
Reddit Users Share What Really Happens When You Get Infected by an Infostealer
The Real Cost of Infostealers: Reddit's Frontline Horror Stories Reddit Users Share What Really Happens When You Get Infected by an Infostealer For most regular internet…
Article Type

The Real Cost of Infostealers: Reddit's Frontline Horror Stories Reddit Users Share What Really Happens When You Get Infected by an Infostealer For most regular internet…
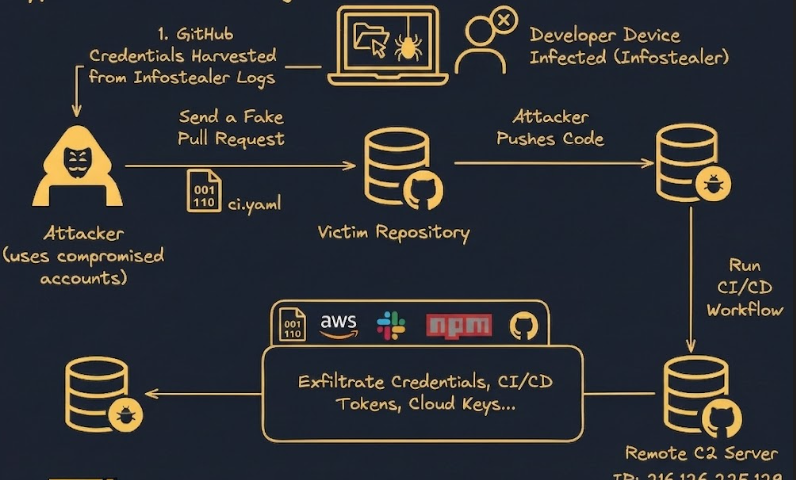
Megalodon: How Infostealers Spawned the 5,000+ Repo GitHub Supply Chain Attack Megalodon: Infostealers Just Spawned a 5,000+ Repo GitHub Supply Chain Attack The cybersecurity community was…
