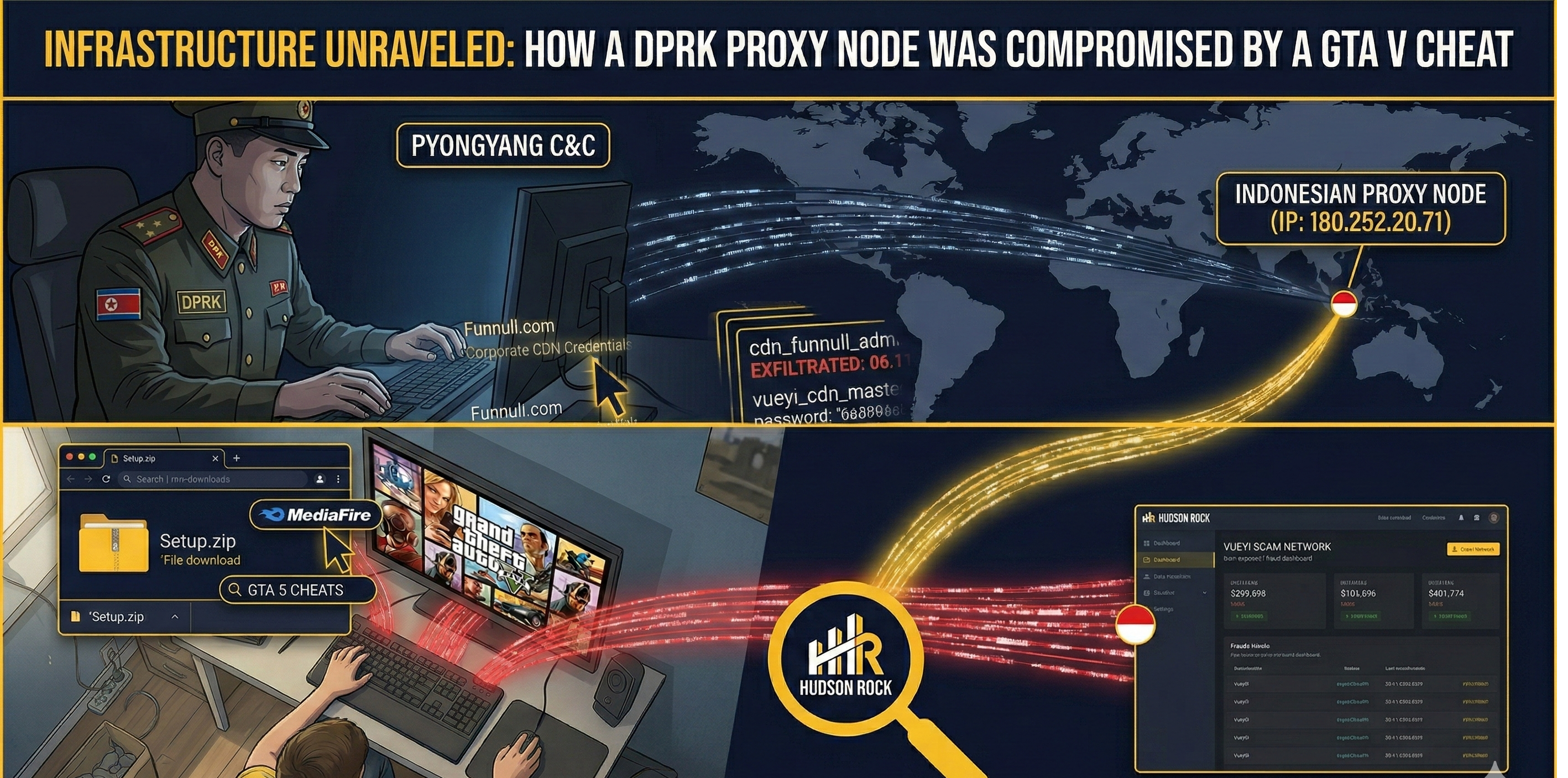
State-sponsored cybercrime is evolving. Foundational research by Kudelski Security, utilizing Hudson Rock’s extensive cybercrime database, recently mapped out how North Korean (DPRK) IT workers use proxy networks to infiltrate Western companies, secure remote jobs, and fund their regime. But what happens when one of these highly skilled operatives makes a catastrophic operational security mistake?