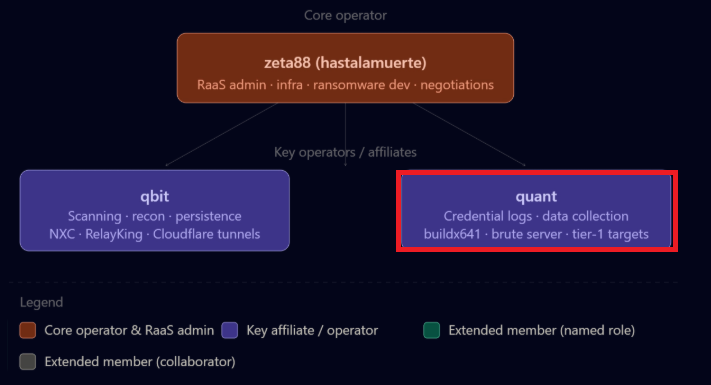
The Gentlemen Ransomware Group's Infostealer Playbook How The Gentlemen Ransomware Group Operates: A Blueprint Built on Infostealer Credentials A recent internal data leak from "The Gentlemen"…

The Infostealer-Ransomware Pipeline: A New Partnership with Ransomware.live The Missing Link: How Infostealers Fuel Ransomware Attacks (and Our New Partnership with Ransomware.live) In the ever-evolving landscape…
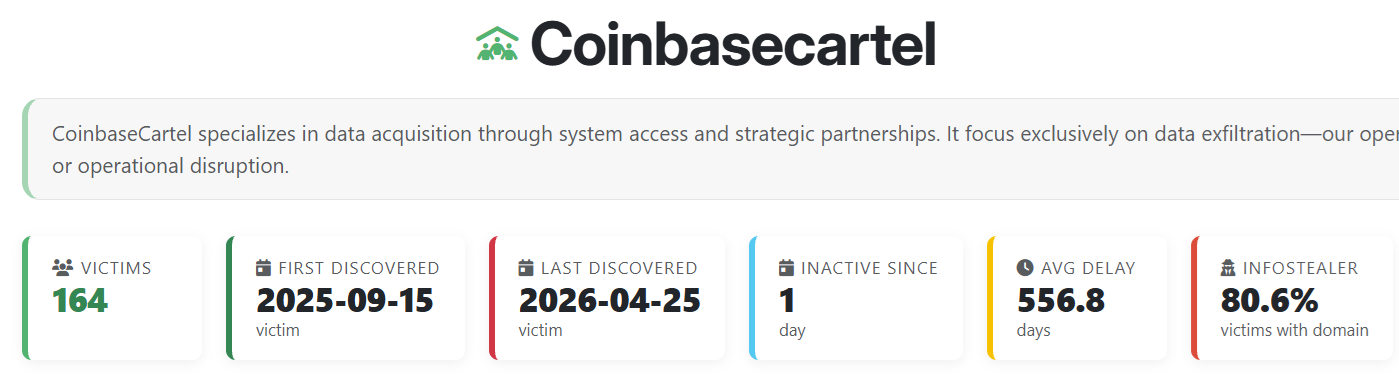
Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100+ Company Ransomware Spree Inside the Coinbase Cartel: How Infostealer Credentials Fueled a 100+ Company Ransomware Spree…

Original report - https://www.teiss.co.uk/news/news-scroller/korean-matchmaking-service-duo-fined-over-600000-over-sensitive-member-data-breach-17402 Korean matchmaking company Duo has been fined over £600,000 by the country’s data protection watchdog for failing to secure the data of…
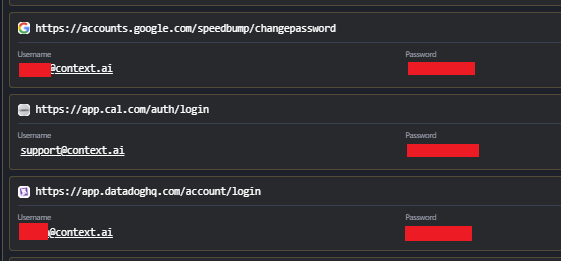
Breaking: Vercel Breach Linked to Infostealer Infection at Context.ai Breaking: Vercel Breach Linked to Infostealer Infection at Context.ai Following the recent confirmation of the Vercel breach,…
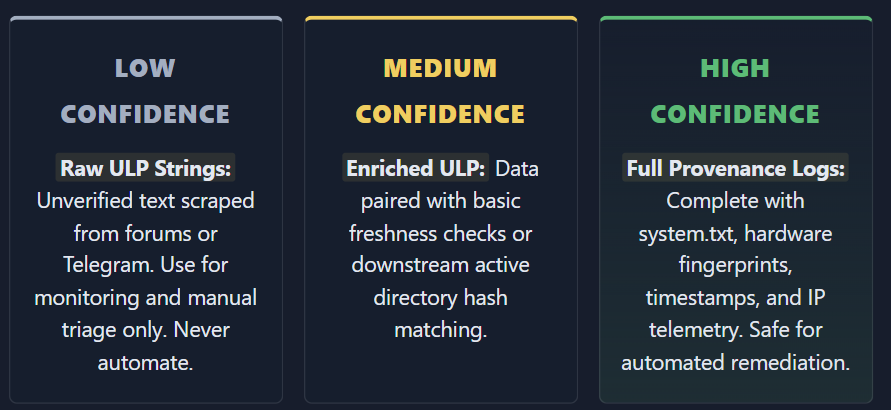
Infostealers ULP Data Is Burning Out SOC Teams and Killing Automation Infostealers ULP Data Is Burning Out SOC Teams and Killing Automation The cybersecurity industry has…
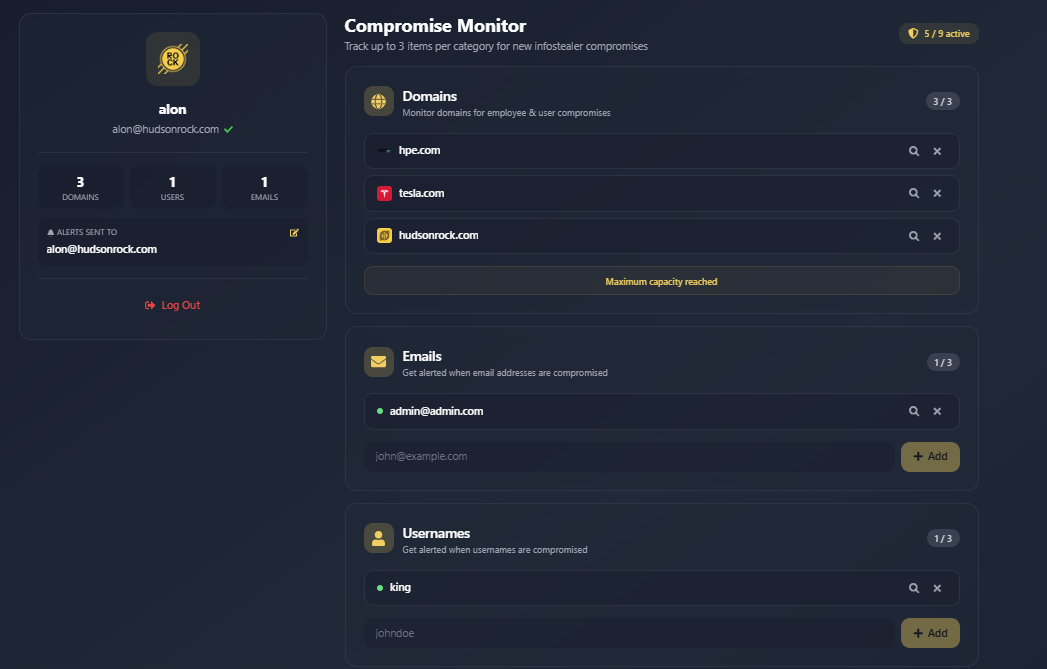
Free Infostealer Monitoring: Track Up to 3 Emails, 3 Domains, and 3 Usernames Free Infostealer Monitoring: Track Up to 3 Emails, 3 Domains, and 3 Usernames…
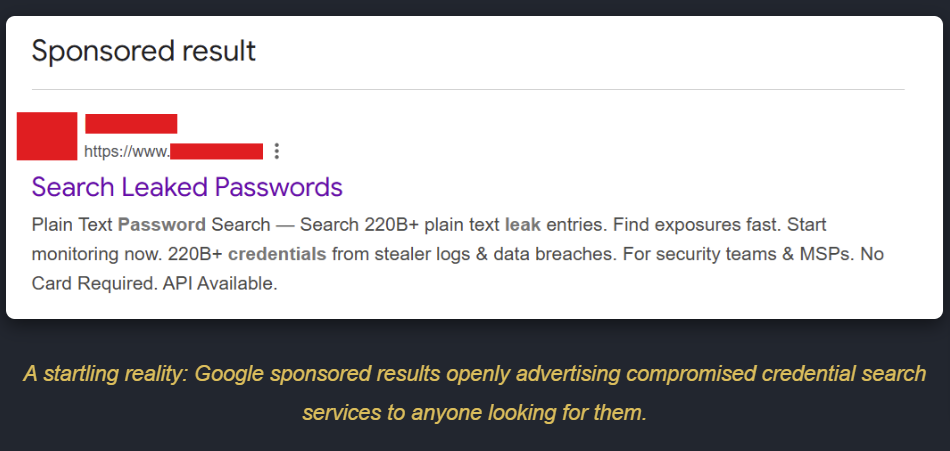