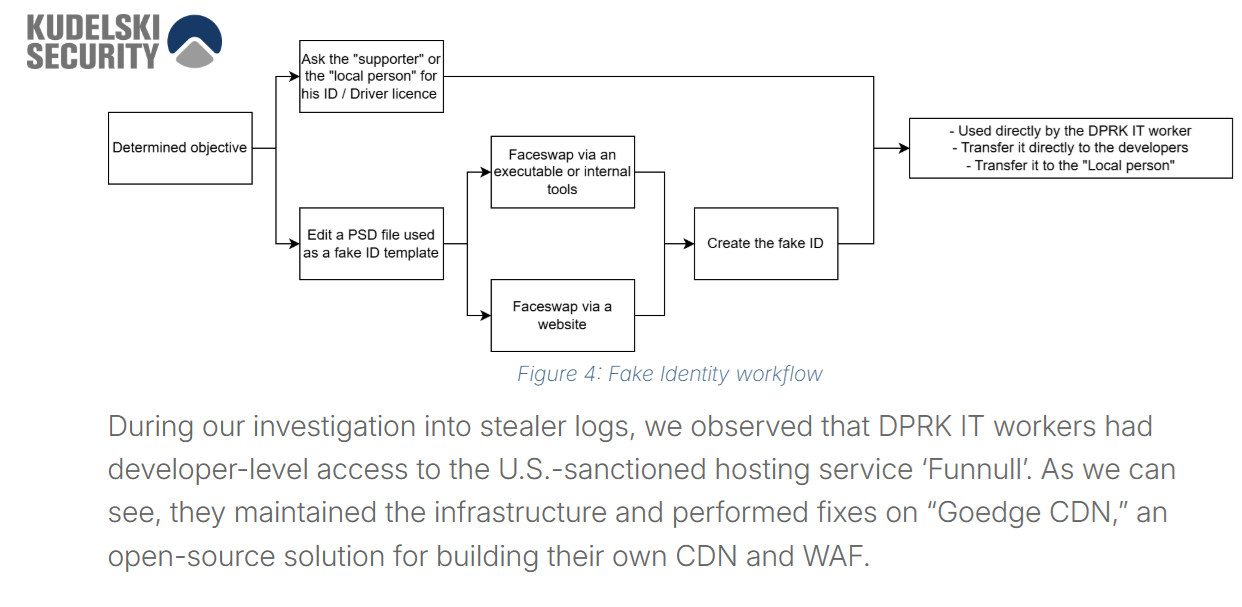
Image: Snippet from Kudelski Security’s foundational research on the DPRK Fake IT Worker network.
Using cybercrime intelligence data from Hudson Rock, we analyzed a machine belonging to a suspected DPRK IT worker that was accidentally infected with the LummaC2 infostealer. Instead of corporate credentials, this log contained the ultimate “smoking gun” exposing a previously undocumented Indonesian proxy node. Here is a look inside the digital life of a state-sponsored fraudster.
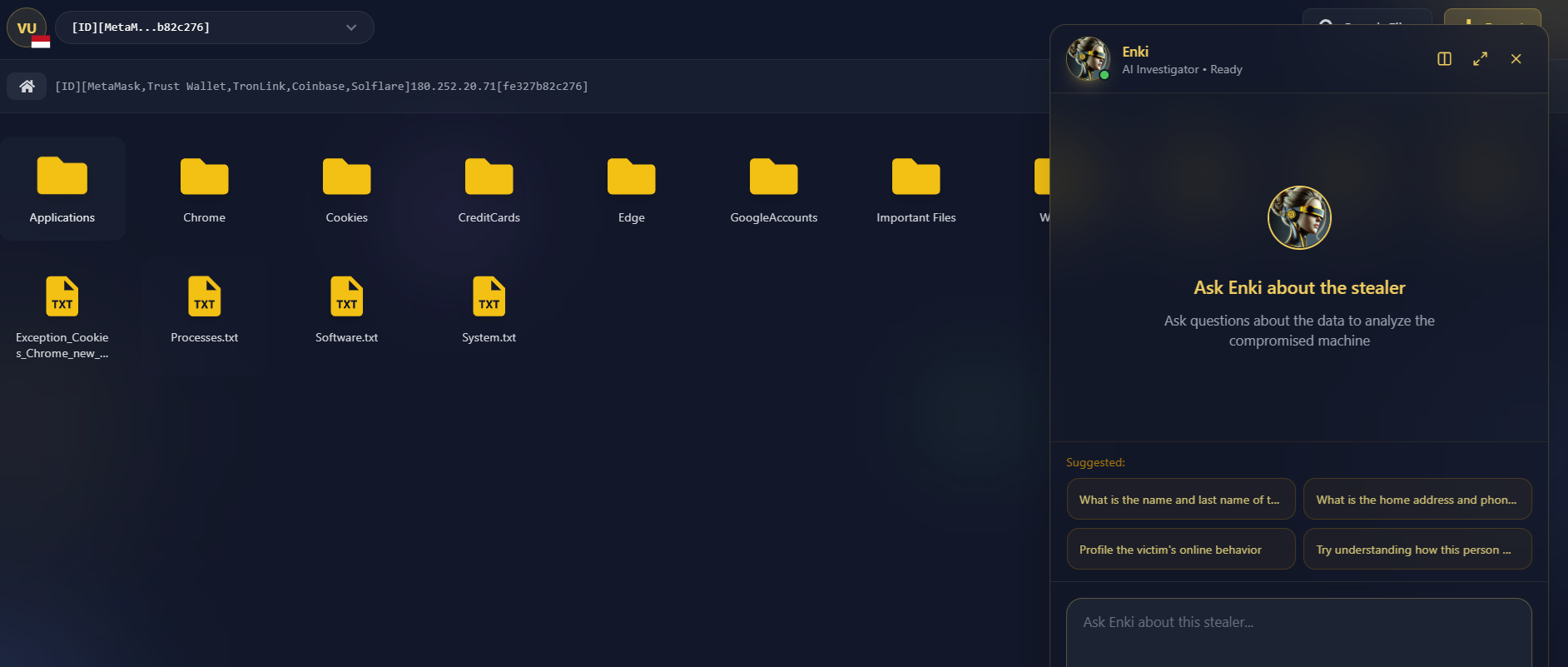
Image: Overview of the extracted files from the infected DPRK IT worker’s machine via Hudson Rock’s Cavalier platform.
The Catalyst: Tracking Sanctioned Infrastructure
The discovery of this specific proxy node was not a random coincidence. The investigation was triggered when researchers identified this infected machine within the Hudson Rock database because its exfiltrated logs contained corporate CDN credentials for funnull.com. As detailed in recent research by Silent Push on “infrastructure laundering,” services like Funnull are frequently leveraged by state-sponsored actors. Silent Push revealed how DPRK operatives systematically abuse these content delivery networks to mask the true origin of their malicious servers, allowing them to bypass geofencing and blend their activities into legitimate regional web traffic. Funnull and the broader network of DPRK IT workers utilizing this infrastructure laundering technique were recently the subject of major sanctions by the US Department of the Treasury. Finding these specific administrative credentials inside an infostealer log served as the exact starting point to investigate this computer and unravel its entire operation.
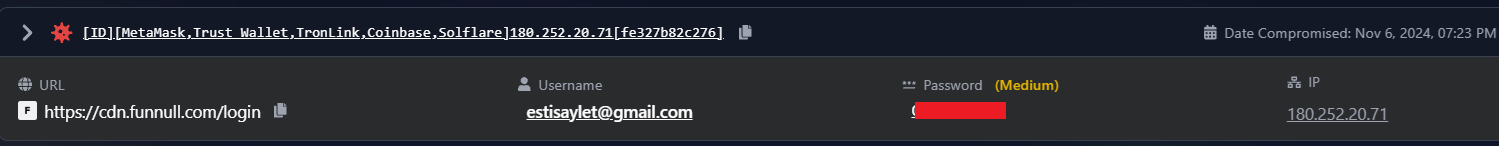
Image: Corporate CDN credentials for funnull.com found on the infected machine, which initiated the investigation into this node.
1. The Persona: An Indonesian Front with Chinese Roots
To operate across Western freelance platforms and global hosting providers, the operator utilized a massive matrix of synthetic identities. Operating primarily behind an Indonesian IP address (180.252.20.71) and the alias “Ikbal,” the operator maintained dozens of accounts across five distinct Chrome profiles and one Edge profile to meticulously compartmentalize their operations.