The New Era of Initial Access: How Infostealer Lookup Services are Changing Cybercrime We are currently witnessing a massive shift in how cyberattacks begin. Infostealer lookup…
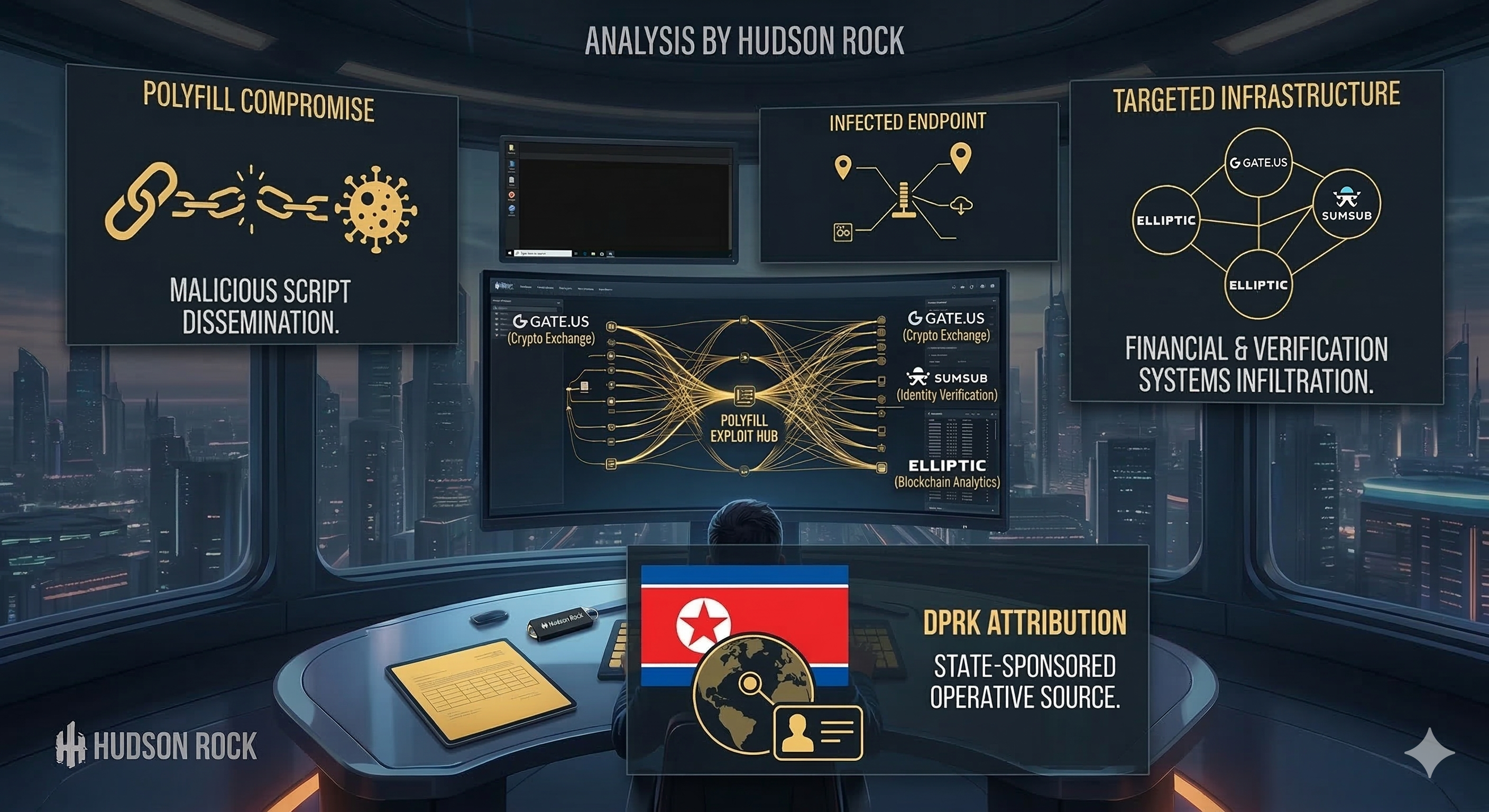
How One Infostealer Infection Solved a Global Supply Chain Mystery and Unmasked DPRK Spies in U.S. Crypto. Researcher & Law Enforcement Notice: Hudson Rock welcomes researchers…
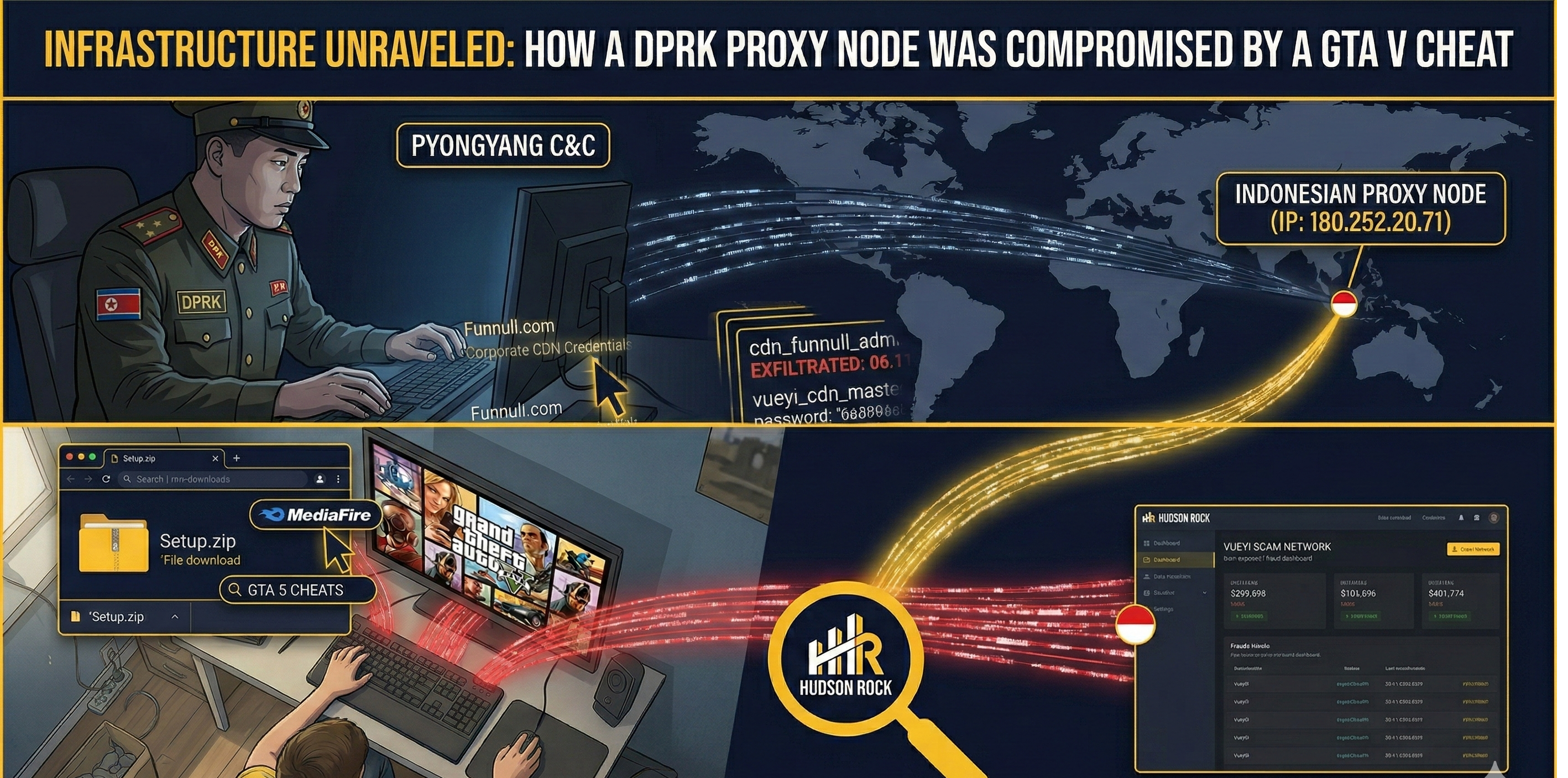
Infected by GTA 5 Cheats: How an Infostealer Infection Unmasked a North Korean Agent State-sponsored cybercrime is evolving. Foundational research by Kudelski Security, utilizing Hudson Rock's…