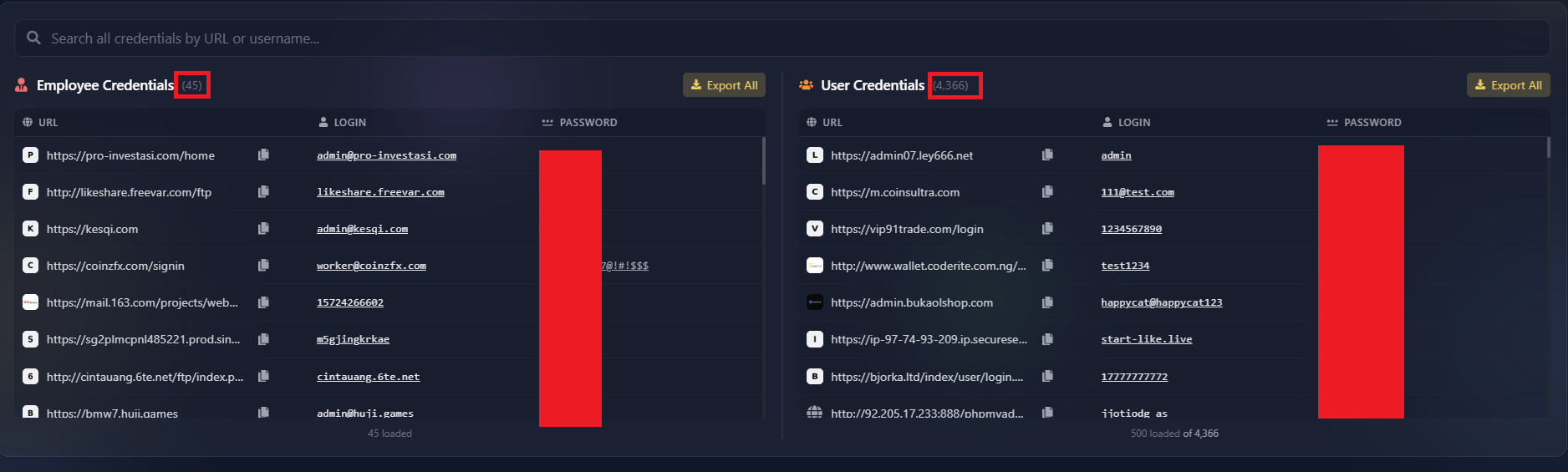
Image: A snapshot of the stolen credentials exposing the operator’s vast matrix of synthetic identities and administrative access.
| Primary Alias | Platform Usage Context |
|---|---|
| ikbal17 / ikbalgaming01 | Primary infrastructure access, GoDaddy domain management. |
| bacotburiq01 | Crypto exchange setups, Alibaba Cloud access. |
| estisaylet | Creating developer accounts, Web3 interfaces, AWS hosting. |
Despite using localized Indonesian internet slang for usernames, the operator’s search history revealed a striking duality. They seamlessly switched between their “Local Persona” (searching for Indonesian GTA V roleplay servers and local TikTok DJs) to a “Technical Persona” executing sophisticated searches for enterprise-grade crypto source codes using perfectly fluent Mandarin Chinese. This strongly indicates a collaborative effort between local facilitators and DPRK handlers.
2. The Toolkit: Deepfakes and Front Door Bypasses
How does a foreign operative pass live video interviews with Western HR departments? The installed software telemetry on the compromised machine provided the exact answer.
- OBS Studio & OBS-VirtualCam: This plugin routes pre-recorded videos or AI-generated deepfakes directly into software like Zoom or Teams, making the feed appear as a legitimate, physical webcam.
- Bandicam & VideoProc: Used to capture “proof of work” or manipulate video assets before injecting them into the virtual camera stream.
- IntelliJ IDEA & MongoDB Compass: Professional development environments confirming the operative is a high-level developer refactoring source code, rather than just a low-level worker.
The raw search history confirmed this intent. The operator was actively searching for “ChatGPT Generator Text to Video Maker” and “edit video di pc” (edit video on PC). They were actively generating and refining synthetic identities to bypass corporate verification gateways.
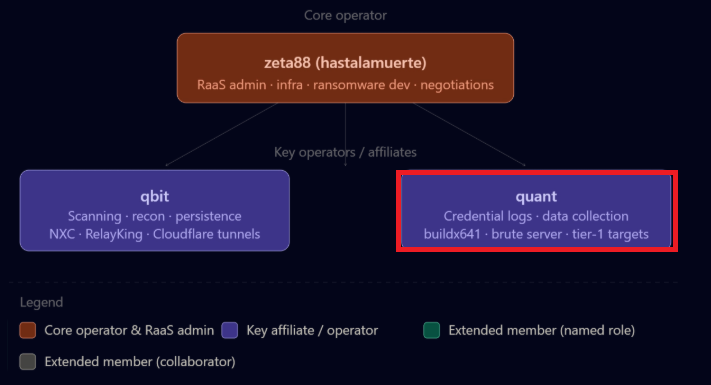
3. The Scams: Caught Red-Handed in the Logs
The operator wasn’t just performing freelance coding. The browser history files (History.txt and vueyi_search_history.csv) expose a massive, centralized administrative network under the moniker “Vueyi.” They were actively building an industrial-scale fraud empire.
Here is a direct look at what a state-sponsored scam developer searches for and actively manages on a daily basis:
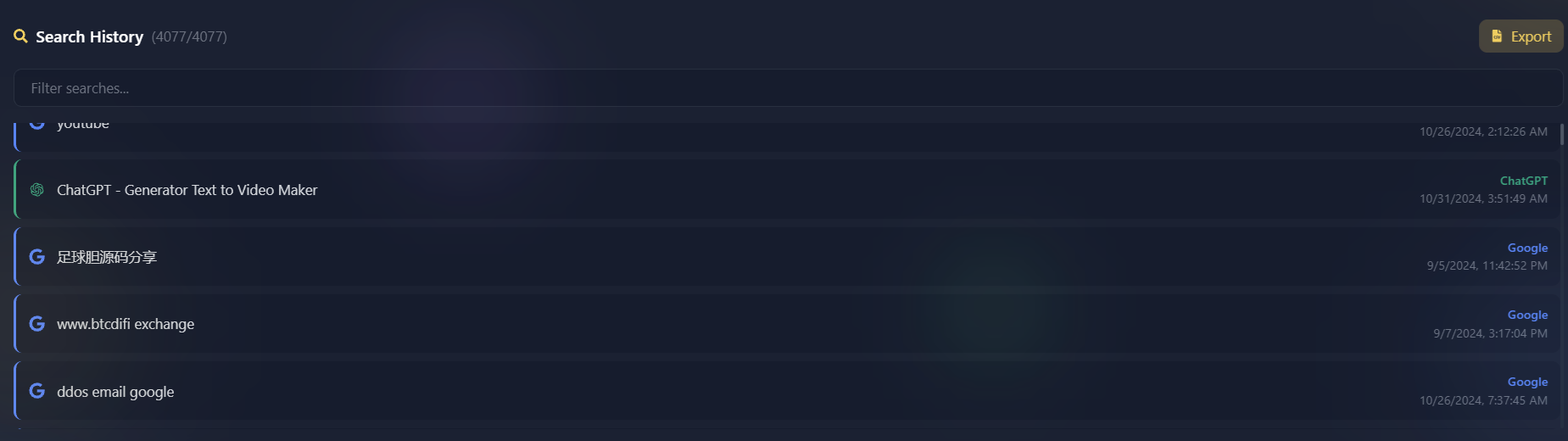
Image: Raw search queries extracted from the machine’s browsing history, highlighting the development of fraudulent crypto platforms and deepfakes.
These searches explicitly prove they were sourcing “steal-U” smart contracts designed to drain USDT from victim wallets and building high-volume “task scams” that spoofed major global brands. The password logs corroborated this, revealing direct administrative access to fake portals like https://grab-alibaba.com/admin/login and https://director.grab-amazon.com.
The infection didn’t just capture credentials; it exfiltrated 12 separate cryptocurrency wallet instances (MetaMask, Trust Wallet, TronLink, Solflare) carefully segregated across different browser profiles to prevent the cross-contamination of illicit funds. Investigators also uncovered a wallet.png file saved in the user’s pictures.
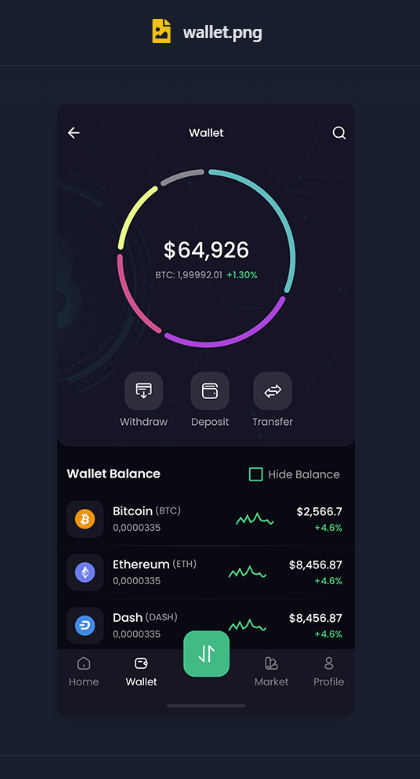
Image: A BTC wallet found stored directly on the infected machine, revealing a balance of $65,000 in illicit funds.
4. Operational Analytics: The 10 Primary Use Cases
Based on a comprehensive analysis of the 4,077 search queries in the exfiltrated history file, here are the 10 primary operational use cases for this proxy node, categorized by intent and frequency.
1. Industrial-Scale Scam Infrastructure Development
98% CONFIDENCEEvidence: Nearly 1,000 queries (25% of total volume) focused on full-stack development frameworks including SpringBoot, Vue.js, React, and ThinkPHP. Consistently searching for “backend + frontend” integration.
Context: This was the “workhorse” activity of the machine, used to build the scaffolding for fraudulent platforms.
2. Cryptocurrency Exchange Mimicry & Cloning
95% CONFIDENCEEvidence: Over 500 queries specifically targeting “交易所” (Exchanges). Specific terms included “Binance clone,” “Huobi UI Vue GitHub,” and “OKX.com clone.”
Context: The operative was actively “ripping” the UIs of major global exchanges to build phishing sites or fake trading platforms to harvest user credentials.
3. IP Seasoning (Behavioral Mimicry)
95% CONFIDENCEEvidence: Over 320 queries for localized Indonesian content: Al-Nassr football matches, Indonesian national team schedules, local TikTok DJs, and Islamic Friday prayer times.
Context: Generating “mundane” residential traffic allows the operative to “season” the IP address, bypassing fraud detection algorithms that flag static proxy traffic.
4. Identity Synthesis & Deepfake Orchestration
90% CONFIDENCEEvidence: Frequent searches for “ChatGPT – Generator Text to Video Maker,” “ElevenLabs voice cloning,” and “ChatGPT – Video Translator.”
Context: Used with OBS Studio/VirtualCam to create synthetic “human” identities and pass live video interviews with Western HR departments.
5. Smart Contract & Token Theft (Draining)
88% CONFIDENCEEvidence: Direct Mandarin searches for “多语言挖矿盗U秒U系统源码” (Multi-language mining “Steal-U” [USDT] system source code).
Context: Beyond just “working” for companies, the operative was procuring malicious smart contracts designed to drain USDT from victim wallets via “mining” scams.
6. Malware Procurement & Security Evasion
92% CONFIDENCEEvidence: Specific searches for “Craxs RAT,” “Free Lua Executors” (game hacks), and “menonaktifkan smartscreen windows 11” (disable Windows 11 SmartScreen).
Context: Hunting for remote access trojans (RATs) and ways to bypass local defenses—an activity that ironically led to their own infection.
7. Global “Task Scam” Administration
85% CONFIDENCEEvidence: History logs for administrative URLs such as grab-alibaba.com/admin and grab-amazon.com/director.
Context: Managing the backend of “task scams”—fraudulent portals that spoof major brands to trick users into “pre-paying” for tasks.
8. System Administration & Server Orchestration
85% CONFIDENCEEvidence: Debugging queries for Elasticsearch, aaPanel deployments, Linux daemon management, and server-side errors (e.g., bind() to [::]:80 failed).
Context: This was not a standard user; the computer was being used as a professional server node to host and manage the “Vueyi” scam empire.
9. Freelance Market Infiltration
80% CONFIDENCEEvidence: Searches for “官方开发人员职位空缺” (Official developer vacancies) and research into remote hiring platforms.
Context: Supports the “Fake IT Worker” persona, seeking legitimate remote developer roles in Western companies to establish a foothold and funnel salary back to the regime.
10. Illicit Marketplace Sourcing
90% CONFIDENCEEvidence: Consistent traffic to MediaFire, GitHub, and ymwu.com (a massive Chinese underground marketplace for illicit commercial website source codes).
Context: The operative relied on the cybercrime underground to source the “templates” for their fraudulent empire, avoiding the need to build anything from scratch.
5. The “Shared Activity” Smoking Gun
A crucial question arises: Was this Indonesian machine simply an unwitting victim of a random hack? The evidence strongly suggests otherwise. The machine’s owner was either a willing facilitator (a “laptop farm” host) or the North Korean operative themselves, deeply embedded in a local persona.
A typical remote hacker hides their tracks using incognito modes or dedicated profiles. However, the data extracted from Chrome Profile 1 shows a seamless, minute-by-minute transition between two vastly different lives within the exact same browser session.
State-Sponsored Work
- Managing the
mesta.cccrypto scam admin panel. - Searching in Mandarin for “16-language exchange” source code.
- Operating professional database tools (MongoDB Compass, aaPanel).
Personal Leisure
- Searching for Indonesian GTA V roleplay servers (“Indo Pride”).
- Watching “DJ Campuran” local TikTok and YouTube music mixes.
- Hunting for “FiveM Mod Menu” video game cheats.
This “Dual-Life” activity highlights a known DPRK operational tactic: IP Seasoning. By actively engaging in localized, mundane web browsing, the operative creates a legitimate residential behavioral footprint. This successfully tricks the fraud detection algorithms of Western platforms (like Upwork or Binance) which normally flag static or empty proxy IPs. The presence of professional database management software completely rules out the “average victim” theory.
6. The Ultimate OPSEC Failure: Cheating in GTA V
Infostealer infections remain the ultimate operational security failure for threat actors. But how did this highly skilled operative get infected in the first place?
Given the “shared activity” dynamic on the machine, the browsing history provides a highly ironic answer. It is incredibly likely that the local Indonesian facilitator (the person hired to host the laptop and “season” the IP by playing games) was the one who accidentally triggered the infection. On November 6, 2024, mere hours before the infostealer log was generated and exfiltrated, this local user navigated to MediaFire and downloaded two files while actively searching for “FiveM Mod Menu Hacks” and “Free Lua Executors” to cheat in a GTA V roleplay server:
TITLE: Setup
TIME: 06.11.2024 07:35:46
URL: https://www.mediafire.com/file/e86n68htfmac30x/Setup.zip/file
TITLE: Setup
TIME: 06.11.2024 08:20:00
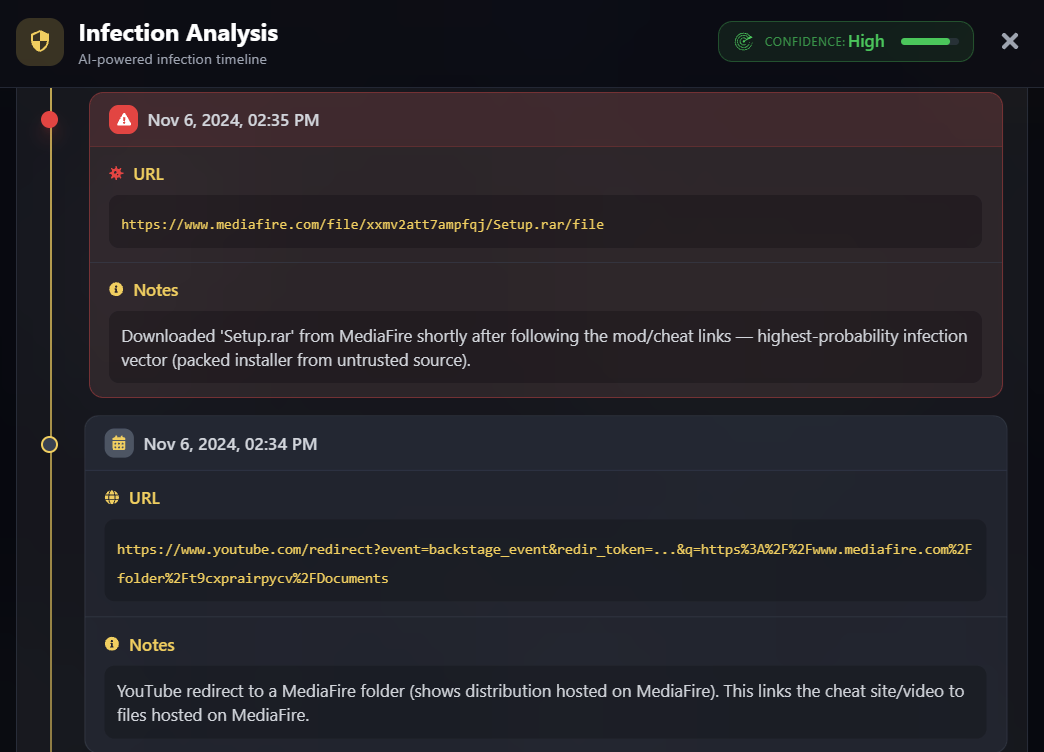
Image: AI infection timeline analysis showing the exact moment the operator downloaded the LummaC2 payload disguised as “Setup.zip” from MediaFire.
These Setup.zip and Setup.rar files are classic delivery mechanisms for the LummaC2 infostealer. In a staggering twist of irony, the North Korean operative’s meticulously constructed fraud empire wasn’t brought down by an advanced counter-intelligence operation or a complex network breach. It was completely undone because the local Indonesian facilitator they paid to host their proxy machine wanted free hacks for a video game.
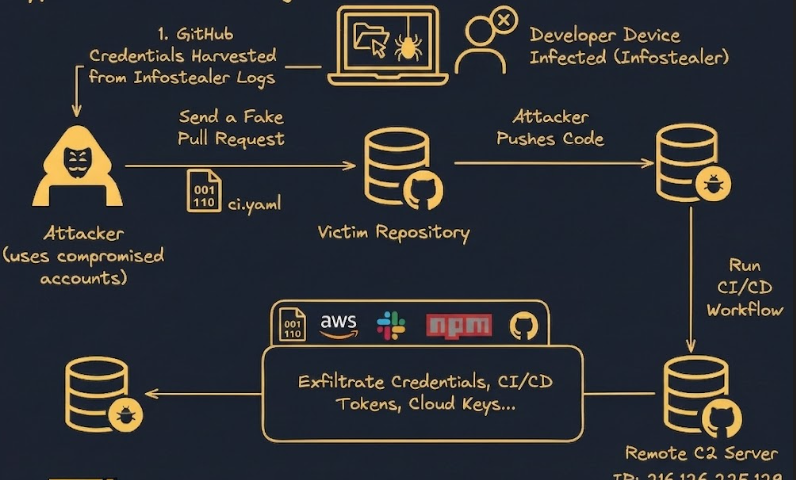
A Pattern of State-Sponsored Mistakes
This isn’t the first time Hudson Rock’s intelligence has pulled back the curtain on North Korean cyber operations. This discovery strongly echoes previous findings where an infostealer infection exposed a North Korean APT machine linked to one of the biggest cryptocurrency heists in history. Together, these incidents highlight a systemic OPSEC vulnerability within state-sponsored hacking groups: their reliance on the same underground ecosystems, cracked development tools, and shared infrastructure as everyday cybercriminals makes them highly susceptible to the exact same infostealer infections.
To help the security community better understand the scale and methodology of these operations, we have built a custom visualizer mapping the initial access and infection chain of this previous APT finding. This graph visualizes exactly how a single compromised endpoint unravels an entire state-backed network.
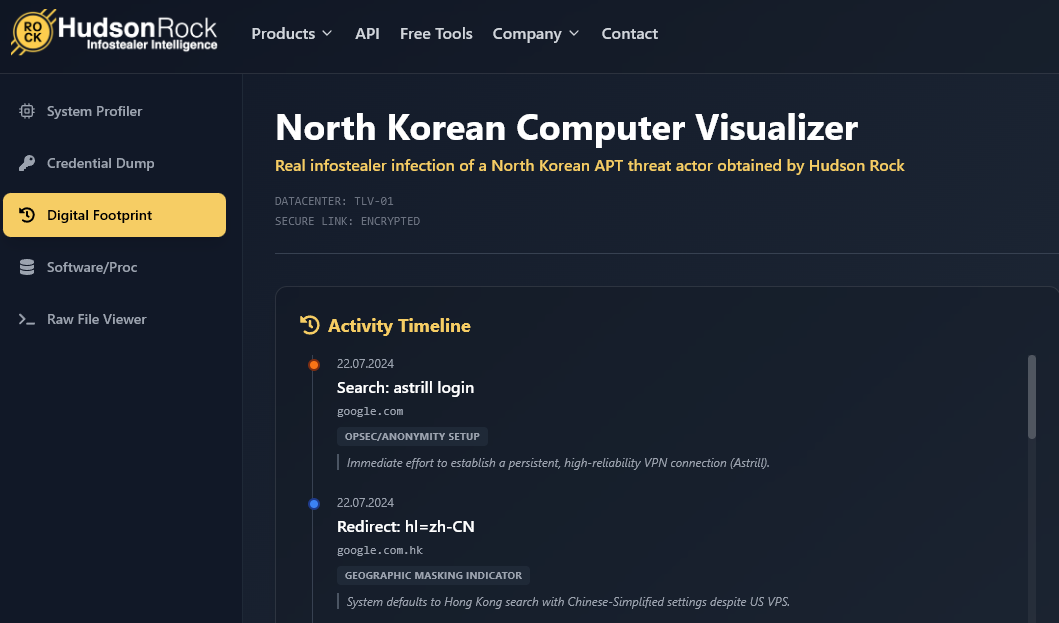
Image: Hudson Rock’s custom visualizer mapping the initial access and infrastructure of the previously discovered North Korean APT machine.
This data proves that identity is the new corporate perimeter. State-sponsored actors do not need to execute complex zero-day exploits if they can simply deepfake their way through a Zoom interview and walk right through the front door. By continuously analyzing cybercrime telemetry from sources like Hudson Rock, security teams can hunt for these exact behavioral markers (like aaPanel deployments on non-standard ports) and stop fraudulent insiders before they ever gain network access.
To learn more about how Hudson Rock protects companies from imminent intrusions caused by info-stealer infections of employees, partners, and users, as well as how we enrich existing cybersecurity solutions with our cybercrime intelligence API, please schedule a call with us, here: https://www.hudsonrock.com/schedule-demo
We also provide access to various free cybercrime intelligence tools that you can find here: www.hudsonrock.com/free-tools
Thanks for reading, Rock Hudson Rock!
Follow us on LinkedIn: https://www.linkedin.com/company/hudson-rock
Follow us on Twitter: https://www.twitter.com/RockHudsonRock